Not all leaked secrets carry the same risk. A leaked credential attached to a read-only logging job is more of a hygiene issue. The same credential attached to an AdministratorAccess role hands an attacker complete control of the account. Treating both incidents identically in the queue wastes responder time on the first and delays action on the second.
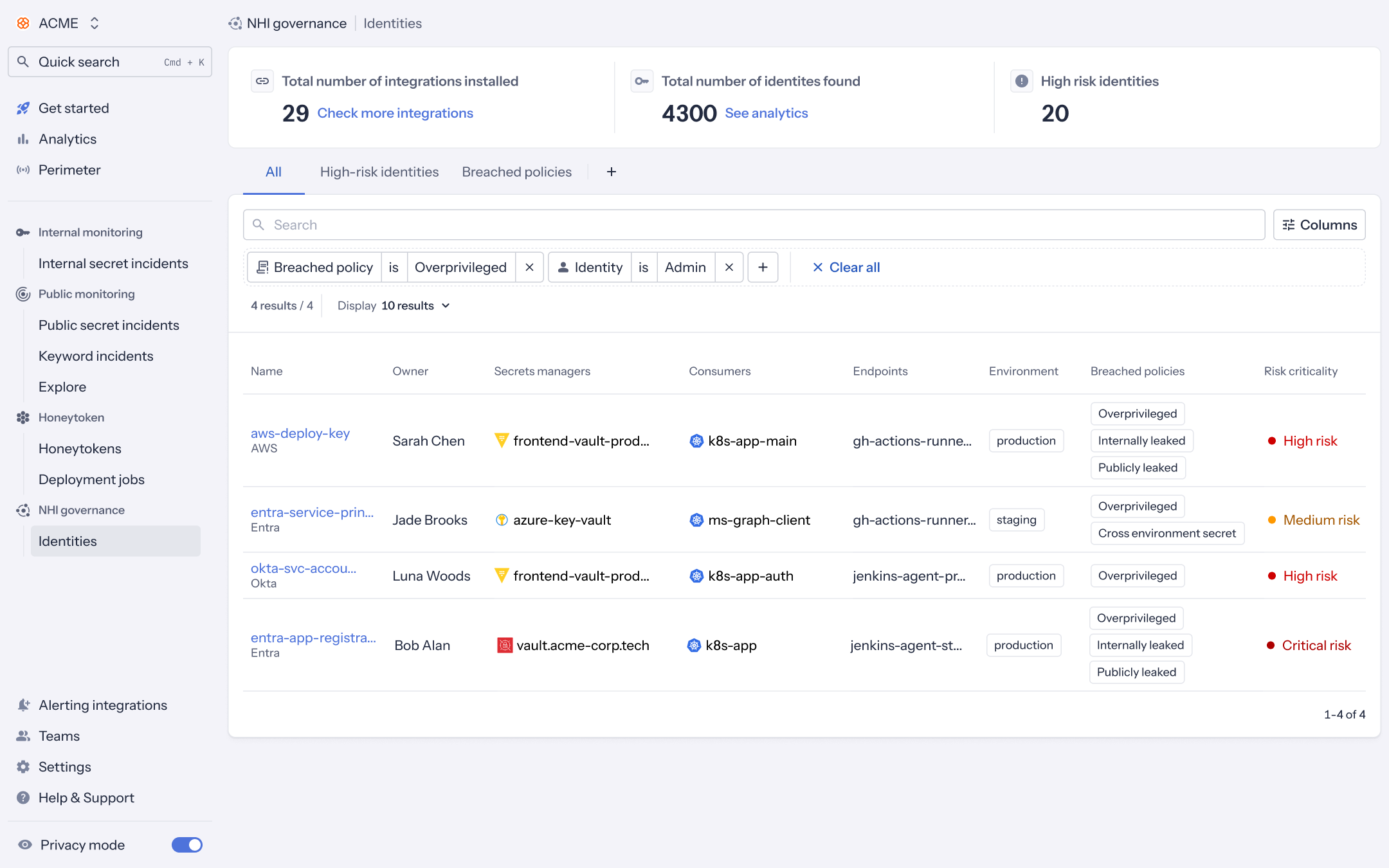
GitGuardian's latest NHI Governance release introduces privilege context as a first-class signal in the platform. The system now identifies which machine identities hold admin-level rights, surfaces those that have accumulated more permissions than they actually use, and automatically escalates the severity of incidents landing on those high-impact identities. Your remediation queue starts to reflect the real blast radius of each finding.
The missing dimension in NHI risk
Most security teams have spent the last few years getting a grip on where their non-human identities live. Service accounts, OAuth apps, CI/CD tokens, IAM roles, and agentic AI workloads now sit inside inventories that were unimaginable three years ago. The OWASP Top 10 for Non-Human Identities formalized the obvious risk patterns, including leaked secrets, reuse, long-lived credentials, and broken offboarding.
Inventories still lacked one further dimension: the blast radius of each identity. An overprivileged NHI amplifies every other risk attached to it. A reused secret on a global admin account exposes the entire tenant. Recognizing that distinction at scale used to require manually crawling through IAM policies, directory role assignments, and custom permission sets. That work struggles to keep up across thousands of identities and multiple clouds.
Customer conversations repeatedly surfaced the same asks: visibility into orphaned and overprivileged accounts, real-time tracking of agent permissions, and a way to detect when a workload sits on more access than its job requires. AI agents now connect to trading systems and production data stores, raising the cost of unanswered privilege questions every quarter.
The Admin badge
When NHI Governance maps the permissions attached to an identity and finds an admin or equivalent role, that identity now carries an explicit "Identity level: Admin" badge in the inventory and detail view. Detection runs on well-known role and policy markers across AWS IAM, Microsoft Entra, and Okta.
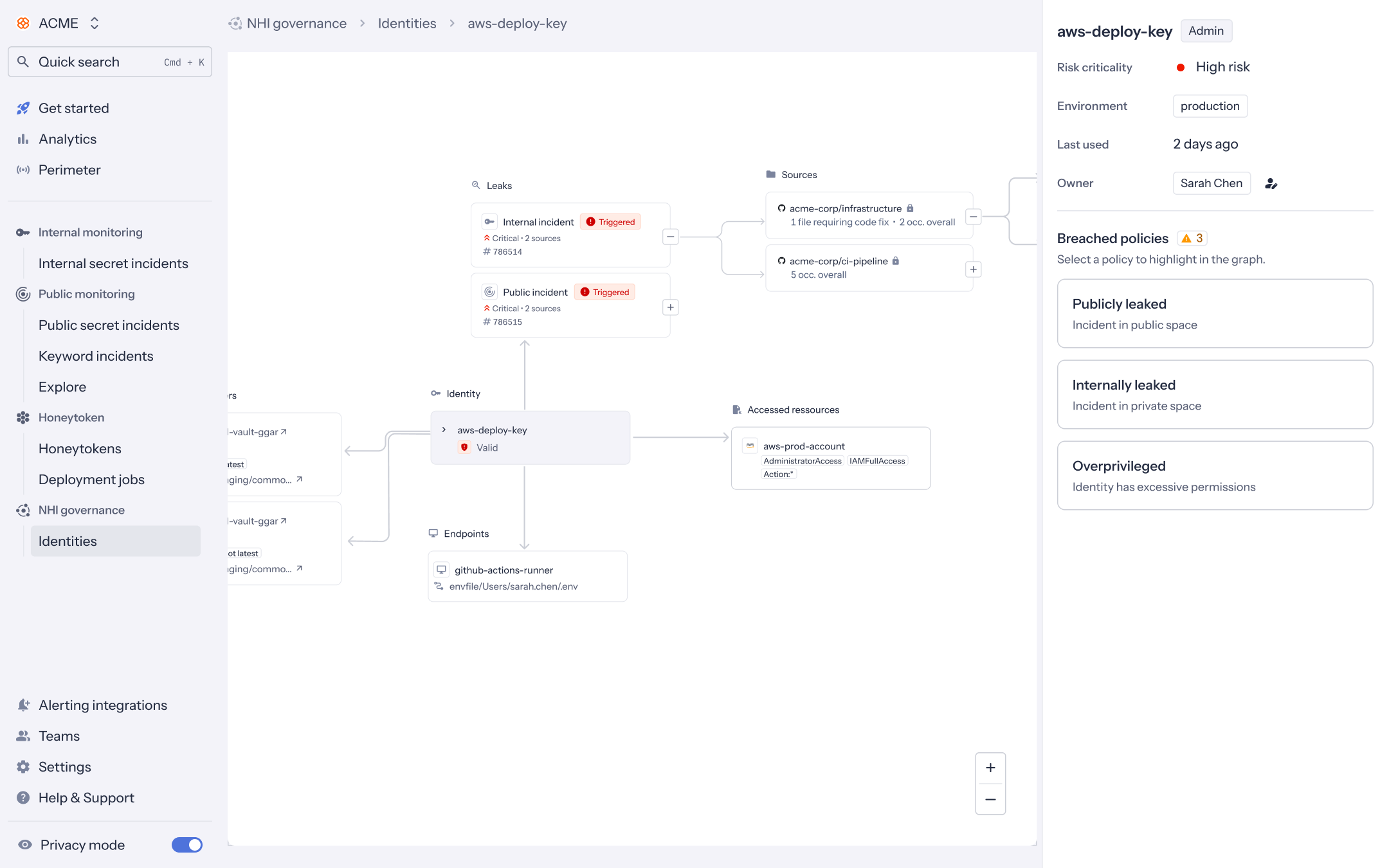
AdministratorAccess, IAMFullAccess, and wildcard action permissions visible on the linked production account.AWS coverage surfaces managed policies such as AdministratorAccess, PowerUserAccess, and IAMFullAccess, alongside inline statements that grant Action: * on Resource: *.
Entra coverage spans directory roles like Global Administrator, Privileged Role Administrator, and Application Administrator, plus Azure RBAC roles such as Owner and Contributor, and high-privilege Microsoft Graph permissions like RoleManagement.ReadWrite.Directory.
Okta detection covers the built-in Super Admin role and custom admin role assignments.
The badge appears wherever the identity is listed, giving security and platform teams a single visual signal that a leak, a reused key, or a broken offboarding event sits on top of full account-level access.
The Overprivileged Identity policy
Admin status answers a binary question. Overprivilege sits in the messier middle, where identities accumulate permissions far beyond what their workloads actually require. The new Overprivileged Identity policy flags permission sets that have drifted directly. Detection covers wildcard actions, sweeping resource scopes, and large bundles of high-privilege graph grants. The effect over time is a steady push back toward the least privileged for the long tail of NHIs that grew bigger one ticket at a time.
Risk criticality that reflects the blast radius
When a policy breach affects an admin NHI, its severity is automatically raised one level, with critical as the maximum. For example, an internally leaked secret was previously registered as high and on an admin identity; it now registers as critical. An overprivileged finding on a non-admin identity stays at medium. On an admin identity, the same finding moves to high. Improper offboarding of an admin identity is rated critical rather than high.
The model is layered. A base severity per policy breach forms the foundation, with modifiers stacking on top for admin status and, where relevant, production exposure. The dashboard now aligns with how seasoned incident responders naturally triage.
A worked example
Imagine GitGuardian finds an internal secret leak in a private repository. The secret belongs to an Entra application registered with RoleManagement.ReadWrite.Directory, a permission that allows the app to grant itself any directory role. Without a privileged context, the incident would surface as a high-severity internal leak, sandwiched among hundreds of similar findings on read-only services.
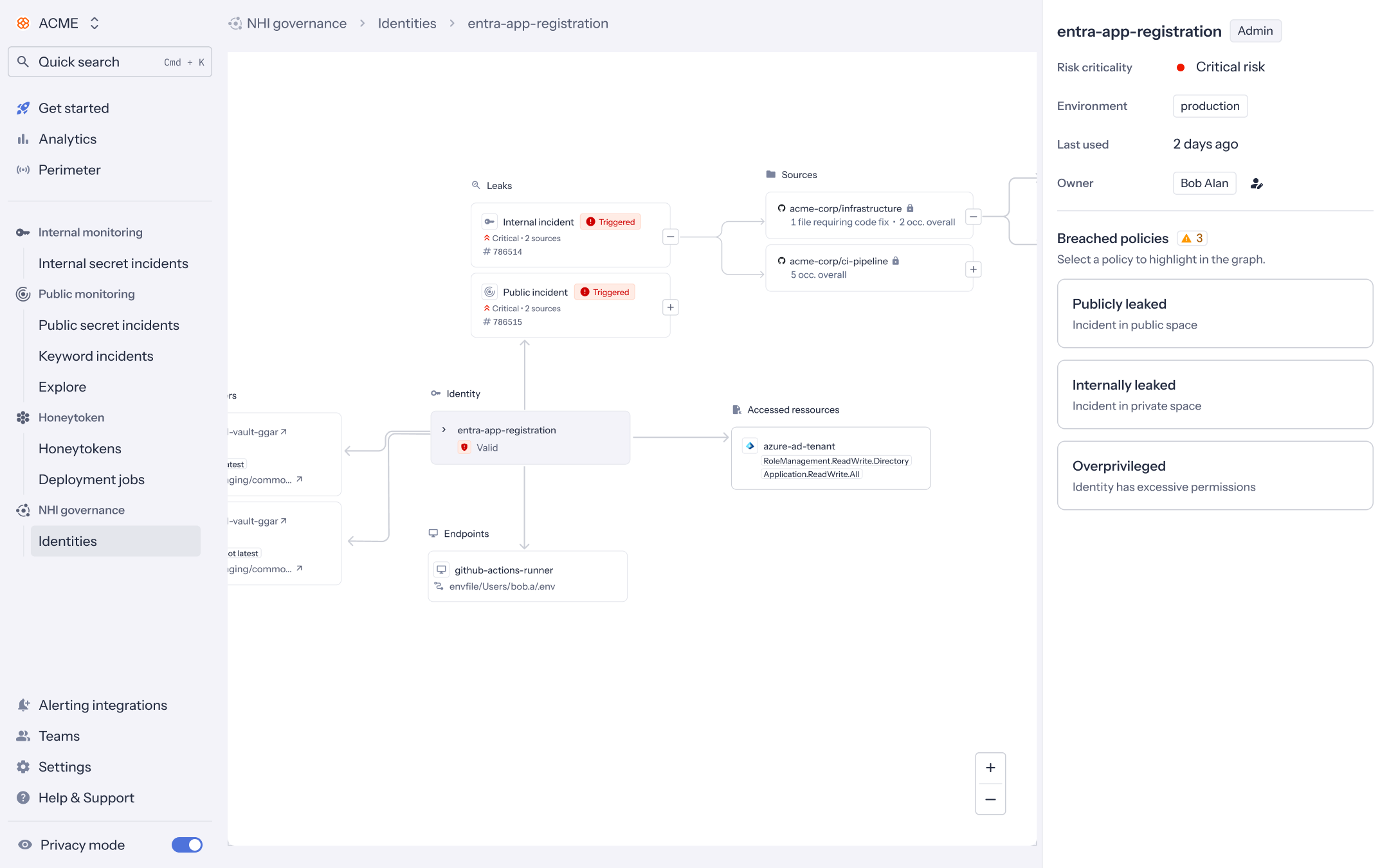
RoleManagement.ReadWrite.Directory carries the Admin badge and inherits Critical risk after the new severity model is applied.With this release, NHI Governance recognizes the application's admin-equivalent rights, tags it with the Admin badge, and bumps the incident to critical. The responder opens the queue, finds the critical at the top, and acts on the priority the new severity reveals: rotate the secret, audit recent role assignments, and check for newly granted application permissions.
Three moves to put this to work this week
Start by sorting your inventory by risk criticality. The identities your program should worry about most now rank at the top of the view, ahead of the long tail of low-impact noise.
Next, filter by Identity level: Admin and run an access review. Every admin NHI deserves a named owner, a documented purpose, and a rotation plan. Identities missing any of those three controls form your immediate remediation list.
Finally, surface Overprivileged Identity breaches and pair the filter with the environmental context. Overprivileged identities in a sandbox slot into the backlog. The same identities in production belong to this sprint.
From privilege context to better prioritization
Privilege has always been a missing axis in NHI risk. Stamping admin status onto an identity does the unglamorous work of separating the five incidents that could compromise an entire cloud account or directory tenant from an inventory of hundreds or thousands of incidents. With this release, NHI Governance moves that distinction from tribal knowledge into the product, across AWS, Entra, and Okta, inside the same workflow security teams already use every day.
Future increments will build on this foundation. Privilege escalation paths and usage-based overprivilege detection will extend the same model with stronger signals and additional API integrations. The most valuable action available today is opening NHI Governance, sorting by risk criticality, and seeing which identities the security team has been quietly under-prioritizing.
Available today to NHI Governance customers. Read the release note or the admin identities documentation for setup details.