On June 6, Verizon unveiled its 2023 Data Breach Investigations Report, DBIR. This comprehensive report summarizes their findings about incidents from all industries and companies of all sizes. Unfortunately, if you read the previous years' reports, much of the information will look familiar. As they state, "We don't require bad actors to evolve their tactics because the old ones still work just fine." This also mirrors our State of Secrets Sprawl Report findings, where the trend lines for the same credential-related issues keep going up.
What is the DBIR?
The 2023 DBIR examined 16,312 incidents, of which 5,199 were confirmed data breaches, taking place between the beginning of November 2021 and the end of October 2022. This is the 16th annual report issued by the Verizon Threat Research Advisory Center, VTRAC, which is a group inside Verizon that helps teams "mitigate cyber threats from their networks, applications, and devices."
This report's release also marks the 20th year anniversary of the center's creation, making them industry leaders in this area of research. This report has become one of the most anticipated reports, as it helps organizations understand what threats they are facing and how to best prepare for those eventualities.
Top stats of the 2023 report
The report shows that the top three attack patterns over the previous year were:
- System Intrusion - Complex attacks that leverage malware and/or hacking to achieve their objectives, including deploying Ransomware.
- Basic Web Application Attacks - Attacks are against a Web application, and after the initial compromise, they do not have a large number of additional Actions. It is the “get in, get the data and get out” pattern.
- Social Engineering - Psychological compromise of a person that alters their behavior into taking an action or breaching confidentiality.
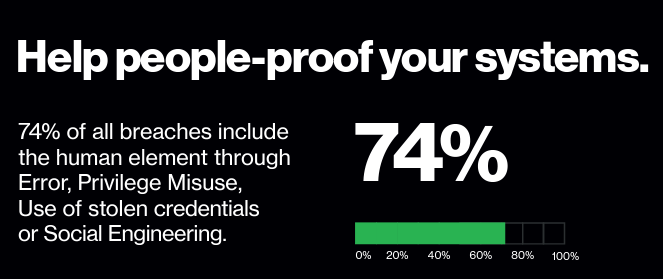
Humans are most often the cause
According to the report, 74% of all breaches include the human element, with people being involved either via Error, Privilege Misuse, Use of stolen credentials, or Social Engineering.
External actors were responsible for 83% of reported breaches, with the rest being carried out by a mix of internal personnel and partners, third parties sharing a business relationship with the organization. The vast majority of breaches, around 75%, involved organized crime, while less than 10% involved nation-state affiliated actors.
It's all about the money
While it should come as no surprise that most cybercriminals are driven by financial gains, it is alarming that this motivating factor has shown growth year over year, up to 94.6% in breaches. Ransomware was again one of the top action types present in breaches, present in 24% of cases. The median loss more than doubled to $26,000, and the highest reported losses hitting $2.25 million. Additionally, the overall costs of recovering from a ransomware incident are increasing.
Credentials use and leakage during braches
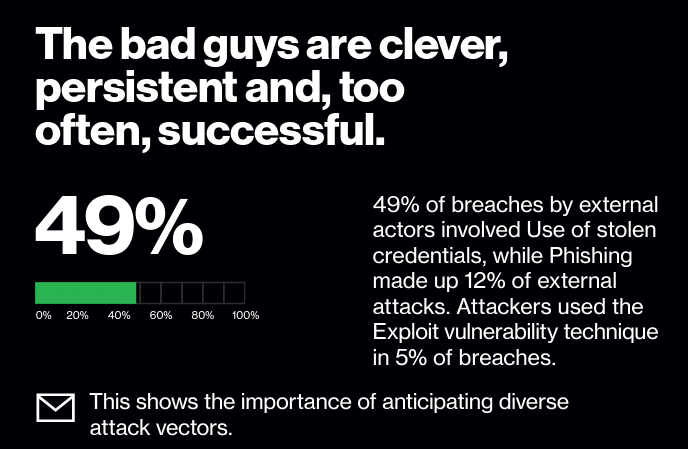
86% of the breaches involved the use of stolen credentials in Basic Web Application Attacks, representing approximately one-fourth of the dataset and the second most common attack pattern. This is sadly not too much of a surprise given the fact that credentials were second only to personal data in types of data leaked during breaches.
The report shows that stolen credentials were leveraged in nearly half, 49%, of the breaches for initial access to an organization’s systems.
Credentials are not just leaking from our code or logs either. Unfortunately, plaintext credentials are also commonly found in inboxes. 41% of breaches involve mail servers, and sadly many contain credentials to some other system. This should remind us all to never, ever email plaintext passwords, API keys, or any other secret.
What can we do to protect our organizations?
One of the main ways the report suggests you can protect yourself and your organization is to implement multi-factor authentication, MFA. While not a silver bullet, when enforced properly, MFA can be very effective in reducing the effectiveness of attacks that lead to credential theft. Jen Easterly, Director of U.S. Cybersecurity and Infrastructure Security Agency, is quoted in the report: "In particular, it’s critical that “high-value targets” like system administrators and Software as a Service (SaaS) staff use phishing- resistant MFA."
Finding and removing your plaintext credentials is critical
The best secrets are ones that you never see and are rotated often. GitGuardian can help you keep your secrets out of places where attackers can exploit them. The GitGuardian Secret Detection platform can help you quickly find any and all hardcoded secrets in your repositories, giving you intelligence on the location and age of the credential, if the secret is exposed publicly, and in many cases, if it is still valid. Your teams can quickly triage and tackle the job of removing, rotating, and safely storing credentials in tools like Vault by HashiCorp or Doppler.
Even better than removing credentials from your work is never committing them in the first place. This is why we simplify scanning for secrets on the command line with our open source CLI, ggshield. Developers can even easily automate the process of scanning with our pre-commit git hooks.
No matter how large your organization, how many development teams you have, or how many repositories you manage, GitGuardian can help you reduce the chances attackers will be successful.