Knoxville is home to multiple famous institutions, such as the University of Tennessee, the Tennessee Valley Authority (TVA), and Dolly Parton. Visually, you know you are in Knoxville when you see The Sunsphere, a 23-meter gold-colored glass sphere sitting atop an 81-meter tall tower of steel. The monument, created for the 1982 World's Fair and in the spirit of celebrating advancements in energy, watched over us as we gathered to celebrate advancements in cybersecurity at BSides Knoxville 2024.
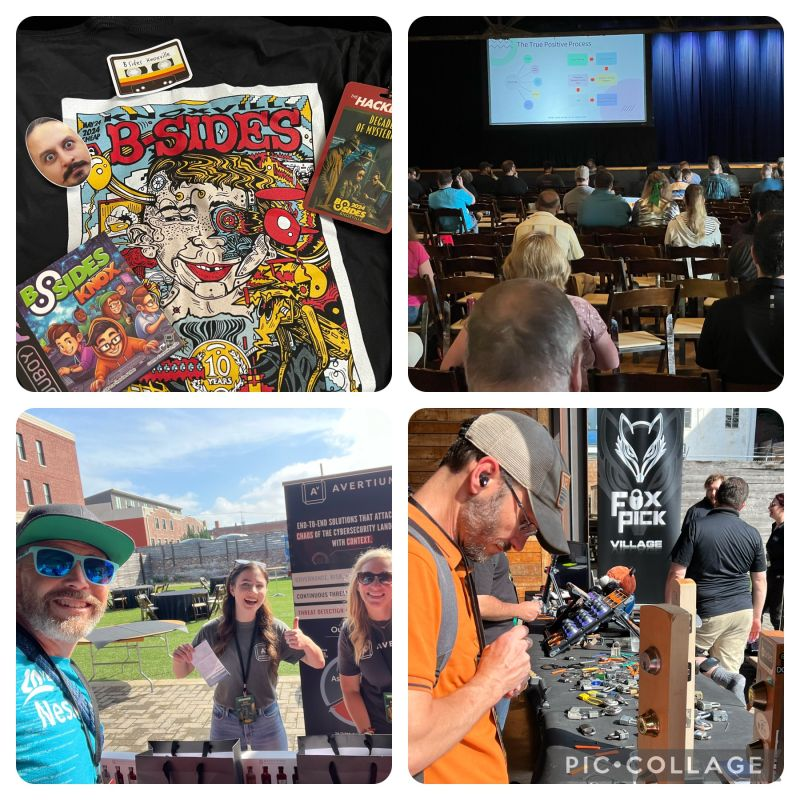
This year marked the 10th anniversary of this Tennessee-based BSides, and it was the biggest one yet. Over 400 attendees gathered to exchange knowledge, share experiences, and celebrate a decade of cybersecurity innovation. It would be hard to cover all the sessions across two speaking tracks, the lock pick pillage, the remote control robot hacking, and all the other little things that went into this event at the Mill and Mine. Here are just a few of the highlights.
Context is king when it comes to vulnerability management
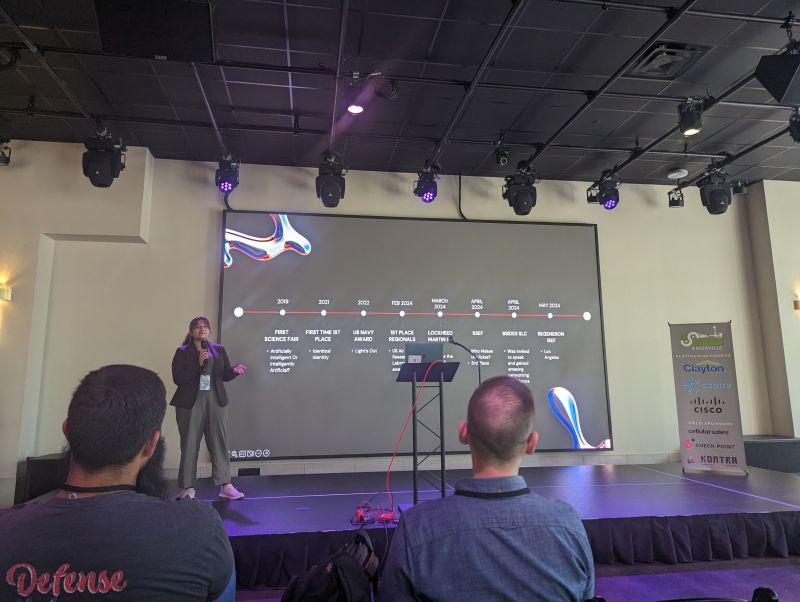
One of the younger presenters at any BSides, Meghna Vikram, a high school junior, presented her research findings in her session, "Who Makes the Rules?" She walked us through her efforts to leverage machine learning to fix vulnerabilities in JavaScript code in a more thorough way.
Her first step was to find a vulnerability analysis tool with output in an easy-to-manipulate format. She settled on a static analysis tool that produces YAML, a format defined by indentation that is easy for machines and humans to read. Her hypothesis was that while most SAST tools did provide generally valuable findings, the version she was using stopped short of giving specifics about how the vulnerability could be introduced.
For example, out of the box, the tools she ran showed a cross-site scripting (XSS) vulnerability present, but further research into the vulnerability database showed over 39000 ways that XSS could have been introduced. While it is helpful to know the vulnerability is present, she is working on a tool that shows exactly how each one was introduced into the code.
Meghna said she was surprised that after multiple passes at prompt training and experimentation, the AI she was relying on, ChatGPT, began to give deeper context around each issue and even examples of what the affected code would look like. While her research is in the early stages, it shows clear promise that AI-assisted security tools will play a role in training and giving developers a helping hand with their work.
Elementary, my dear cybersecurity professional!
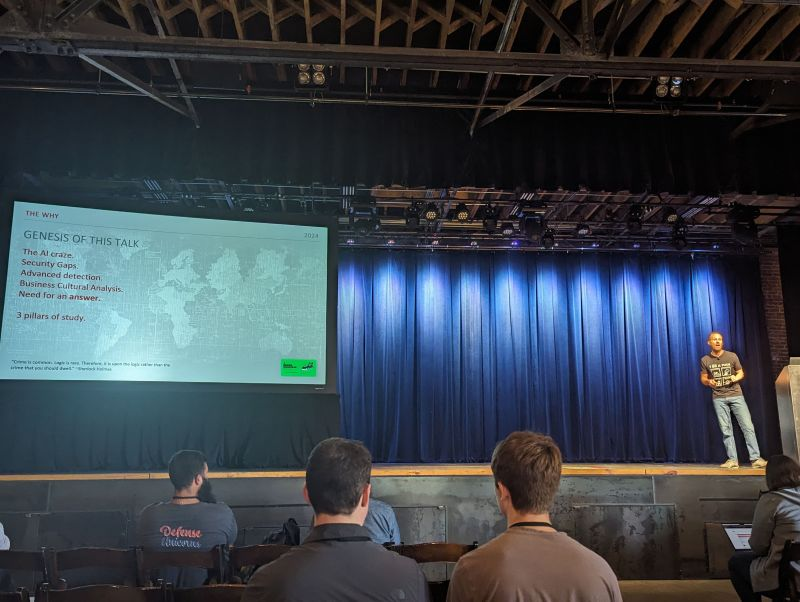
Very few times has a speaker fully leaned into the overall tone of a conference as Joshua Jones, Senior Compliance Consultant at Contextual Security Solutions, did with his Sherlock Holmes-themed talk "The Compromise of the Baskervilles: Holistic Testing in the "Automagic" Era." Not only did Joshua work in many a great quote from Sir Arthur Conan Doyle's classic cannon of work, but he also explored AI's role in security testing and the importance of getting the basics right.
Joshua started by walking us through history, from the Trojan Horse to the use of the Enigma machine in World War 2, to illustrate how security has evolved over time. Any tool, whether it involves AI or not, ultimately requires human oversight and strategic deployment. Defenders need to understand the nuances of the systems they protect, and AI should be seen as a means to bolster defenses, not as a standalone solution.
Drawing parallels to the classic detective story "The Hound of the Baskervilles," Joshua showed how Watson played a role similar to that of AI, performing the menial data collection tasks that allowed Holmes, or us, to step in at just the right moment and crack the case. AI, like Watson, can play a pivotal role but lacks the self-awareness to make the needed conclusions or take the needed actions. He wrapped up by saying that while AI changes the "how" of security, the "why" remains rooted in fundamental human values of protection and resilience.
To understand the history of hacking, you must understand 'phreaking'
The always-colorful Matt Scheurer, ThreatReel podcaster and VP of Security at a major US organization, took attendees on a nostalgic journey through the history of telephony and its intersection with hacking in his session, "Lies, Telephony, and Hacking History." Bringing along a suitcase filled with various bits of tech from the last 60 years, he walked us through a history of telephone systems and how the subculture of phone phreaking evolved.
The talk started with how we went from switchboards to dial tones and how ingenious hackers explored and exploited these systems. He said in those early days, the scene was driven by a thirst for knowledge, mischief, and the desire to make free calls, especially because in the 1970s and 80s, long-distance calls could cost upwards of $1.00 per minute. Along the way, he showed off his collection of tools, including an acoustic coupler as seen in the movie War Games, a "blue box" that generated 2600Hz tones to let people make long-distance calls for free, and some other interesting gear that allows a person to tap directly into phone lines.
Matt also discussed modern telephony abuse, including vishing (voice phishing), SMiShing (SMS phishing), and the dangers of mobile SIM swapping. The techniques attackers use today have been evolving for decades; while technology has changed, the principles of social engineering and exploitation remain relevant. We must stay vigilant in securing communication systems, as they are the backbone of our IT systems.
Community and collaboration in the era of AI
While many of the talks at BSides Knoxville spotlighted the role of AI, overall, the theme of holistic security, getting the basics right, shined through as the focus. Your author gave a talk about the importance of elevating security awareness across all teams throughout the organization and the role security champions can play in keeping us all secure at every level.
While the tools keep on changing, the mission and the core ideas remain constant. BSides Knoxville 2024, in its 10th year, celebrated a vibrant and dynamic cybersecurity community. It was a great day to look at the past, understand where we came from, and collectively discuss the challenges we see on the horizon. Fortunately, one of the things we can all look forward to is more BSides in the future. We hope to see you at your local one soon.