There is a category mistake that happens all the time in the non-human identity (NHI) market. People talk about governance as if it were a box you buy, install, and turn on. It is not.
NHI governance is the outcome of the hard work of understanding what you have and whether each identity is in a desired state. It is the condition you reach when your organization can see non-human identities, understand what access they hold, detect when that access becomes risky, and prove remediation efforts were taken when something went wrong.
That is exactly why GitGuardian’s secrets-first model makes sense for organizations fighting for visibility and control of their sprawling non-human identity inventories.
The GitGuardian platform is built around the pragmatic truth that, if a non-human identity authenticates with an API key, token, service credential, or other secret-backed authentication string, that secret becomes the best artifact for discovering the identity, understanding its reach, and explaining the security state of the access it enables. GitGuardian gives teams true visibility over all NHI secrets across infrastructure, tying that visibility to hygiene improvement and breach reduction.
Let's take a look at the platform, feature by feature, to understand how we deliver on our promise to help you reach your NHI governance goals.
Start With the Secrets You Can Actually See
GitGuardian helps teams get to NHI governance by starting with the thing most organizations can observe right now: the secrets their non-human identities rely on. These access mechanisms provide a pragmatic approach to mapping your identities across your environments.
Most teams do not begin with a complete, clean inventory of every service account, workload identity, automation token, certificate, and API credential in the environment. They begin with fragments. They know some of what lives in cloud IAM. They know some of what lives in their vaults. They know some of what was set up by platform teams, some by developers, and some by vendors. The rest shows up in scattered evidence across the software lifecycle.
GitGuardian gives you visibility into your secrets that should never have been left as plaintext, such as source code and configuration files. But it also extends to the systems surrounding software delivery, where credentials are copied, pasted, cached, logged, and forgotten. This includes messaging systems like Slack, ticketing systems like Jira, container registries like Amazon ECR, among dozens of other places.
That is the first governance outcome GitGuardian supports. Teams get a clearer view of the real identity surface, not the planned one. If a secret exists in a system of record but has also spread into a support ticket or a shared internal workspace, the state of that identity has already changed. That secret is now part of a broader exposure story, and GitGuardian gives teams a way to see it.
Extend the View Into the Vaults
Secrets visibility only goes so far if the picture ends at plaintext exposure. GitGuardian extends the model by indexing secrets from the places teams intentionally store them. Enterprise secrets managers, such as Hashicorp Vault and CyberArk's Conjur, or cloud providers such as AWS Secrets or Azure Key Vault
GitGuardian collects secret metadata to enrich the inventory without sending secret values in the clear. GitGuardian is no longer only telling you what leaked. It is also helping you understand the managed layer where those secrets are supposed to live.
That creates a much more useful inventory across infrastructure. Teams can see the secrets created within approved systems and compare that state with the same credentials discovered elsewhere in the organization. The same secret in a vault, a private repository, and a team chat means something has gone wrong with your governance plan. GitGuardian provides a single view that is much closer to the truth of how access actually works inside modern systems.
Confronting Vault Sprawl In NHI Governance
Vault visibility also surfaces a problem that deserves more attention than it usually gets: vault sprawl.
Many organizations have done the right thing in spirit and still carry unnecessary complexity in practice. They have multiple secret managers, overlapping teams, inherited platforms, duplicated values, and different operational habits across cloud, product, and security groups.
GitGuardian helps expose that overhead by showing where the same secret is duplicated, reused, or spread across environments. The product’s posture policies explicitly include duplicated secrets, reused secrets, and cross-environment secrets.
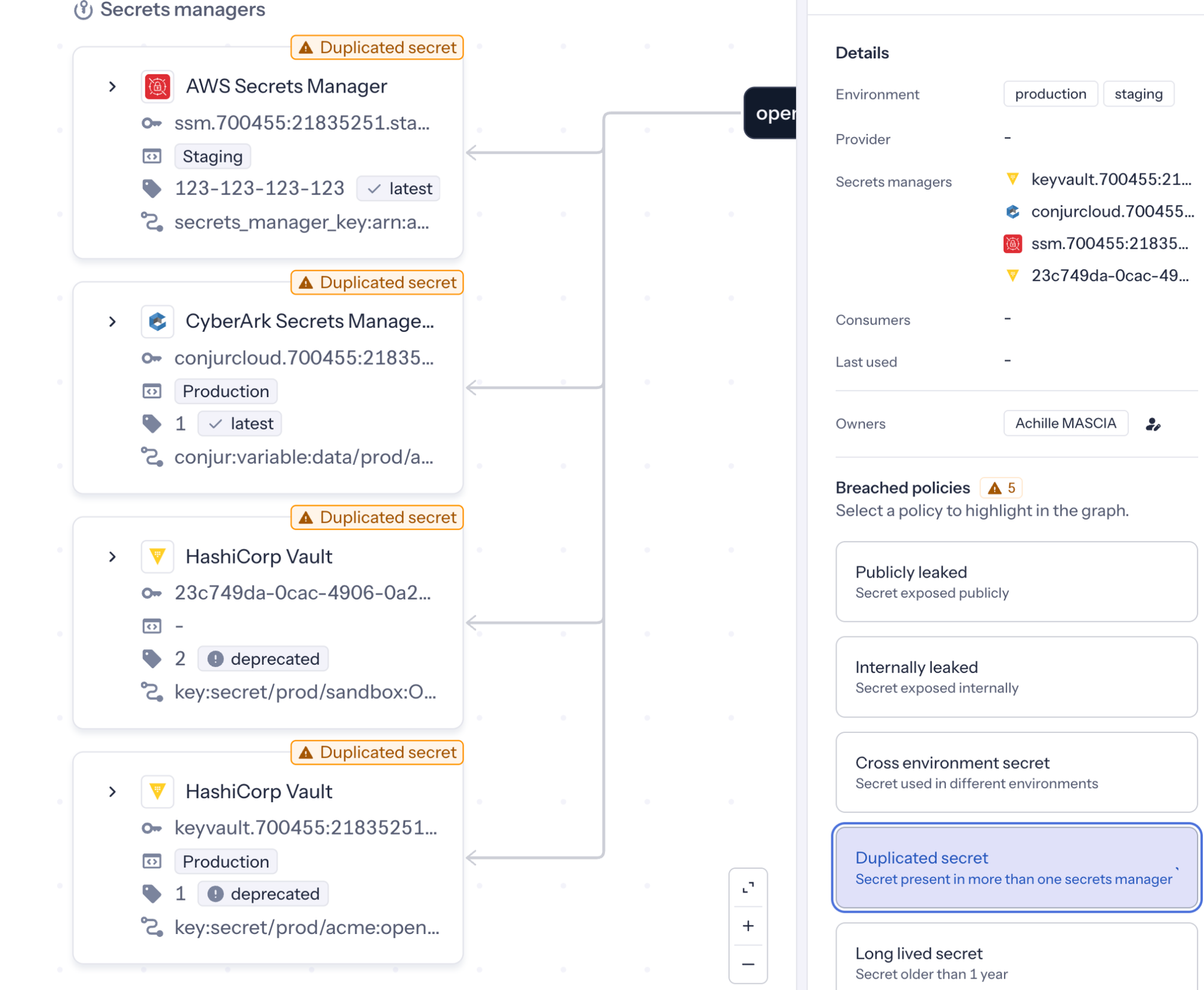
The GitGuardian platform does not just tell you that a vault exists. It helps you see whether the state of your vault-backed secrets is clean, duplicated, sprawling, or risky.
Turn Secret Discovery Into a Live Inventory
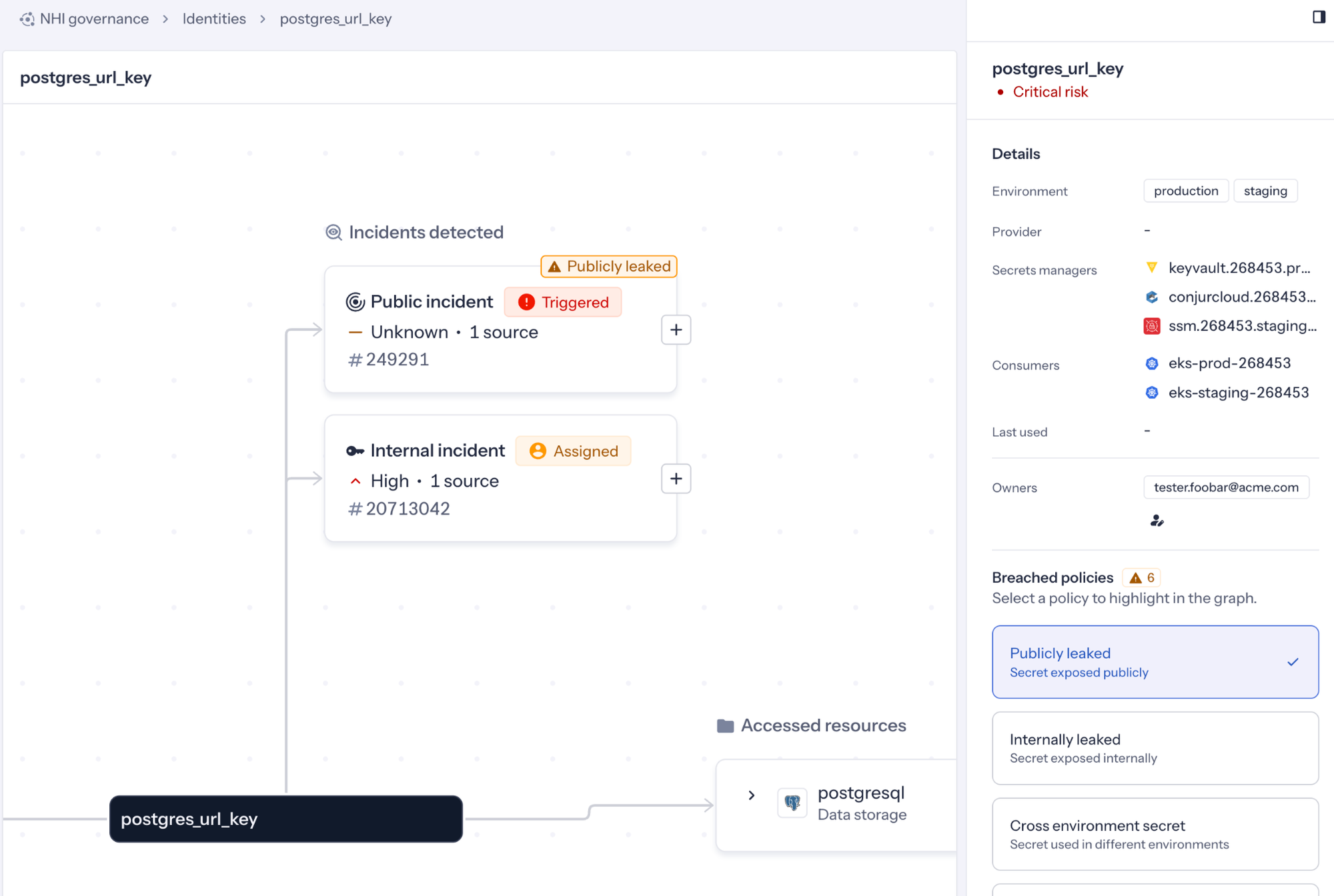
Turning your detection findings into a living inventory is where the larger governance story starts to come together. GitGuardian’s platform provides a centralized NHI inventory connecting discovered identities, secrets, and related context. This makes it easy for teams to search, review, and prioritize what they have across the whole of their enterprise environment. The goal is a unified visibility into the cloud identity footprint, with graph-based relationships across identities, policies, and secrets.
That inventory matters most when it reflects state instead of aspiration. A spreadsheet of service accounts does not tell you where credentials have spread. A static export from one platform does not tell you whether the same secret is reused somewhere else, duplicated in another system, or exposed outside the boundary where it was meant to live. GitGuardian brings those questions together because its model starts with the secret itself and then layers in identity, source, ownership, and policy context around it.
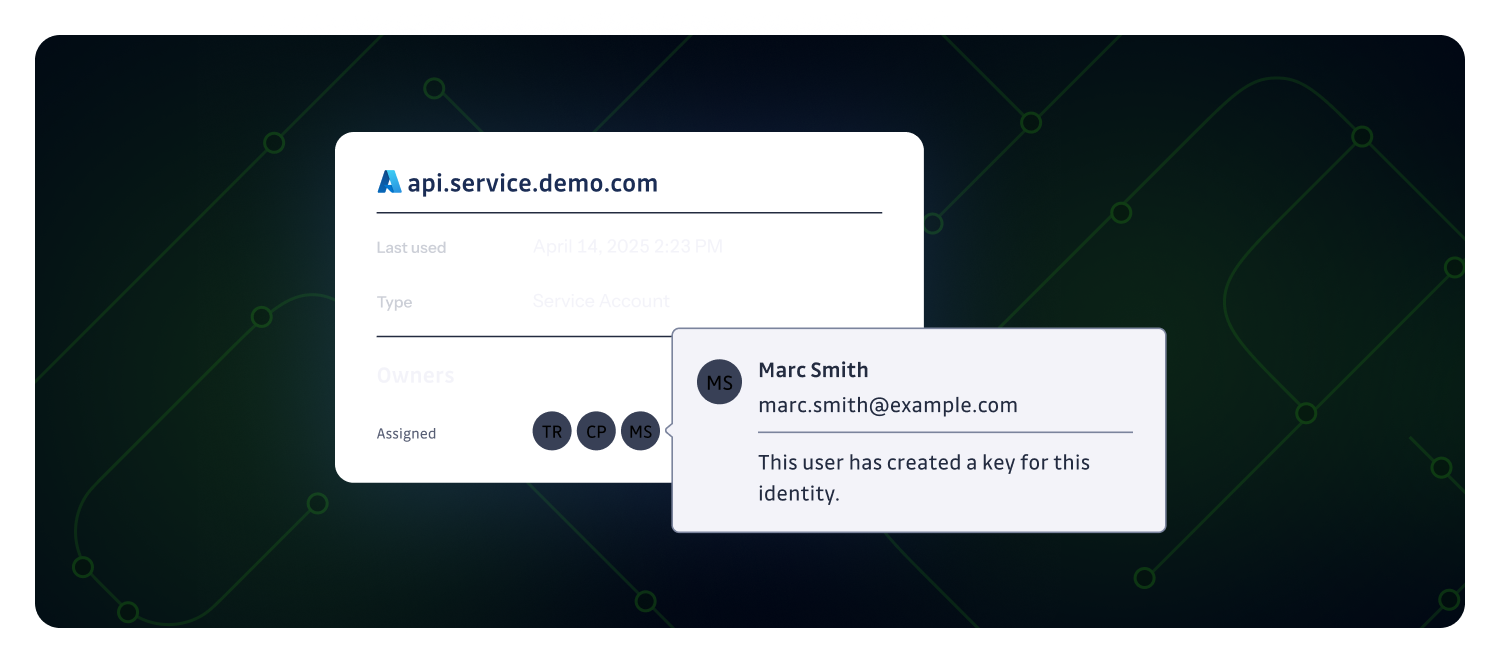
Each non-human identity has a visual knowledge graph on GitGuardian that maps the systems where they are created, stored, and used, and layers metadata from each source into a unified model. The platform, using ggscout, collects the fingerprint of secrets and related metadata from supported secrets managers, while CI and infrastructure sources, such as GitLab, add the "where" NHIs are used and consumed. Cloud IAM systems, including Microsoft Entra and AWS IAM, add permissions and policy context, other identity providers extend identity coverage, and SaaS providers add visibility into usage and potential exposure.
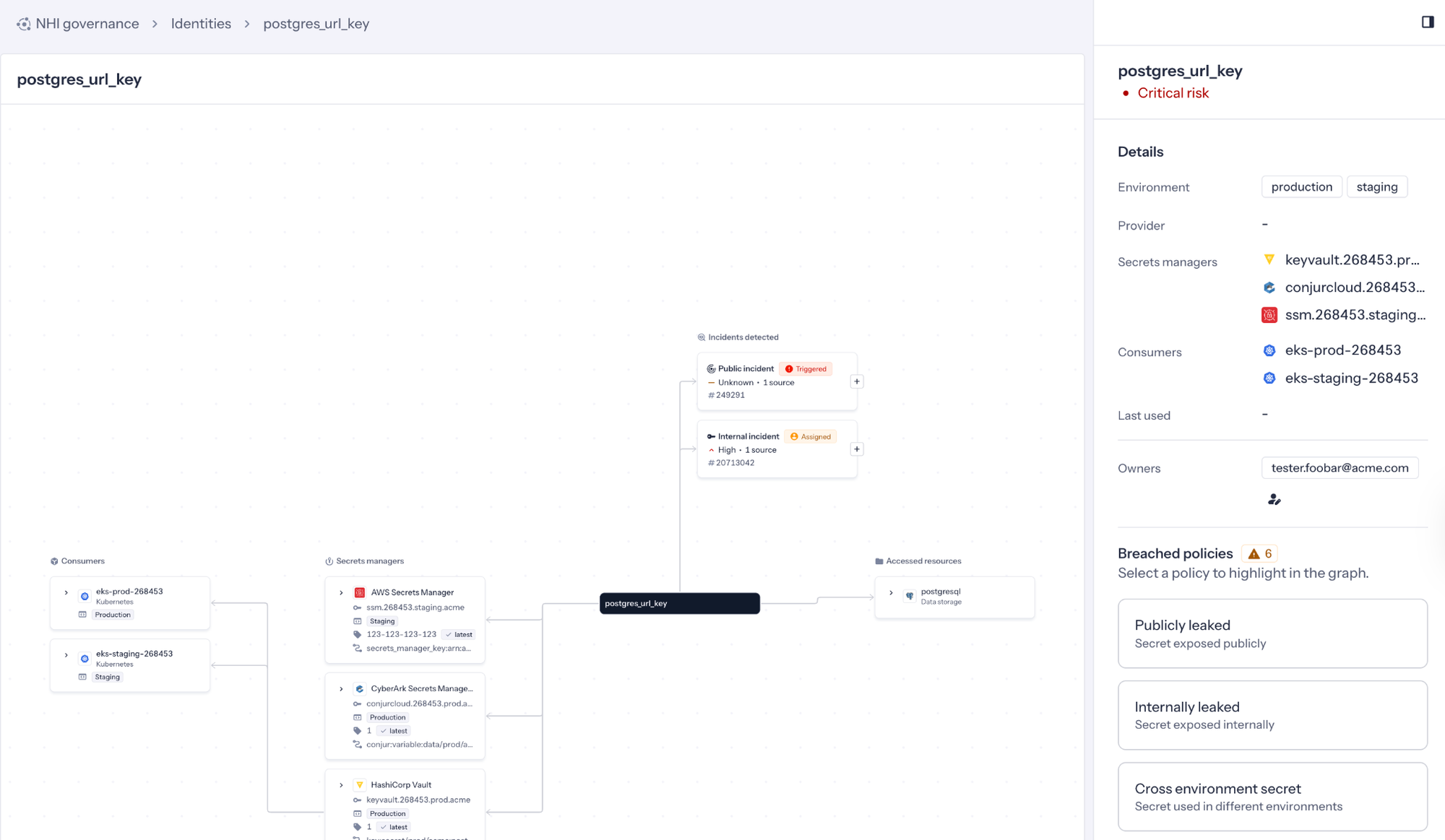
GitGuardian gives you one contextual view of NHI posture. That makes the inventory operational. Which credentials are active? Which ones are leaking across trust boundaries? Which ones are tied to sensitive roles or broad permissions? Which ones are duplicated across storage locations? Governance gets more concrete once the inventory reflects those conditions.
Add Ownership to the Inventory
Inventory alone does not move risk. Someone has to own the identities, the credentials, and the cleanup. GitGuardian lets teams assign responsibility to non-human identities directly in the inventory. This helps close the accountability gap for machine identities, speed remediation, and support compliance expectations.
Most teams already know the mechanical work of secret rotation, credential cleanup, and policy review. The real slowdown usually comes from ambiguity. Who owns this service principal? Who is responsible for the token tied to this automation? Who decides whether a duplicated credential can be removed? Who gets paged when a leaked secret is tied to a business-critical workflow? GitGuardian makes that ambiguity visible and more manageable by placing ownership alongside the identity record itself.
Ownership also changes how teams can talk about governance internally. The conversation stops being “we found another secret” and becomes “this identity is out of policy, here is the owner, and here is the condition that needs to be resolved.” That is a much healthier operational model. It turns secret incidents into identity decisions, and it gives engineering, platform, and security teams a common object to work on together.
Use Policy to Define Acceptable State
Governance needs a line between acceptable and unacceptable states. GitGuardian’s NHI Governance posture policies provide that line in a way that stays close to observable conditions. The documentation says these policies are informed by the OWASP Top 10 for NHIs, and the currently documented set includes publicly leaked secrets, internally leaked secrets, cross-environment secrets, reused secrets, and duplicated secrets.
These policies work because they are concrete. They describe conditions a team can verify. A secret is either publicly exposed or not. A credential is reused across identities, or it is not. A secret crosses environment boundaries or it does not. A value is duplicated across storage locations, or it is not. That makes policy useful as an operational tool instead of a vague aspiration.
It also helps teams mature without pretending they need to solve every machine identity problem in one move. A team can start by reducing public exposure. Then it can work on internal sprawl, duplication, and environment separation. From there, it can move toward cleaner ownership, stronger storage patterns, and narrower permissions. GitGuardian supports that progression because the product is built to show the current state, not just the ideal future state.
GitGuardian Helps Teams Earn the Outcome
NHI governance is the result of understanding what exists, its current state, who owns it, and whether that condition is acceptable. What is acceptable to your team can only be determined by your circumstances and risk tolerances.
GitGuardian helps teams achieve their desired outcomes by prioritizing secrets visibility first. It finds credentials where they were exposed across the software lifecycle. It extends that picture into the vaults and managed stores where those credentials are supposed to live. It turns those fragments into an identity inventory that can be searched, reviewed, and prioritized. It adds ownership so someone is accountable for cleanup and decision-making. It enriches the picture with identity and permission context so teams can understand the impact. It applies posture policies so governance has a measurable definition.
GitGuardian gives teams a better view into the state of their non-human identities by following the secrets those identities depend on. For a problem as messy and distributed as machine identity governance, that is exactly where organizations should start.