Identity orchestration unifies fragmented IAM environments by connecting identity providers, directories, access policies, and governance workflows into a single, automated control plane.
As multi-cloud, hybrid, and SaaS-heavy architectures expand, managing identities across siloed systems has become a major operational and security challenge for enterprises.
The top identity orchestration tools in 2026 fall into several categories:
- Identity orchestration engines
- IAM platforms with orchestration capabilities
- Identity governance and lifecycle platforms
- Secrets security and NHI exposure prevention
Most enterprises need an orchestration layer to unify identity flows and a secrets security layer to ensure credentials and non-human identities (NHIs) aren't compromised.
Why Identity Orchestration Is a Top Priority in 2026
For context, the average enterprise manages identities across 5 to 10+ identity providers, directories, and access management systems.
The result? Fragmented access policies, inconsistent lifecycle management, identity blind spots, and a sprawling attack surface. This is especially true for non-human identities (NHIs) that slip through the cracks of traditional identity access management (IAM).
This is why identity orchestration, which is the practice of connecting, coordinating, and automating identity management across multiple systems through a unified control plane, is so important.
Rather than ripping and replacing your existing identity stack, identity orchestration software sits above it, enforcing consistent policies, automating lifecycle workflows, and centralizing visibility across all connected systems.
The Need for Identity Orchestration Software
In 2026, identity orchestration solutions are a top priority for most CISOs. It's not surprising—the current environment makes these tools "must-have" apps.
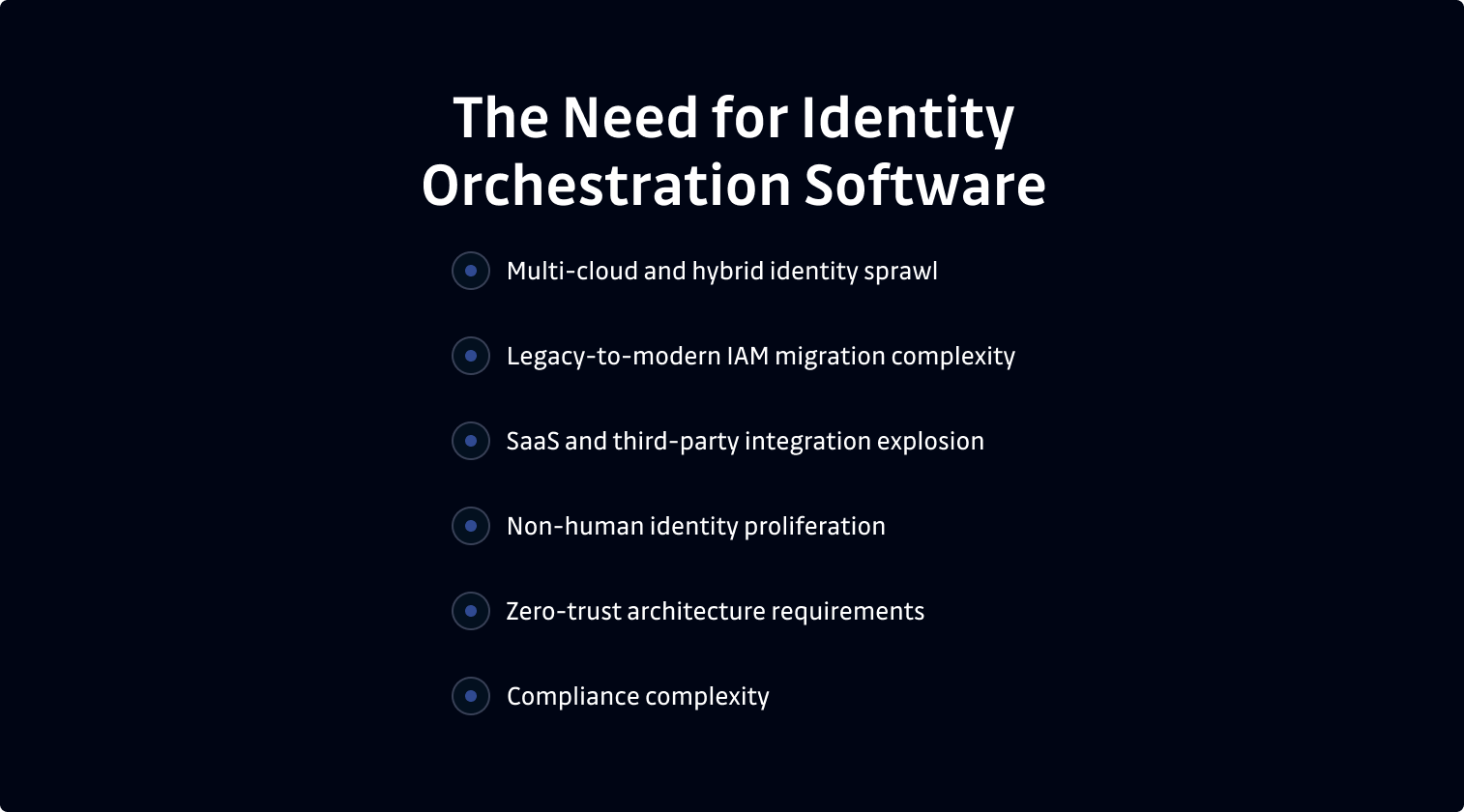
- Multi-cloud and hybrid identity sprawl. Organizations that run workloads across AWS, Azure, GCP, and on-premises environments end up with disconnected identity silos, each with its own policies, directories, and governance processes.
- Legacy-to-modern IAM migration complexity. Many companies run critical applications on legacy systems that depend on LDAP or on-premises Active Directory. Updating those systems to modern identity standards, without rewriting every app, requires an orchestration layer.
- SaaS and third-party integration explosion. Every SaaS tool comes with its own identity requirements. Without orchestration, IT teams must manually manage provisioning across dozens of disconnected platforms.
- Non-human identity proliferation. API keys, service accounts, OAuth tokens, and certificates now outnumber human identities in most enterprise environments. These machine identities are frequently ungoverned, long-lived, and dangerously over-permissioned.
- Zero-trust architecture requirements. Zero trust demands continuous verification and centralized policy enforcement across every identity interaction. Identity orchestration provides the control plane that makes this possible at scale.
- Compliance complexity. Meeting SOC 2, ISO 27001, and PCI DSS requirements across a multi-vendor IAM stack creates significant audit and reporting overhead without a centralized governance layer.
The NHI Blind Spot in Identity Orchestration
Identity orchestration platforms manage identity flows and access policies. But these tools can't detect if the credentials moving through said flows are compromised.
If an API key tied to a service account was hardcoded in a repository two years ago, and has been sitting exposed in git history ever since, rotating it through an orchestration workflow would only partially help until someone finds and remediates the original leak.
Orchestration expands the blast radius of a compromised credential by connecting it to more systems. Doing so makes eliminating credential exposure during orchestration deployment a standard security protocol, not an optional add-on.
This is why it's important to integrate a dedicated secrets security platform like GitGuardian with the specific identity orchestration solution you choose for your company.
Key Capabilities of Modern Identity Orchestration Platforms
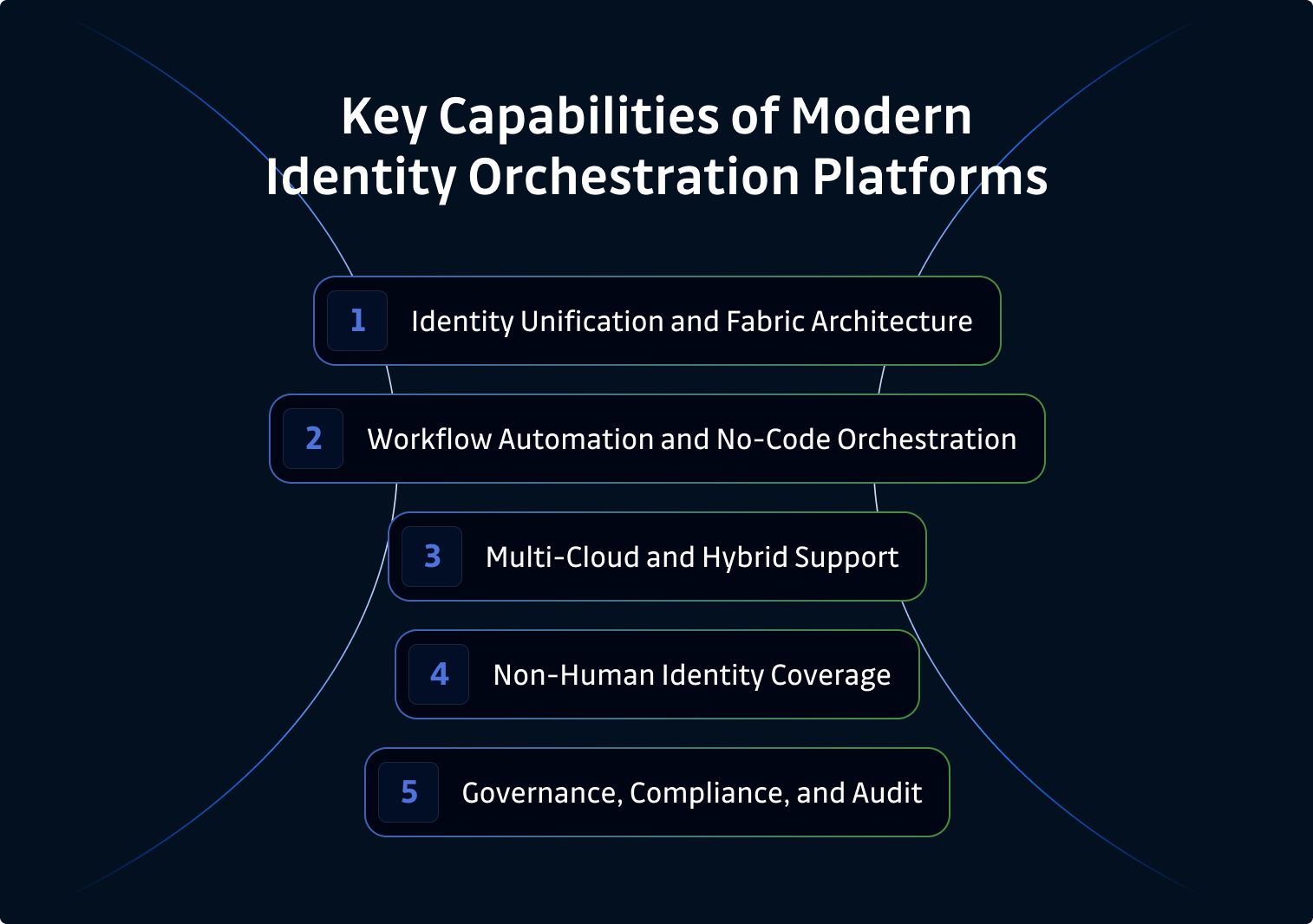
Before comparing vendors, it helps to align on what modern identity orchestration software actually needs to deliver. Here is what enterprises should evaluate:
1. Identity Unification and Fabric Architecture
The platform should connect multiple identity providers, directories, and cloud IAM systems through a single control plane. Also, look for protocol translation and normalization across SAML, OIDC, OAuth, SCIM, and LDAP, as well as centralized policy enforcement across heterogeneous environments.
2. Workflow Automation and No-Code Orchestration
The best solutions offer visual workflow builders to design identity journeys and automate provisioning, deprovisioning, and lifecycle events. Additionally, no-code orchestration lowers the barrier for IAM teams because they don't have to write custom code for every integration.
3. Multi-Cloud and Hybrid Support
Top tools also include cross-cloud identity federation, on-premises app bridging for legacy modernization, and support for Kubernetes and containerized workloads. These features are table stakes for enterprise deployments that operate across hybrid cloud environments.
4. Non-Human Identity Coverage
Now that NHI populations grow faster than any other identity category, service account discovery and governance, API key and token lifecycle orchestration, and machine identity visibility within orchestration workflows are critical capabilities.
5. Governance, Compliance, and Audit
Finally, the best identity orchestration solutions have centralized audit trails across identity systems and compliance reporting for SOC 2, ISO 27001, and PCI DSS. They also offer risk scoring and access reviews, which are required by enterprises that operate in regulated industries or manage complex multi-vendor IAM stacks.
The Missing Layer: Secrets Exposure Detection
While secret exposure capabilities fall outside the scope of most orchestration platforms, every CISO who evaluates orchestration tools should plan for it. Why? Because the secrets that flow through orchestration layers are only as secure as their exposure posture.
Dedicated secrets security platforms fill the gap with git history scanning, CI/CD pipeline monitoring, public exposure detection, and collaboration tool scanning across Slack, Jira, Confluence, and Teams. This leads to fewer data breaches within existing systems.
Top Identity Orchestration Tools and Platforms for 2026
1. Strata Identity
Category: Identity orchestration and identity fabric platform
Strata Identity pioneered the "identity fabric" approach to identity orchestration. The platform abstracts identity infrastructure into a unified orchestration layer, helping companies modernize legacy apps, consolidate multi-cloud identities, and enforce consistent policies without rip-and-replace migrations.
Core Features:
- Identity Fabric Architecture: Abstracts and unifies identity across multiple IdPs and directories
- Legacy App Modernization: Bridges legacy identity protocols (LDAP, on-prem AD) to modern standards (OIDC, SAML) without rewriting applications
- Multi-Cloud Policy Orchestration: Centralized policy enforcement across AWS, Azure, GCP, and hybrid environments
- No-Code Workflow Design: Visual tools for building identity journeys and access flows
- Identity Routing: Intelligent routing of authentication requests across providers
Pros:
- True identity fabric approach with strong multi-IdP unification
- Excellent for legacy-to-modern migration without app rewrites
- Strong multi-cloud and hybrid environment support
Cons:
- Strata Identity is not focused on secrets exposure detection and NHI-specific security. Because of this, organizations should layer secrets security tooling to cover leaked credentials that pass through their orchestration workflows.
Pricing: Enterprise commercial pricing; contact for quotes.
Enterprise Fit: Strata Identity is ideal for large enterprises with complex, multi-IdP environments that need a unified orchestration fabric—especially if said enterprise is undergoing legacy IAM modernization.
Website: strata.io
2. Ping Identity (PingOne DaVinci)
Category: No-code identity orchestration engine
PingOne DaVinci is Ping Identity's no-code orchestration engine, which lets identity teams build adaptive authentication flows and visual identity journeys without custom development. It integrates natively with the Ping ecosystem and supports third-party connectors.
Core Features:
- No-Code Flow Builder: Drag-and-drop interface to create identity journeys
- Adaptive Access: Conditional logic with risk signals for step-up authentication
- Pre-Built Connectors: Library of integrations with IdPs, MFA providers, fraud detection tools, and directories
- Centralized Orchestration: Unifies Ping products and third-party services into a single flow engine
- API-Driven Extensibility: Custom connectors and API hooks for specialized workflows
Pros:
- Powerful no-code orchestration with a mature connector ecosystem
- Adaptive access and risk-based authentication capabilities
- Well-integrated with the broader Ping Identity platform
Cons:
- PingOne DaVinci is best when used within the Ping ecosystem. Also, it doesn't provide secrets exposure detection or NHI-specific credential security.
Pricing: Commercial SaaS pricing; tiered enterprise plans.
Enterprise Fit: PingOne DaVinci is a strong option for enterprises already in the Ping ecosystem, or those that need flexible, no-code identity flow orchestration.
Website: pingidentity.com
3. Simeio

Category: Managed identity orchestration services
Simeio combines an identity orchestrator platform with managed identity services. As such, it unifies siloed IAM environments, which allows enterprises to manage multiple identity tools through a single interface with managed-service support.
Core Features:
- Identity Orchestrator: Unified interface for managing multiple IAM tools and workflows
- Managed Identity Services: Expert-managed identity operations and administration
- Multi-Tool Unification: Connects disparate IAM platforms, like Okta, Azure AD, and SailPoint
- Lifecycle Orchestration: Automated provisioning, deprovisioning, and access reviews
- Compliance and Reporting: Centralized audit and governance dashboards
Pros:
- A managed-service model to reduce operational burden on internal IT teams
- Good multi-vendor IAM unification capabilities
- Helpful for enterprises with complex, multi-tool IAM stacks
Cons:
- Simeio's managed-service model may not suit organizations that prefer self-service platforms. It's also less focused on developer-native or CI/CD-specific identity concerns.
Pricing: Enterprise managed-service pricing; contact for quotes.
Enterprise Fit: Simeio is a quality tool for enterprises that need managed identity orchestration across multiple IAM vendors.
Website: simeio.com
4. Auth0 (Okta)
Category: Developer-centric identity platform with orchestration capabilities
Auth0, now part of Okta, provides a developer-first identity platform with flexible orchestration through its "Actions and Rules" framework. This allows teams to build custom identity flows, integrate third-party services, and enforce policies programmatically within authentication and authorization pipelines.
Core Features:
- Actions Framework: Serverless extensibility to customize identity flows
- Universal Login: Centralized, customizable authentication experience
- Machine-to-Machine (M2M) Authentication: OAuth2 client credentials flow for service-to-service authentication
- Multi-Tenant Support: An "organizations" feature for B2B identity orchestration
- Pre-Built Integrations: Marketplace of connectors for MFA, fraud detection, enrichment, and more
Pros:
- Very developer-friendly with a strong API and extensibility
- Flexible Actions framework for custom orchestration logic
- Strong community and marketplace ecosystem
Cons:
- Auth0's orchestration is code-driven, which typically requires developer involvement. It's also not a dedicated orchestration fabric for unifying multiple IdPs, nor does it offer secrets exposure detection.
Pricing: Free tier plus paid plans; enterprise pricing available through Okta.
Enterprise Fit: Auth0 is excellent for developer-led organizations and SaaS companies that need flexible, programmable identity orchestration.
Website: auth0.com
5. Microsoft Entra ID (Azure AD)

Category: Enterprise IAM platform with orchestration and governance
Microsoft Entra ID (formerly Azure Active Directory) provides identity orchestration through conditional access policies, identity governance workflows, and workload identity management. As part of the Microsoft ecosystem, it's the default identity layer for most Azure customers.
Core Features:
- Conditional Access: Policy-based orchestration for adaptive authentication and authorization
- Identity Governance: Entitlement management, access reviews, and lifecycle workflows
- Workload Identities: Managed identities and service principal governance for Azure resources
- Cross-Cloud Federation: Multi-cloud identity federation with external IdPs
- Verified ID: Decentralized identity verification capabilities
Pros:
- Deep integration with Microsoft and Azure ecosystems
- Strong conditional access and governance capabilities
- Native workload identity support for Azure-based architectures
Cons:
- Microsoft Entra ID's orchestration capabilities are strong within the Microsoft ecosystem but limited for multi-vendor, multi-IdP orchestration outside of Azure. The platform doesn't provide secrets exposure scanning either.
Pricing: Included with Microsoft 365 and Azure subscriptions; premium tiers (P1, P2) for advanced governance.
Enterprise Fit: Microsoft Entra ID is essential for Microsoft-centric enterprises, but requires supplementation for multi-IdP orchestration and secrets security.
Website: microsoft.com/en-us/security/business/identity-access/microsoft-entra-id
6. TrustBuilder

Category: European identity orchestration and access management
TrustBuilder is an identity orchestration platform with a visual workflow editor. Customers can use it to design tailored identity management flows. The platform also emphasizes European data sovereignty and GDPR-aligned identity governance to enhance the user experience.
Core Features:
- Workflow Editor: Visual interface for building custom identity and access management flows
- Adaptive Authentication: Context-aware, risk-based authentication policies
- API Gateway Integration: Identity-aware API security and access control
- Multi-Protocol Support: SAML, OIDC, OAuth2, and legacy protocol bridging
- Data Sovereignty: European-hosted with GDPR compliance focus
Pros:
- Strong visual workflow orchestration capabilities
- A good fit for European enterprises with data sovereignty requirements
- Solid API security integration
Cons:
- TrustBuilder offers a smaller ecosystem and partner network than many of the major US-based identity platforms. It also has limited visibility into NHI exposure and secrets sprawl.
Pricing: Enterprise commercial pricing.
Enterprise Fit: TrustBuilder is suitable for European enterprises that need identity orchestration with data sovereignty and GDPR compliance.
Website: trustbuilder.com
7. Tech Prescient (Identity Confluence)
Category: Customized identity orchestration and automation
Tech Prescient offers Identity Confluence, a customizable identity orchestration platform that automates user lifecycles, access policies, and identity governance across hybrid environments.
Core Features:
- Lifecycle Automation: End-to-end orchestration of joiner, mover, and leaver processes
- Custom Policy Engine: Tailored policy orchestration for complex enterprise requirements
- Multi-System Integration: Connects on-premises and cloud identity systems
- Access Governance: Role-based and policy-based access management
- Consulting and Implementation: White-glove implementation services for detailed deployments
Pros:
- Highly customizable orchestration for complex enterprise needs
- Strong consulting and implementation support
- Good hybrid environment coverage
Cons:
- Tech Prescient is more services-oriented than a pure SaaS product. Because of this, it may not suit organizations that need a self-service, cloud-based orchestration platform.
Pricing: Custom enterprise pricing with services engagements.
Enterprise Fit: Tech Prescient is good for enterprises with complex, customized identity orchestration requirements and hybrid environments.
Website: techprescient.com
8. SailPoint
Category: Identity governance and orchestration platform
SailPoint is a leading identity governance and administration (IGA) platform. It has recently expanded into identity orchestration too, with workflow automation, AI-driven access recommendations, and lifecycle orchestration features across human and non-human identities.
Core Features:
- Identity Governance: Comprehensive access certification, role management, and policy enforcement
- Workflow Orchestration: Automated provisioning, deprovisioning, and access request workflows
- AI-Driven Recommendations: Machine learning for access outlier detection and role optimization
- Non-Human Identity Support: Service account governance and bot/RPA identity management
- Multi-Cloud Connectors: Integrations with major cloud, SaaS, and on-premises systems
Pros:
- Market-leading IGA capabilities with strong orchestration workflows
- AI-driven insights for access governance
- A broad connector ecosystem
Cons:
- SailPoint is more of an IGA platform than a dedicated orchestration engine. Also, the tool doesn't provide secrets exposure detection or developer-workflow-native scanning.
Pricing: Enterprise commercial pricing; SaaS (SailPoint Atlas) and on-premises options available.
Enterprise Fit: SailPoint is a quality choice for enterprises that need identity governance as their foundation for orchestration, especially at scale.
Website: sailpoint.com
9. Saviynt
Category: Cloud-native identity governance and orchestration
Saviynt provides cloud-native identity governance with orchestration capabilities, including lifecycle automation, fine-grained access controls, and application access governance for both human and machine identities.
Core Features:
- Cloud-Native IGA: Built-for-cloud identity governance and lifecycle management
- Application Access Governance: Fine-grained entitlement management across SaaS and cloud resources
- Identity Lifecycle Orchestration: Automated joiner, mover, and leaver workflows, and access certifications
- Privileged Access Governance: Integrated PAM capabilities for privileged account oversight
- Risk-Based Analytics: Continuous risk scoring and access intelligence
Pros:
- Strong cloud-native architecture with comprehensive IGA
- Good integration of IGA and PAM in a single platform
- Risk-based analytics for identity governance
Cons:
- Saviynt is more about IGA than orchestration. It's also less focused on developer workflows, CI/CD pipelines, and secrets exposure scanning than other apps.
Pricing: Enterprise SaaS pricing.
Enterprise Fit: Saviynt is a solid option for cloud-first enterprises that need identity governance with orchestration and PAM capabilities.
Website: saviynt.com
10. ConductorOne
Category: Identity security and access orchestration
ConductorOne enables identity security by automating access reviews, streamlining provisioning, and orchestrating access governance workflows. The platform makes identity security practical and fast for modern teams.
Core Features:
- Automated Access Reviews: Streamlined certification campaigns with intelligent recommendations
- Access Request Workflows: Self-service access requests with policy-based approvals
- Provisioning Orchestration: Automated provisioning and deprovisioning across connected systems
- Identity Graph: Visibility into who has access to what across SaaS and cloud apps
- Non-Human Identity Visibility: Service account and bot identity discovery
Pros:
- Fast to deploy with a modern, lightweight approach
- Strong automated access review capabilities
- Good NHI visibility for service accounts
Cons:
- ConductorOne is a relatively new platform, so its connector ecosystem is still growing. The tool is also less focused on legacy and on-premises identity orchestration, and does not address secrets exposure detection.
Pricing: Commercial SaaS pricing; free tier available.
Enterprise Fit: ConductorOne is great for modern, cloud-first teams that need fast, lightweight identity security and access orchestration.
Website: conductorone.com
11. Okta (Workforce Identity Cloud)

Category: Enterprise IAM platform with orchestration workflows
Okta's Workforce Identity Cloud provides SSO, adaptive MFA, lifecycle management, and identity governance with orchestration capabilities. It does all this through Okta Workflows, a no-code automation engine that enables users to build complex identity processes.
Core Features:
- Okta Workflows: No-code identity automation with a drag-and-drop flow builder
- Universal Directory: Centralized identity storage that connects multiple sources
- Adaptive MFA: Context-aware multi-factor authentication with suspicious behavior detection
- Lifecycle Management: Automated provisioning and deprovisioning across apps
- Integration Network: Over 7,000 pre-built app integrations
Pros:
- Massive integration ecosystem
- Powerful no-code Workflows engine for identity automation
- Strong adaptive access and MFA capabilities
Cons:
- Orchestration stays within the Okta ecosystem, so it isn't a true multi-IdP fabric. The tool doesn't provide secrets exposure detection or NHI credential scanning either.
Pricing: Tiered commercial pricing; enterprise plans available.
Enterprise Fit: Okta's Workforce Identity Cloud offering is best for enterprises that already use Okta as a primary IdP and need orchestration within the same ecosystem.
Website: okta.com
The Secrets Security Layer That Every Orchestration Stack Needs
The identity orchestration tools we covered help customers manage machine and user identities across providers, directories, and systems—and they do it very well. But none of them offer secrets security and NHI exposure intelligence. Using them in isolation will weaken your company's security posture. Fortunately, Gitguardian fills the gap for many organizations.
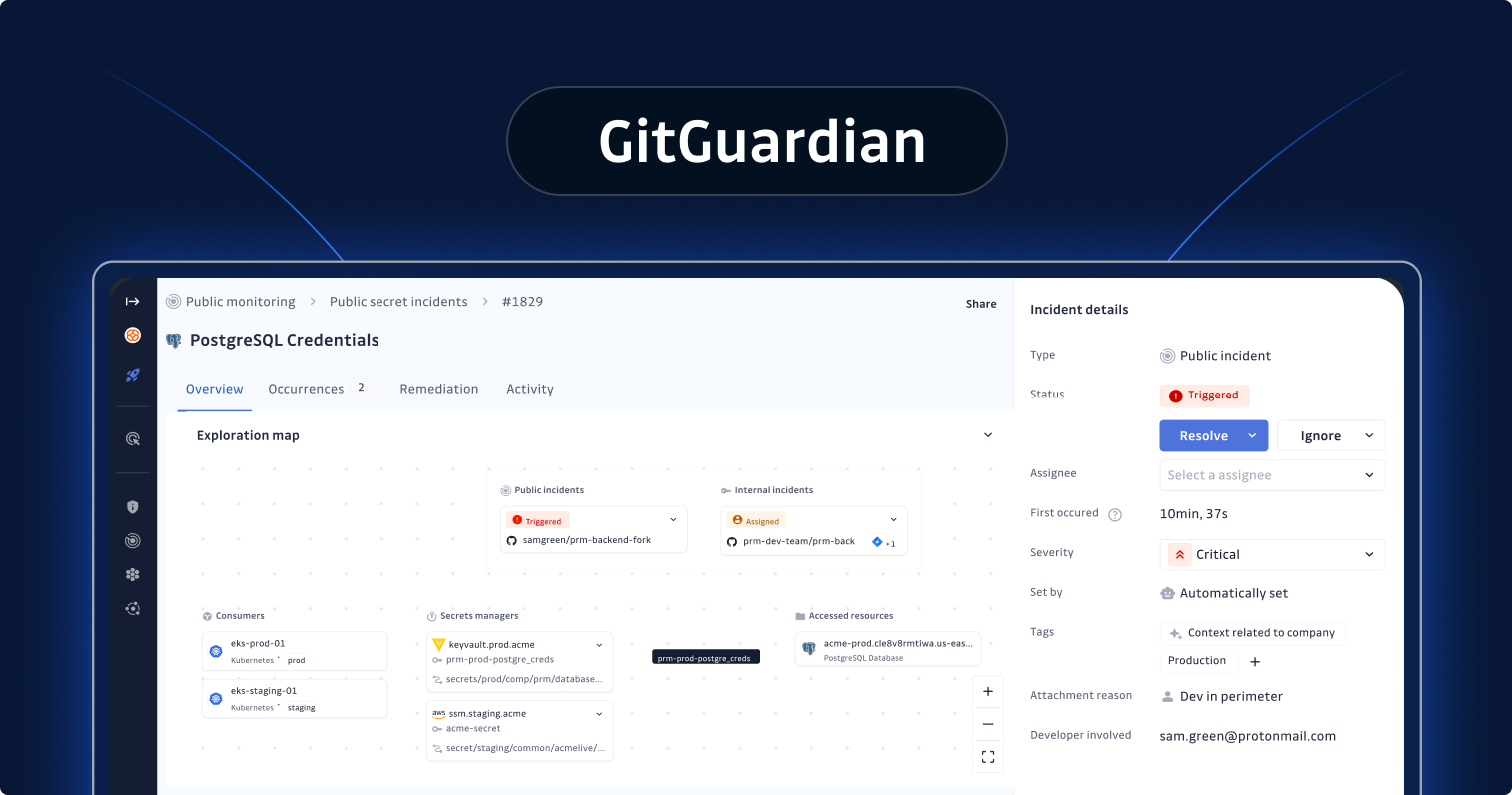
GitGuardian
Category: Secrets security and NHI exposure intelligence for identity orchestration
GitGuardian is an enterprise-grade secrets security and non-human identity exposure platform that provides the critical security layer that identity orchestration stacks need.
While the orchestration platforms above can unify and automate identity flows, GitGuardian makes sure the credentials, API keys, tokens, and service account secrets moving through those flows aren't compromised. As such, it delivers unmatched exposure detection across repositories, CI/CD pipelines, collaboration tools, and public sources. These facts make GitGuardian the perfect complement to any identity orchestration deployment.
Core Features:
- Internal Secrets Monitoring: Real-time and historical scanning across all repositories, including full git history, to find hardcoded secrets before they cause damage
- Public Secrets Monitoring: Continuous monitoring of public GitHub to detect accidental exposure of organizational credentials before attackers find them
- NHI Governance: Organization-wide visibility into non-human identity exposure, secret sprawl mapping, and remediation workflow orchestration
- CI/CD Pipeline Scanning: Integration with developer workflows through the GitGuardian CLI (ggshield) to catch secrets before they enter source control
- Collaboration Tool Coverage: Scanning across Slack, Jira, Confluence, and Teams for exposed credentials that bypass code-based controls
- Vault Integration: Integrations with HashiCorp Vault, CyberArk, and cloud-native vaults for centralized visibility and migration guidance on hardcoded secrets
- Detection Accuracy: ML-enhanced detection with entropy and contextual validation to deliver a high signal-to-noise ratio and continuous detector updates for cloud, SaaS, and custom secret patterns
- Agentic AI Security: Protection across the AI development value chain, including AI-powered CLI tools and autonomous agents, to minimize exposure risks in agentic workflows
Pros:
- Unmatched breadth of exposure detection (public + internal + collaboration tools + CI/CD)
- Advanced secrets intelligence for risk prioritization
- Strong vault ecosystem integrations
- High detection accuracy with low false positives
- Enterprise-ready governance and reporting
- Fills the exposure-detection gap left by identity orchestration platforms
Cons:
- GitGuardian specializes in secrets exposure detection and NHI security, not identity orchestration workflow design. Think of it as a complement to, not a replacement for orchestration engines.
Pricing: Free Starter tier, plus Teams and Custom enterprise pricing.
Enterprise Fit: GitGuardian is essential for any large company that deploys identity orchestration and wants to ensure the credentials flowing through these workflows are secure and properly governed. Our platform is particularly well-suited for mid-market and enterprise organizations operating in multi-cloud, Kubernetes-heavy, and CI/CD-driven environments.
Website: gitguardian.com
Implementation Strategy for Enterprise Identity Orchestration
Follow this three-phase approach to implement an identity orchestration tool for your enterprise.
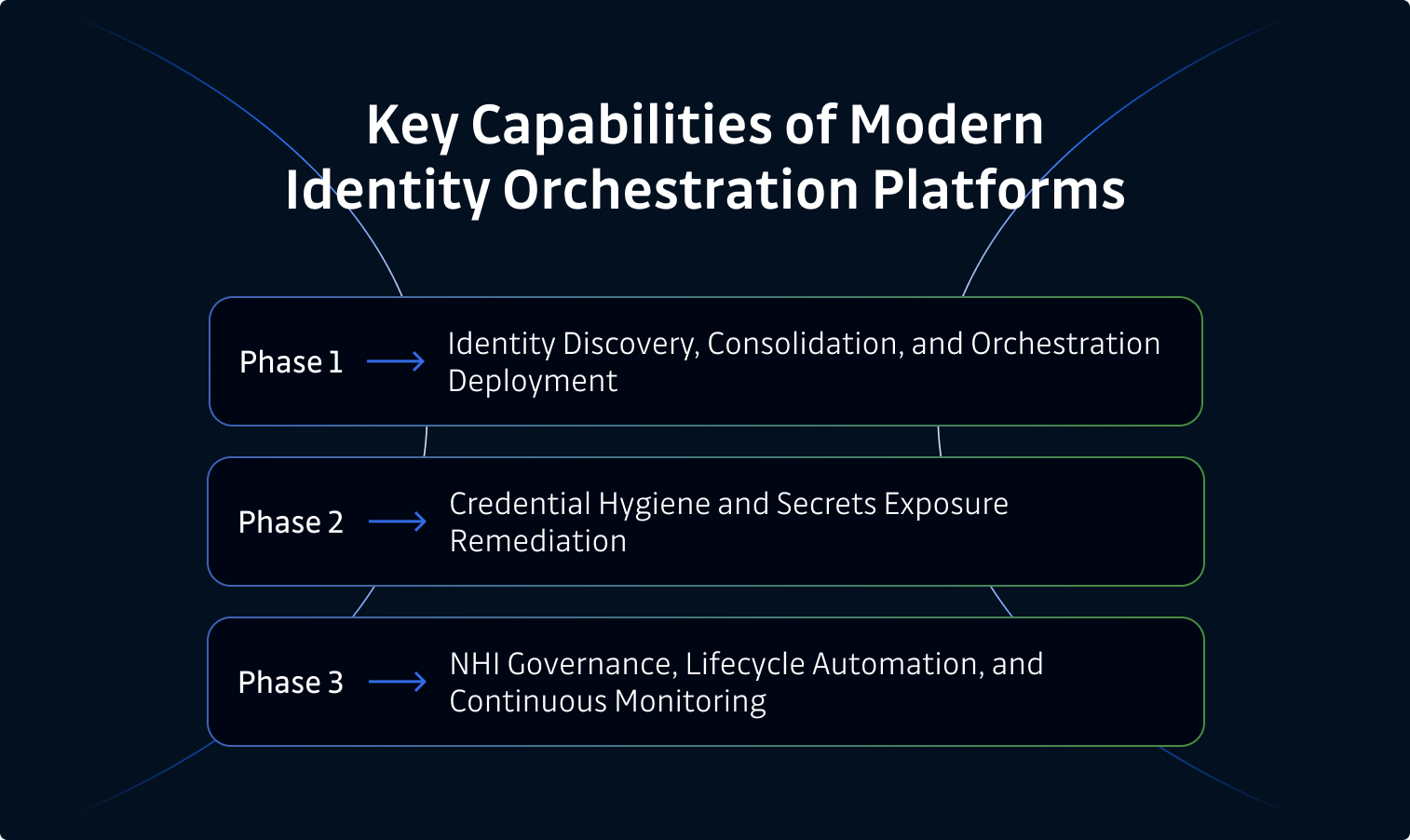
Phase 1: Identity Discovery, Consolidation, and Orchestration Deployment
The Objective: Establish a unified view of your identity landscape and deploy orchestration.
Start with an inventory of all identity providers, directories, access management systems, and federated trust relationships across cloud, on-premises, and SaaS environments. Then, map identity-to-resource relationships to see the scope of human and non-human access paths.
From there, select and deploy an identity orchestration company that's aligned with your architecture, whether that's an identity fabric, no-code engine, or IGA-based approach. Finally, bridge legacy and modern identity protocols (LDAP, SAML, OIDC, SCIM) to enable unified policy enforcement and implement centralized adaptive access policies across all connected identity systems.
The Executive Outcome: A unified identity control plane with consistent policies that can replace fragmented, manual management across multiple siloed systems.
Phase 2: Credential Hygiene and Secrets Exposure Remediation
The Objective: Confirm the credentials that pass through your identity flows aren't compromised.
Scan all source code repositories, including full git history, CI/CD pipelines, and collaboration tools for leaked secrets and exposed credentials. Next, identify and remediate hardcoded API keys, tokens, and service account credentials, especially those that are now connected via orchestration workflows.
Finally, establish baseline credential hygiene metrics and mean-time-to-remediation (MTTR) targets, then deploy continuous secrets monitoring to detect new exposures in real time.
The Executive Outcome: Less risk that orchestration will worsen the impact of previously exposed credentials, and a cleaner credential posture across your entire identity stack.
Phase 3: NHI Governance, Lifecycle Automation, and Continuous Monitoring
The Objective: Extend orchestration to non-human identities and automate credential lifecycle management for long-term operational maturity.
Discover and inventory all non-human identities, including service accounts, API keys, OAuth apps, certificates, and workload identities, within orchestration workflows. Then, automate secret rotation, certificate renewal, and just-in-time access provisioning for machine identities.
Next, enforce least-privilege policies for all NHIs connected via the orchestration layer, and integrate secrets exposure monitoring with orchestration and governance dashboards.
Finally, establish clear ownership models for NHIs across AppSec, IAM, and Platform Engineering teams. Doing so turns identity operations into a mature, self-sustaining program.
The Executive Outcome: End-to-end identity orchestration that covers human and non-human identities, with automated lifecycle management, least-privilege enforcement, and continuous exposure detection embedded into the operating model.
The Future of Identity Orchestration
The digital security space is always changing. Here are several trends that are reshaping the identity orchestration market.
- Identity fabric convergence. Dedicated orchestration platforms, IGA tools, and PAM solutions are converging into unified platforms. Organizations that rely on three separate tools for orchestration, governance, and privileged access management will likely see these capabilities consolidated into single-vendor platforms over the next few years.
- AI-driven orchestration. Autonomous identity workflows, anomaly detection, and adaptive policy recommendations driven by machine learning are hitting the market. The best orchestration platforms make access decisions in real time based on behavioral signals, not static policy rules.
- Non-human identity as a first-class concern. For years, companies viewed NHI governance as secondary to human identity management. That's changing. As machine identities proliferate across Kubernetes clusters, CI/CD pipelines, and agentic AI systems, orchestration platforms that lack strong NHI coverage will fall short of enterprise requirements.
- Secrets security integration becomes standard. Detection of exposed credentials is moving from a specialized security function to an expected layer in identity orchestration deployment. The connection between leaked secrets and identity-based breaches is hard to ignore, so organizations will build secrets exposure monitoring into their orchestration strategy.
- Decentralized and verifiable identity. Decentralized identity verification capabilities are beginning to integrate with enterprise orchestration workflows. This enables new patterns for cross-organization identity federation and user verification without centralized identity stores.
Improve Identity Operations
The organizations that approach identity orchestration as a platform problem, not a point-solution problem, and treat credential hygiene as a prerequisite rather than an afterthought, will be better positioned to reduce identity-related risk at scale.
If you're currently deploying identity orchestration workflows, secure the credentials that flow through them. Book a demo of GitGuardian to see how our platform fits into your identity security strategy.
FAQs: Identity Orchestration and Access Management
What is identity orchestration, and why does it matter?
Identity orchestration is the practice of connecting, coordinating, and automating identity management across multiple systems through a unified control plane. It matters because modern enterprises operate across fragmented identity providers, directories, and cloud platforms. Without orchestration, organizations face inconsistent access policies, manual lifecycle management, identity blind spots, and an expanded attack surface.
What is the difference between identity orchestration and identity governance (IGA)?
Identity governance (IGA) focuses on access certification, role management, and compliance reporting. Identity orchestration is broader. It connects and automates identity workflows across multiple IAM systems, including IGA platforms. Think of orchestration as the automation and unification layer that sits above individual governance tools and coordinates how they interact.
How does identity orchestration handle non-human identities?
Most orchestration platforms are designed for human identity workflows. However, mature platforms have expanded to include service account governance, API key lifecycle management, and workload identity orchestration. For comprehensive NHI security, enterprises should layer a secrets security platform to detect exposed or compromised machine credentials that orchestration can't identify.
Do identity orchestration platforms detect leaked secrets or exposed credentials?
Generally, no. Identity orchestration platforms manage identity flows and access policies, but don't scan repositories, CI/CD pipelines, or collaboration tools for leaked API keys, tokens, or hardcoded secrets. This is a critical gap that requires a dedicated secrets security platform like GitGuardian.
How do identity orchestration tools integrate with existing IAM stacks?
Orchestration platforms sit above existing IAM tools. They connect to IdPs like Okta and Azure AD, directories like LDAP and Active Directory, IGA platforms like SailPoint and Saviynt, PAM solutions, and cloud IAM through standard protocols (SAML, OIDC, SCIM) and pre-built connectors. This means organizations can implement orchestration without disruption to existing systems.
What ROI can enterprises expect from identity orchestration?
Key ROI drivers include reduced operational overhead from manual identity management, faster onboarding and offboarding cycles, consistent policy enforcement that minimizes access-related incidents, improved audit and compliance readiness, and reduced risk from identity sprawl and overprivileged accounts. Much of the time-consuming manual work that IT teams do goes away when they put mature orchestration in place.
Can identity orchestration support zero-trust architectures?
Yes. Identity orchestration is a key enabler of zero-trust by centralizing policy enforcement, enabling adaptive and context-aware access decisions, and providing continuous verification across all identity interactions. Combined with secrets security for credential integrity, it forms a strong foundation for zero-trust identity. Orchestration provides the control plane, while secrets security ensures the credentials running through said control plane haven't been compromised.