Let's face it: acquiring enterprise security software can feel daunting. There are so many competing security priorities in the enterprise, making it hard to know which ones to address and in what order. Once you are ready to evaluate solutions, it can be confusing to know where to start. This includes secrets security, both on the storage and management side and the detection and leak remediation side.
For those who might be tackling secrets security now or in the near future, we want to shine a light on the path we have seen many customers take, moving from free, personal use of the GitGuardian Secrets Detection Platform all the way through to successful enterprise adoption. While every organization is different, and your circumstances might be unique to you, we are happy to share what we have learned from our customers over the years.
Free for individuals
At GitGuardian, we want every developer to keep their secrets secret and stop credentials from leaking into their shared code. This is why we make GitGuardian Secrets Detection and ggshield, our CLI, absolutely free for individual developers. Many developers use GitGuardian when they are ready to release code into the wild, especially as open source projects, to make sure they are not opening any access to unintended users.
With just a few commands, any developer working on their personal projects or on open source contributions can add a handy pre-commit or pre-push git hook to their repositories to automatically prevent the over 400 types of secrets from making it into their git history.
Free for small teams
If your team has 25 developers or fewer, you also qualify to use our free tier of the GitGuardian Secrets Detection platform. We do not restrict the power of our scanning tools for free customers, providing the same level of enterprise protection for all projects, large and small. What you see is what you get with GitGuardian.
While some teams discover the GitGuardian platform early in their journey, many enterprises are beyond this phase of growth when they decide to tackle secrets sprawl; we are here to help in the process.

A free trial for your larger team's projects
When adopting or evaluating any enterprise solution, it is a good idea to start small and view the process as a journey, not a rushed moonshot style mission. Yes, you should act with urgency to attain better security, but starting with small, manageable efforts is preferable to the extremes of doing nothing or abandoning other ongoing security efforts to focus on what might be a whale of a task.
Many teams start evaluating the GitGuardian Secrets Detection platform by focusing on a single project or repository they deeply understand. When you first add a new repo to your defined perimeter, the platform will perform a historical scan. This deep scan will look through every branch and every commit in your project's git history, uncovering any and all hardcoded secrets lurking below the surface. This is especially useful for inherited legacy code and decades-old big balls of mud.
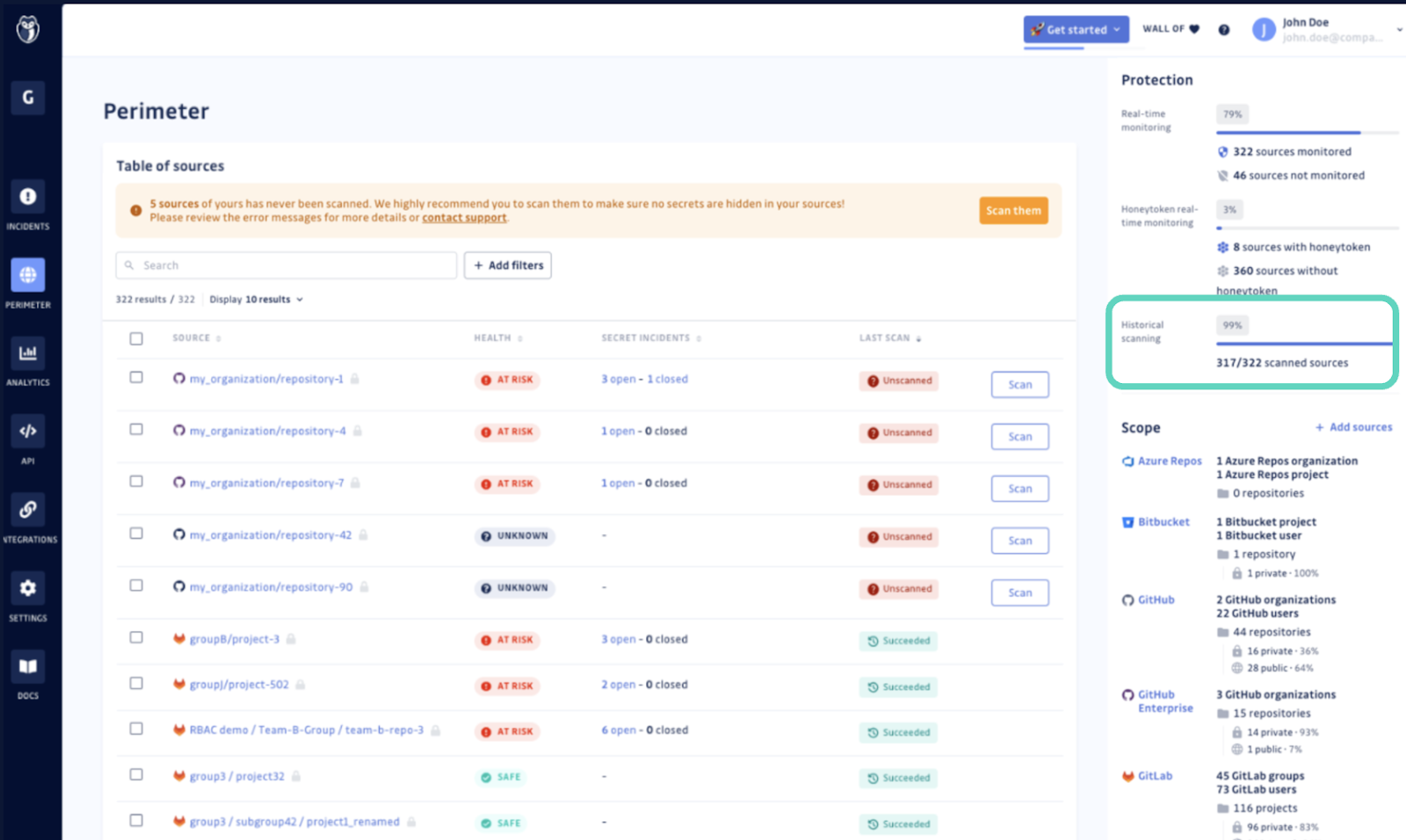
Many teams use these historical findings as a baseline, showing if plaintext secrets in the code are a recurring, ongoing issue.
Testing for new secrets over time
Once a repository has been added to your GitGuardian perimeter, the platform will scan for any newly added secrets. Many teams will set a period of days or weeks to monitor for new issues and to test sample secrets that represent the real credentials that they worry will slip into the wrong hands. This is when teams also test our ability to scan Slack channels for secrets.
Alerting that works for you
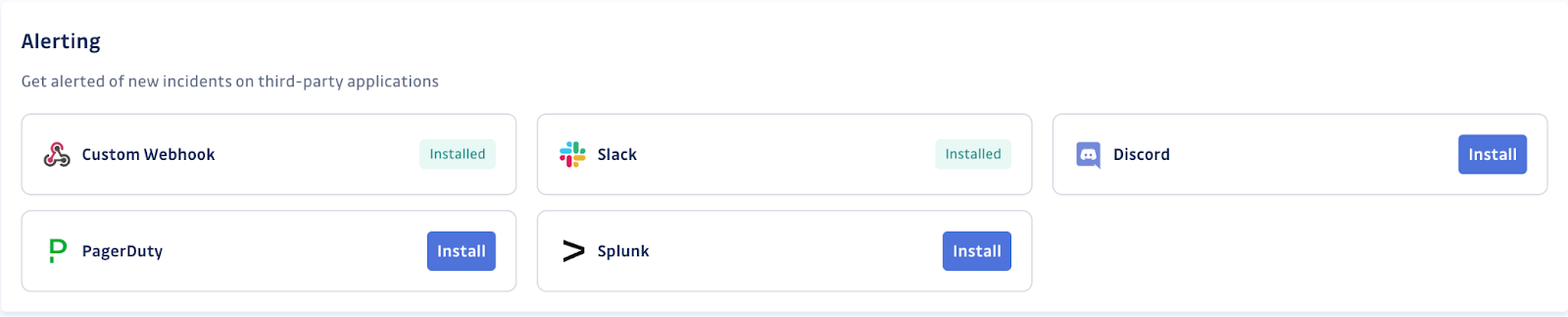
It is during these times that many teams will also test the alert integrations. While all alerts will, by default, trigger a warning email, most teams want to make sure any alerts also get added to the right channel on platforms like Slack or Discord or get those alerts automatically sent to services like PagerDuty or Splunk. You can also create custom webhooks that fire off the alert anywhere you need, into any custom SEIM or orchestration tooling.
Remediation is challenging
For anyone evaluating an enterprise scanning platform, the question should not only be, "Can it find issues?" but instead, "Can it help us find and solve our issues?" With GitGuardian, the answer is a resounding "Yes!"
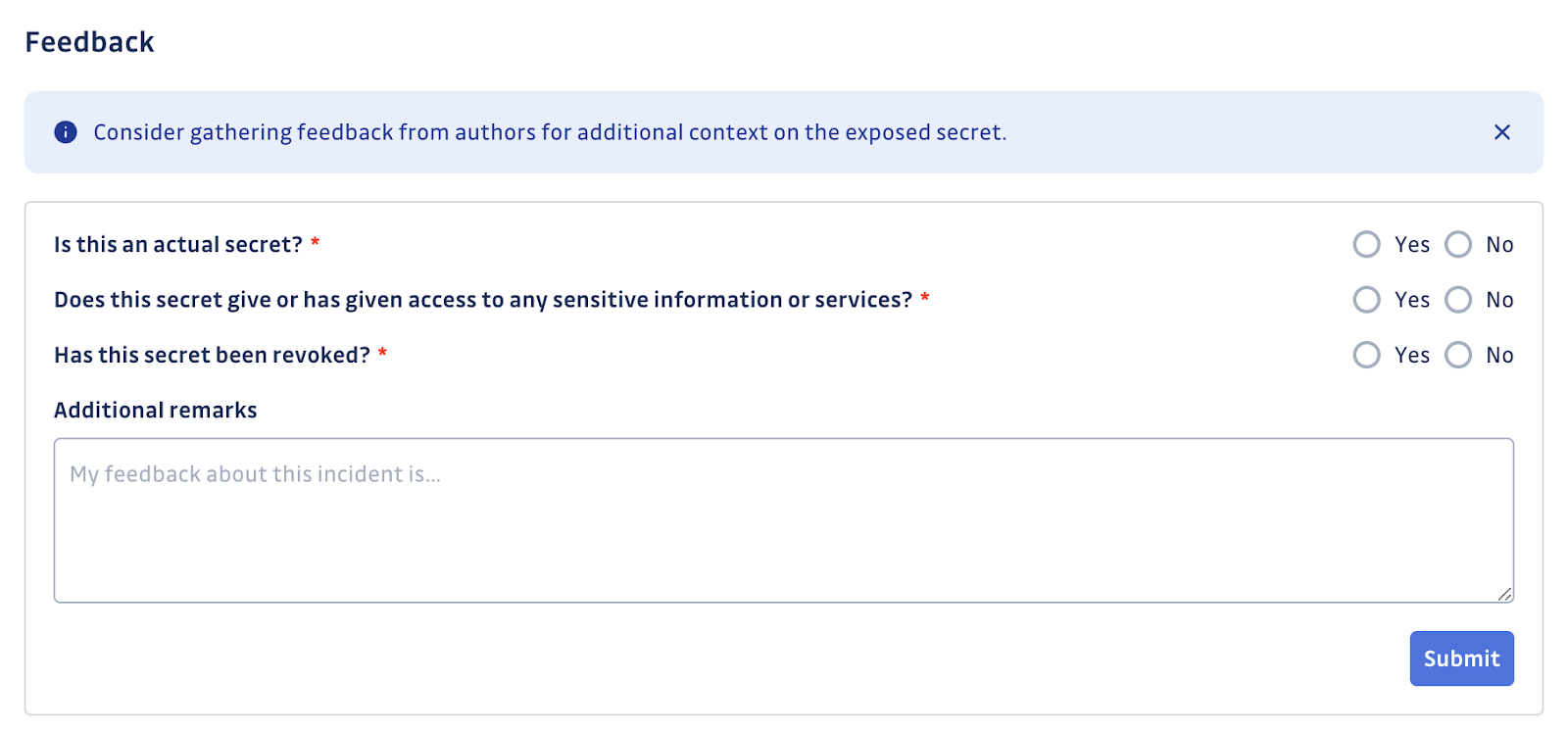
Remediation of secrets is a challenge for a number of reasons. The interconnectedness of modern DevOps means one can not simply rip out or revoke a secret once published without fear of a cascading failure event. We must gather all the needed data about the secret's validity, presence throughout the codebase, if it has been exposed publicly yet, and other vital details.
Gathering facts is a start, but you also need to get feedback directly from the team member who added the secret into the code, the developer. Each incident managed through the GitGuardan dashboard has the option to easily share the details with selected team members and gather feedback directly through the platform. Even if the developer is external to your company, the share option can accommodate this communication through the use of a temporarily public URL.
Working with larger enterprises
Even though GitGuardian makes it easy to perform a self-evaluation and even use the product for free in some situations, we know that most enterprises will require a more formal approach. We have worked with a lot of organizations to perform a Proof of Concept, POC, exercise and we are happy to share what that process looks like.
Finding your own path
Secrets sprawl is a growing problem affecting every company that writes or leverages code. It is something enterprises need to address sooner than later. Advanced secrets management maturity is needed by companies handling sensitive, mission-critical data, requiring addressing the problem of secrets storage and proper use with dedicated secrets managers like Vault by Hashicorp or CyberArk, as well as detecting and remediating secret leaks at scale.
It might be tempting to think, 'I can just write some regular expression' to address the issue. We have heard from many customers that when it comes down to "build versus buy" for secrets sprawl, the overhead and magnitude of what is needed often becomes overwhelming rather quickly. But you don't have to just take our word for it. Check out the many, many reviews and testimonials about GitGuardian from our users.
No matter where you are on your security journey, GitGuardian is here to help you get a handle on secrets sprawl. While we encourage you to do your own investigation of our platform, we are also ready to help you navigate this subject. Reach out today and schedule a demo and start down the path towards peace of mind when it comes to knowing where your secrets are.








