Leaked Kubernetes Secrets: Impact Assessment and Mitigation Strategies
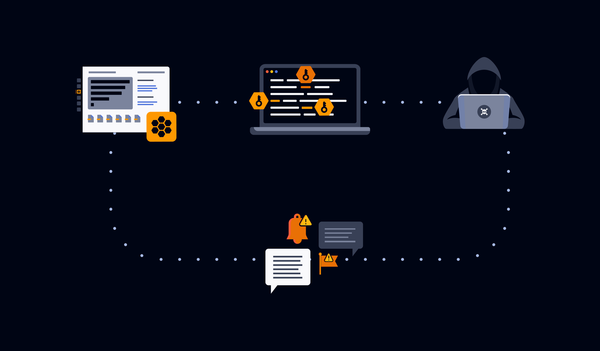
A single leaked Kubernetes credential rarely stays in the cluster. It opens the registry credentials, private Docker images, and private GitHub repositories behind it. In Q1 2026 alone, our detectors caught close to 2,000 new such leaks on GitHub, 28% valid at leak time.