Automating and integrating secrets detection into version control systems (VCS) like GitHub, GitLab, and BitBucket, as well as continuous integration (CI) tools, is a crucial component of DevSecOps. We are eager to introduce the following significant advancement in our effort to maintain code security across your SDLC. GitGuardian Internal Monitoring now has native integration with the Azure DevOps Platform.
Let's look more closely.
Integrate Azure DevOps repos into GitGuardian
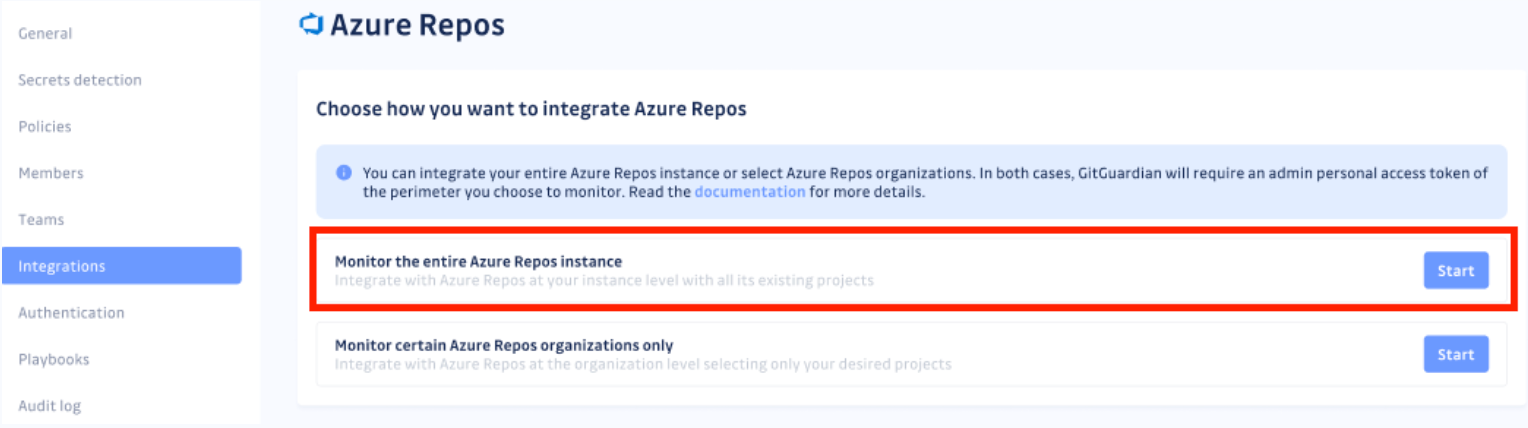
There are two ways that GitGuardian can integrate with Azure Repos: at the instance level or the organization/collection level.
The first step in configuring both integrations is to get an access token from Azure. Using your Azure DevOps permissions and this personal token, GitGuardian can access your repositories. We strongly advise using a bot user to generate personal access tokens.
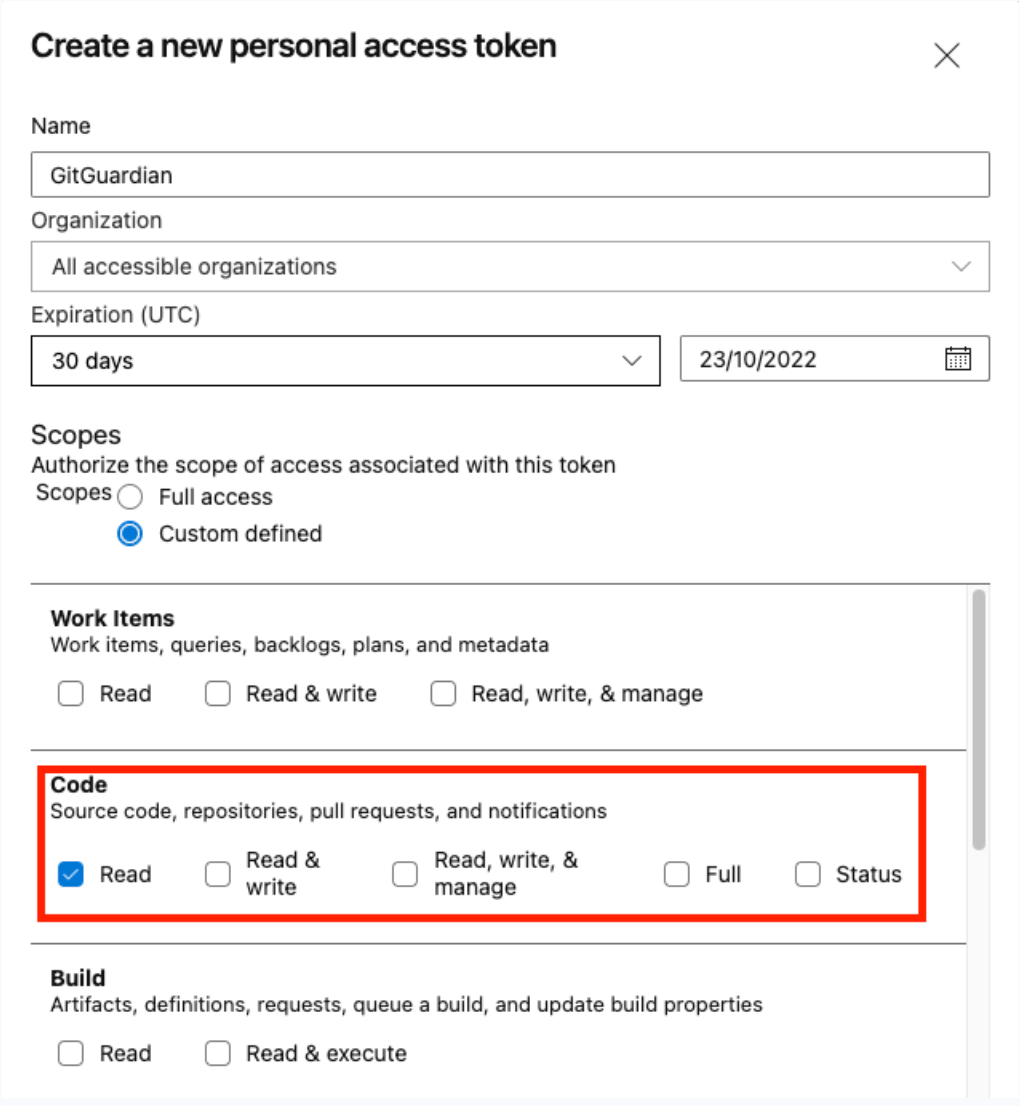
- Go to the "User setting" area of Azure DevOps.
- Create a new token for the Azure Repos Service by going to the "Personal access tokens" section. You must first enter "Security" for Azure Repos Server, then choose the Personal access tokens page from the left sidebar.
- Set a name, such as "gitguardian."
- You can grant access to the entire instance or the current organization.
- Important: Under Scope>Code, you must choose "Custom defined" and check the "Read" scope.
- The maximum allowed expiration date is one year, so we advise setting it to that.
You must remember that the maximum validity period for a token in Azure DevOps is one year when you create your GitGuardian access token. It implies that if you want to keep the integration active, you'll need to renew the token.
With that information in mind, head to GitGuardian's Integrations page and choose how you want to integrate Azure Repos. Here, we click on Start for the instance-level option. For project-level integration, please visit the Azure DevOps Repos section of our documentation.
You now must submit your Azure Repos Instance URL and the token you created above.
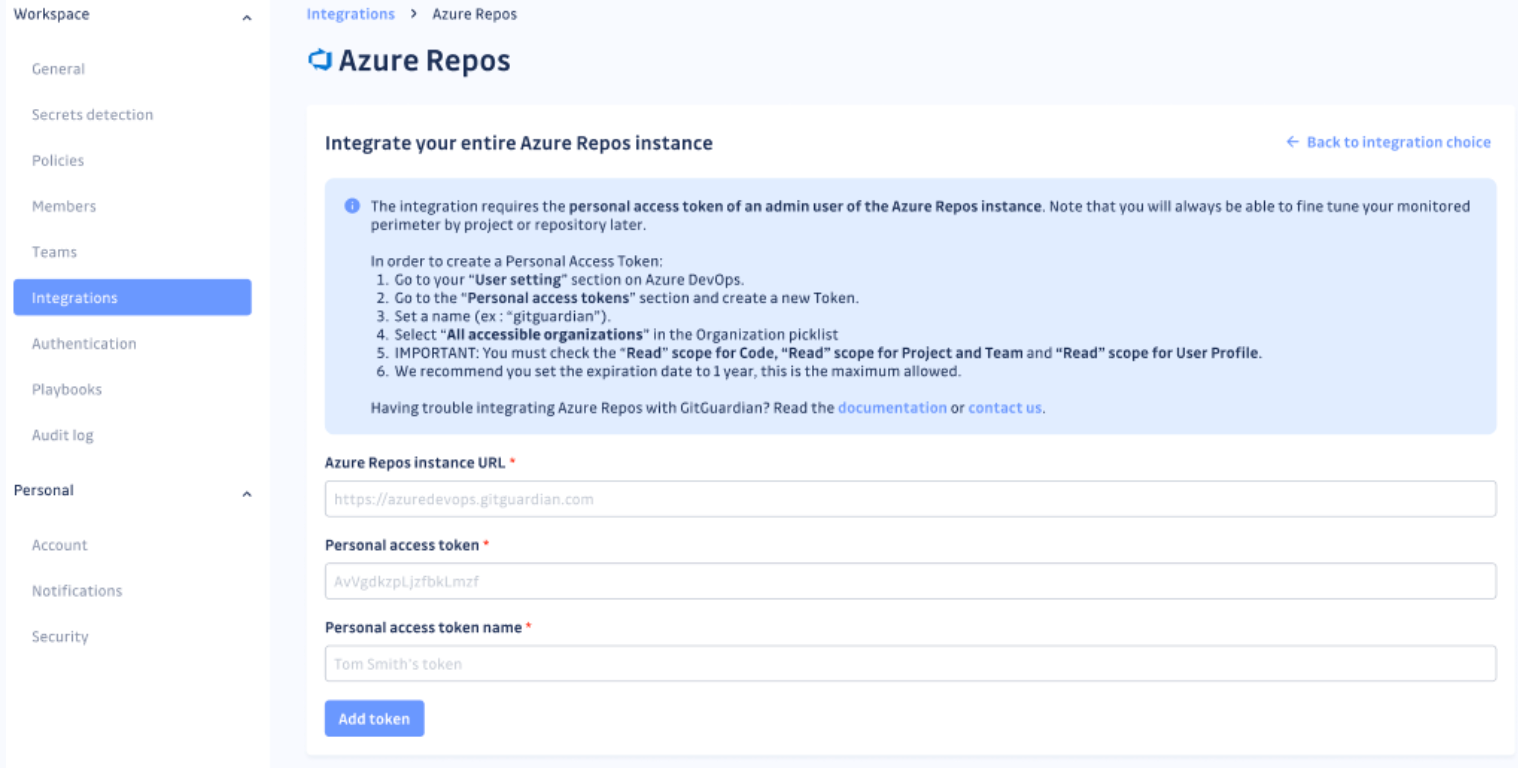
After hitting the Add token button, GitGuardian will scan your Azure Repos instance.
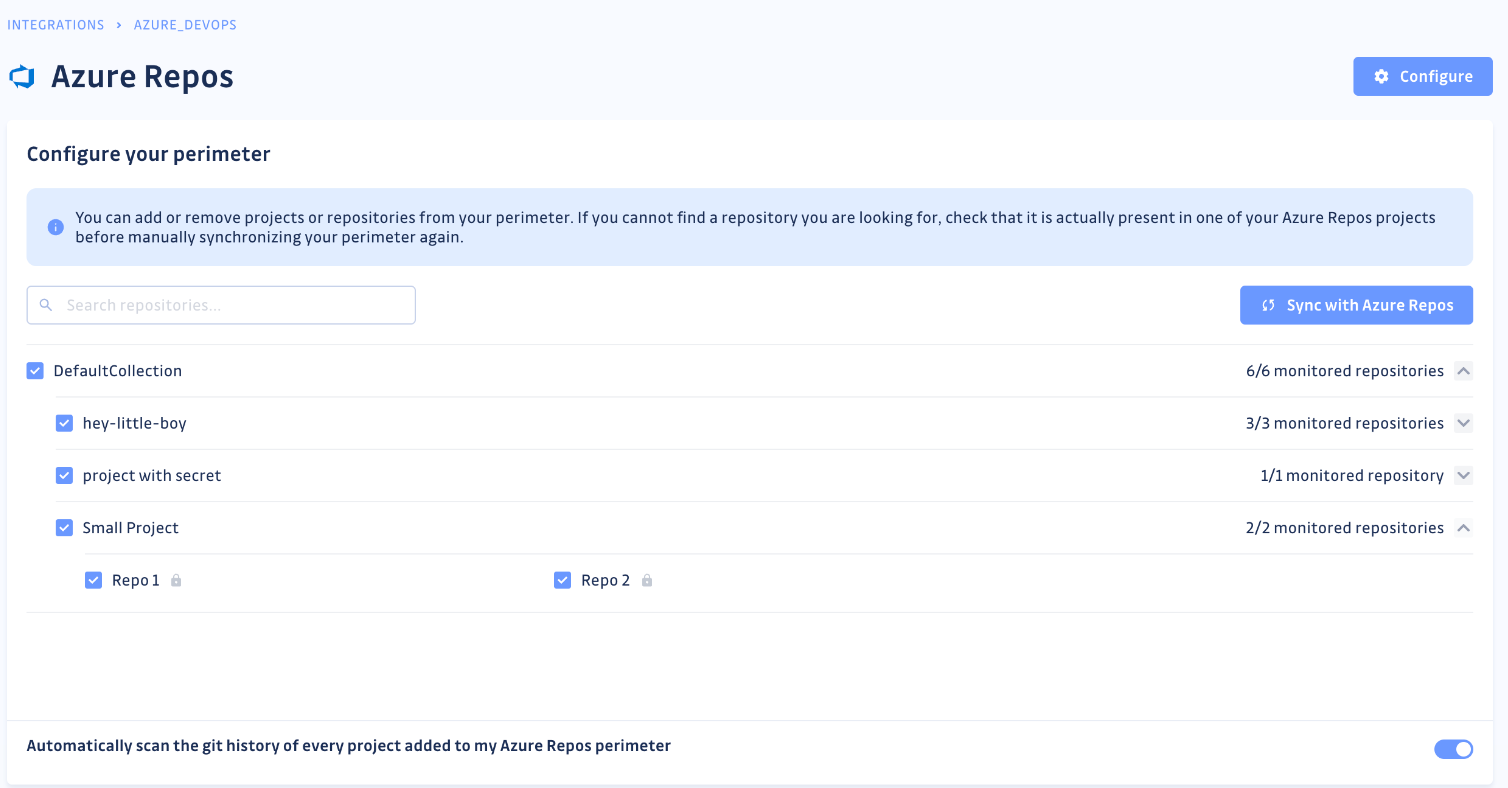
You can view the projects and repositories monitored in your Azure Repos settings page by clicking on See my Azure Repos perimeter.
For each new repository added to your perimeter, GitGuardian, by default, runs a historical scan. Your old commits can contain valid secrets! And remediating years of historical hardcoded secrets incidents can be a complex job. But together, we can pull it off. See this guide.
Once you have set up your Azure Repos integration, you can customize your monitored perimeter and configure which projects and repositories you want to monitor in the Azure Repos settings section of your workspace.
After setting up the integration, it is time for incremental scanning of new commits. It is important to resolve past incidents and handle new ones too. Make the most of our secret detection algorithms that have been battle-tested at scale across the entire public GitHub for over five years!
You can also encourage fellow developers to use our CLI tool, ggshield's pre-commit hooks, to prevent secrets from reaching your codebase altogether.
Implement automated secrets detection across the Azure DevOps suite
For a secure and reliable supply chain, it's essential to secure your code at the source, right where it is managed. After all, VCSs are not suitable places to store secrets. The secrets it holds would be open to everyone with access to the source code. GitGuardian offers its users several native VCS integrations, the most recent of which is the one with Azure DevOps. These native integrations assist developers in securing their applications at every stage of the SDLC, from source control to CI/CD pipelines.
Visit the Integrations page in GitGuardian or our documentation for more information on getting started with any integrations.
Please be aware that this integration supports Azure repos for any version of Azure DevOps with the Rest API ≥ 4.1. Azure DevOps Services and Azure DevOps Server 2019 and 2020 are included. All users of our Business plan are eligible for the integration.
Try your first Azure DevOps integration!
We have another exciting new integration coming soon, so stay tuned!