Security Zines' Rohit Sehgal is back with an awesome illustration to explain the inner workings of Has My Secret Leaked?, the only free service that helps developers and security people verify if their secrets have been leaked on GitHub.com.
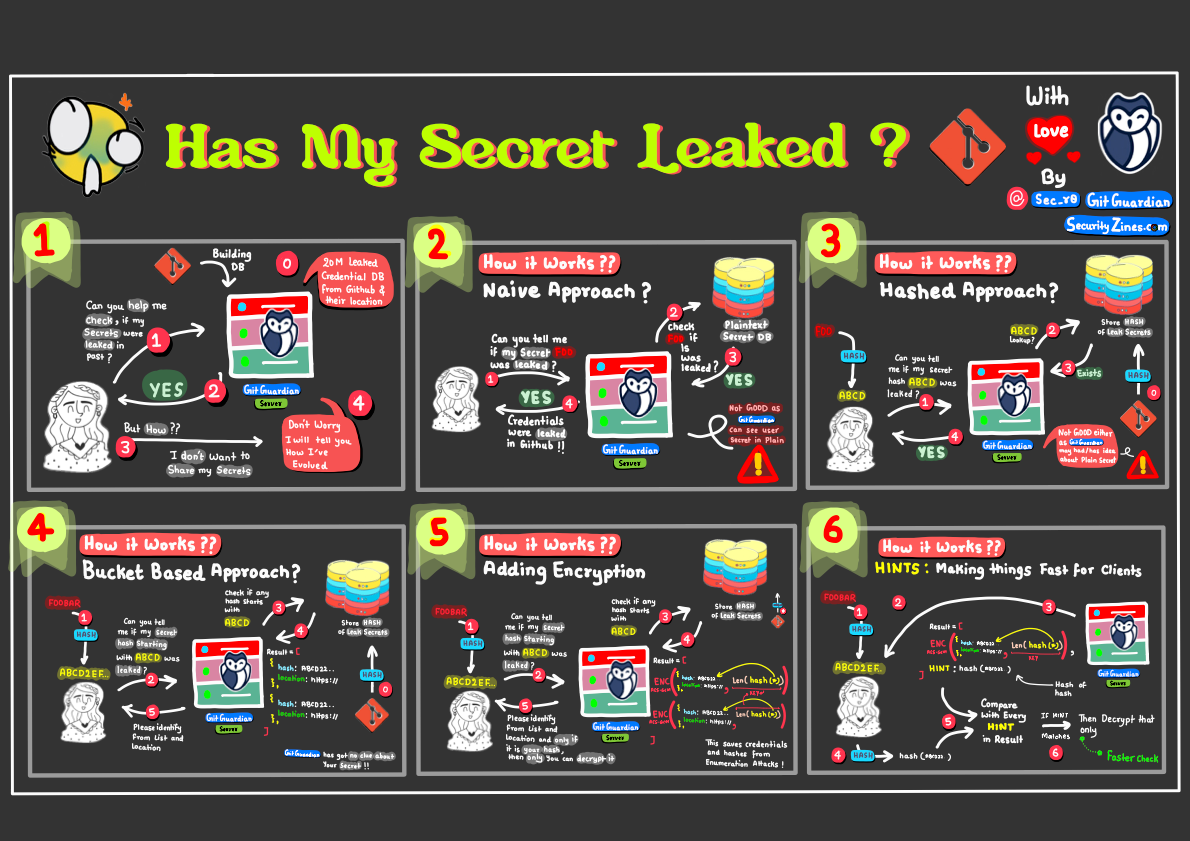
It goes into detail explaining how users can check if their secrets have leaked without revealing the actual secret. The secure protocol ensures GitGuardian does not have access to the users' secrets while helping users check if their secrets have leaked with added security measures.
Zine summary:
-GitGuardian compiled an extensive database of leaks from scanning billions of code files, commits, GitHub gists, and issues since 2017.
- Has My Secret Leaked? involves a hash-based approach where users send a hashed version of their secret.
- To ensure privacy, users only send a fragment of their secret's hash (initial five characters), and the service retrieves matching secrets.
- The service encrypts responses, allowing only the secret's owner to decrypt and retrieve the URL location of the leak.
- Additional security measures include the use of a "pepper" in hashing, restricting queries per day, and disclosing only the first location of a secret.
To check any secret or even a list of secrets directly in your CLI, we recommend using the ggshield hmsl check command. Read the full documentation here.


![Has My Secret Leaked? [Security Zines]](https://storage.ghost.io/c/42/5d/425d266f-cf99-406e-9436-597a19bed011/content/images/size/w2000/2024/01/Security-Z.png)
![Precision & Recall [Security Zines]](https://storage.ghost.io/c/42/5d/425d266f-cf99-406e-9436-597a19bed011/content/images/size/w600/2024/10/Recall-in-Detection.png)
![Honeytokens [Security Zines]](https://storage.ghost.io/c/42/5d/425d266f-cf99-406e-9436-597a19bed011/content/images/size/w600/2024/09/Honeytokens.png)
![Software Composition Analysis [Security Zines]](https://storage.ghost.io/c/42/5d/425d266f-cf99-406e-9436-597a19bed011/content/images/size/w600/2024/05/SOPS-Security-Zine--1-.png)
![SOPS [Security Zines]](https://storage.ghost.io/c/42/5d/425d266f-cf99-406e-9436-597a19bed011/content/images/size/w600/2024/03/SOPS-Security-Zine.png)
