A new exfiltration endpoint is used: https://models.litellm[.]cloud/
Other IoCs stay the same.
On March 24, the campaign targeted Checkmarx KICS scanner and poisoned it with an infostealer.
The Trivy story is moving quickly, and the latest reporting makes one thing clear: this is no longer just a GitHub Actions tag hijack. What started as a compromise of trivy-action, setup-trivy, and the v0.69.4 release has expanded into malicious Docker Hub images, a suspected service-account compromise spanning Aqua’s internal GitHub organization. Researchers tied the new artifacts to the same TeamPCP infostealer seen earlier in the campaign, and Aqua has said the March 19 incident reused credentials retained from the previous breach because remediation was not fully atomic.
That matters because it sharpens the contrast with Shai Hulud. Both attacks targeted the CI/CD pipeline. Both went after secrets instead of the application itself. Both used GitHub as a practical exfiltration surface because GitHub traffic looks routine in engineering environments. But Trivy looks like a fast-moving credential theft campaign that keeps finding new ways to capitalize on. Shai Hulud was a broader supply chain operation designed to persist, propagate, and cause downstream damage.
Attack Timeline
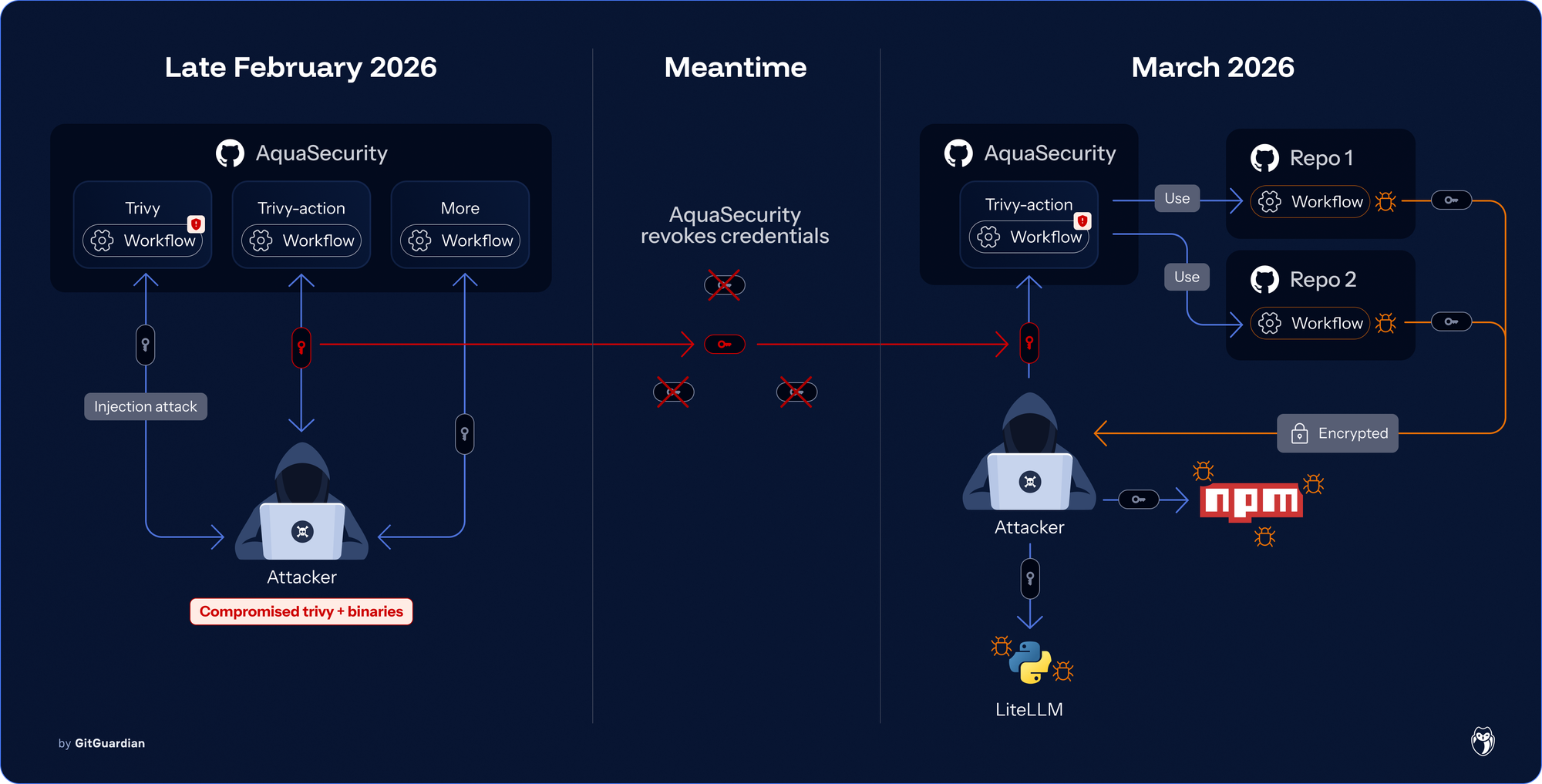
Late February 2026 — Initial CI Compromise
An automated bot (“hackerbot-claw”) exploited a misconfigured workflow, stealing a privileged Personal Access Token (PAT) from the CI environment. Using that credential, the attacker pushed a malicious artifact to the Trivy VS Code extension on Open VSX.
March 1, 2026 — First Disclosure & Partial Remediation
Aqua Security publicly disclosed the incident via a GitHub discussion and rotated credentials. However, subsequent investigation revealed the rotation was incomplete, leaving residual access paths still open to the attacker.
March 19, 2026 — Supply-Chain Weaponization
Using still-valid credentials and a compromised aqua-bot service account, the attacker published a malicious Trivy binary release (v0.69.4) and force-pushed malicious commits to 75–76 of 77 tags in aquasecurity/trivy-action and all 7 tags in aquasecurity/setup-trivy, silently turning pinned tags into payload delivery channels. The injected payload contained two Python infostealers. One was specially crafted to run on a CI/CD runner and exfiltrated sensitive elements from the runner process memory and environment. The second stealer, more generic, exfiltrated SSH keys, cloud tokens, and other secrets, mostly collected from the local file system. Both payloads sent the information to an attacker-controlled domain or to public GitHub repositories as a backup channel.
March 20–22, 2026 — Public Post-Mortems & Guidance
Aqua Security released detailed post-incident blogs with a formal attack timeline, indicators of compromise (IoCs), a list of compromised tags, and guidance for rotating CI/CD and cloud credentials.
Trivy was surgical. Shai Hulud was systemic.
The original Trivy compromise was already serious. The attacker force-pushed 75 version tags into aquasecurity/trivy-action, turning trusted version references into a malware-delivery path for any workflow pinned to a tag rather than a commit SHA. The payload harvested environment variables and secrets from runner memory, searched self-hosted systems for cloud and infrastructure credentials, encrypted the results, and exfiltrated them to attacker-controlled infrastructure or as a release file to public GitHub repositories created in the victim’s own account under the name tpcp-docs. Because the legitimate Trivy scan still ran afterward, many users would have seen normal output and missed the theft entirely.
Shai Hulud 2.0 operated on a different level. It backdoored npm packages, used TruffleHog offensively to harvest local secrets, leveraged self-hosted GitHub runners as command-and-control infrastructure, propagated into downstream packages, and carried a destructive wiper. That is a bigger playbook and a wider blast radius. Trivy moved fast through trusted automation and harvested what it could reach. Shai Hulud was built to spread.
The fresh reporting on Trivy makes that distinction even more useful. The campaign now appears to have expanded from GitHub Actions into Docker images and follow-on malware, including a worm that spreads through SSH keys and exposed Docker APIs, plus a Kubernetes wiper in specific environments. That does not make Trivy the same as Shai Hulud. It makes Trivy a good example of how a credential theft operation can evolve when remediation leaves one valid path behind.
The real lesson is remediation, not just detection
The biggest takeaway here is not that secrets were stolen. That part is already obvious. The bigger lesson is that incomplete cleanup turns one breach into a campaign. Aqua’s own account of the incident points to compromised credentials retained from the earlier breach and a rotation process that did not fully sever access. In practice, that gap is the line between containment and recurrence.
That is where strong secrets security stands out. Teams need to detect exposed credentials quickly, but detection is only the start. They also need to know which machine identities were reachable from that workflow, which of those secrets are still active, what each credential unlocks, and which ones must be rotated first to cut off attacker movement. Public monitoring matters here because both Trivy and Shai Hulud used public GitHub repositories as part of the exfiltration path. Early alerting matters because once an attacker starts harvesting secrets inside CI, every minute counts. Governance matters because non-human identities, especially long-lived service accounts and PATs, create the bridges attackers use to move from one repo, org, or registry to the next.
That is the sharper value proposition in this story. The teams that recover fastest are not the ones that merely discover a leak. They are the ones that can trace blast radius, prioritize rotation, verify remediation, and prove that the same credential cannot be reused tomorrow.
Why this matters now
Trivy and Shai Hulud belong in the same conversation because they both show where modern supply chain attacks pay off. They do not need to own your application. They need to reach the systems that build, sign, scan, and deploy it. Once they get there, secrets do the rest.
But they should not be described as the same kind of event. Shai Hulud was a sprawling, self-propagating supply chain operation. Trivy was initially a more surgical compromise of trusted automation, and the last 48 hours of reporting show what happens when that kind of operation meets incomplete remediation and a reusable service account. The result is not just one bad release. It is a long tail of exposure across GitHub Actions, Docker images, internal orgs, and cloud infrastructure.
That is the story prospects should remember. The hard problem is no longer finding a secret after it leaks. The hard problem is stopping that secret from becoming the attacker’s next foothold.






![Shai-Hulud 2.0 Exposes Over 33,000 Unique Secrets [Updated Nov, 27]](https://storage.ghost.io/c/42/5d/425d266f-cf99-406e-9436-597a19bed011/content/images/size/w600/2025/11/shai-hulud--2--1.png)

