Last time we briefly touched on the concept of a fortress in cybersecurity. In this Episode, Philippe will do a more thorough analysis on this topic.
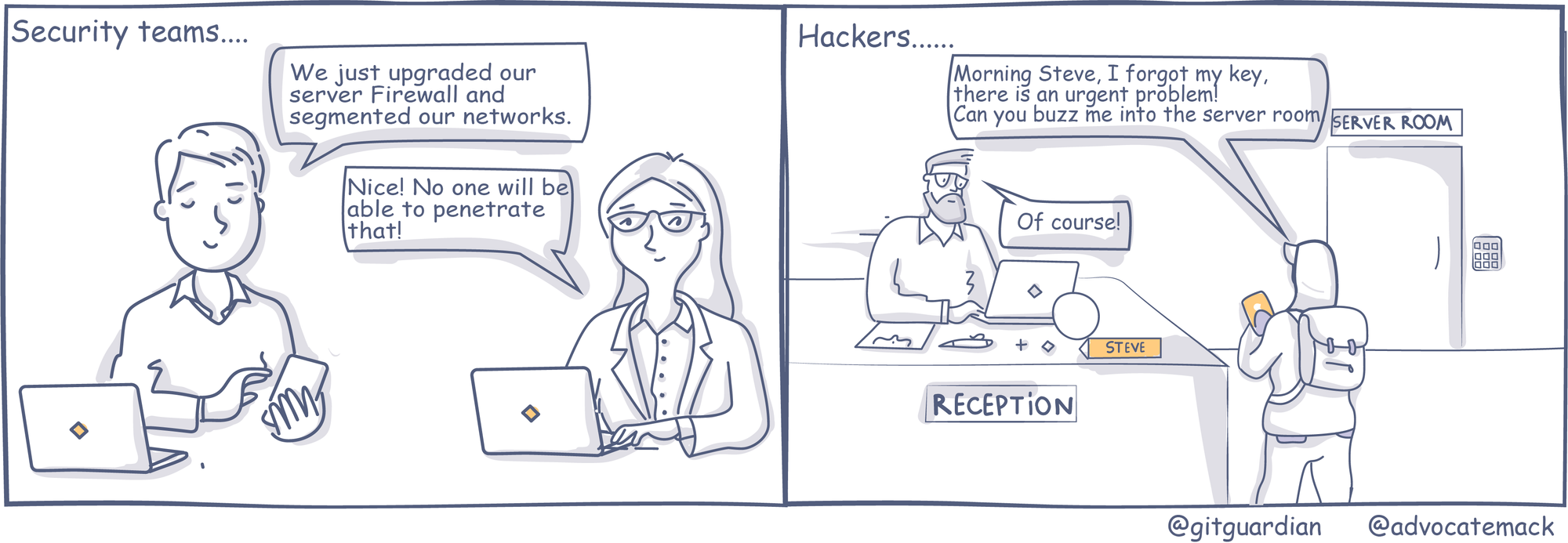
Building a fortress is a strategy from the past. Mobility, remote working, cloud and SaaS have made the delineation between internal and external networks almost impossible. And even beyond these concepts, physical security should be part of your cybersecurity strategy… An attacker does not need to bypass your firewall if he/she can bypass your receptionist and physically connect a device on your internal network.
While some of these scenarios may seem out of James Bond movies, the reality is that there are plenty of tools readily available to facilitate some of these attacks. From RFID attacking tools that can copy employees’ access cards from a distance to RFID implants that can be installed on the card readers themselves in under a minute, these types of attacks no longer require really advanced skills.
RFID access cards usually contain two values: Facility Code and Card ID. The facility code is usually the equivalent of the code of a building and is generally the same for all employees. On the other hand, we have observed that the Card ID is often incremental, which means that if an attacker can copy the card of one employee, it is then possible to perform other types of attacks (e.g. brute force) to then gain access to more sensitive areas such as computer/ network rooms.
Here is a picture of a custom tool that can perform this type of physical brute force attack against card readers.
Sometimes we do not even need to copy access cards, gaining access to office buildings is as easy as following the crowd in the morning and block a meeting room for the day.
In large organizations, we often see screens that tell you which rooms are reserved or available
Our favorites are the ones that even let you reserve a room for several hours directly from a touch screen.
Meetings rooms often offer network and telephony access, so once an attacker has physical access to it, the opportunities are endless.
Moving away from physical access, let’s look at the targets.
Generally, Attackers do not prioritize their initial targets based on their level of access. The first goal is to obtain initial access and then move laterally to other systems or vertically to escalate privileges.
We see a lot of efforts and solutions implemented to secure the final targets but the initial targets are usually left out with little to no protections.
When attackers acquire users’ authentication elements, they don’t need to further exploit any vulnerabilities, they are already in the system as a valid user.
Keep in mind that the initial target is not always a person, it can also be a machine connected to the network. Multi-Function printers are a good example. These devices often have default passwords and in order to send scanned documents by email or on a network share, credentials are often stored on it. These are perfect entry points for attackers.
To add to this, if your SSO is not well configured (e.g. auto enrollment), then it means the technical user account configured on the printer can also access systems like Jira or Slack which very often host a good number of secrets.
And what about two-factor authentication (MFA)?
It is a good thing and we recommend to our customers to use it because makes life more difficult for attackers. BUT deploying MFA does not make you immune against all attacks.
We recently worked on a security incident for one of our customers, where the attackers were able to exploit a vulnerability in their VPN appliance in order to retrieve the cookies/sessionID of authenticated users in order to gain unauthorized access to the VPN and move laterally to the internal network.
As you can see, Philippe has some interesting stories to share as well as some useful recommendations to make. If you are interested, keep following the Red Team Chronicle by subscribing to our newsletter or following us on twitter or LinkedIn.