GitHub’s new Actions security roadmap is a sign that the industry has finally accepted something many defenders have been saying for years: CI/CD is no longer a convenience layer. It is production and identity infrastructure, and it's secret-bearing. When it is compromised, the attacker does not just get a build. They get a path into source code, publishing systems, cloud environments, and the trust chain behind software delivery, as we have seen with several recent attacks.
In publishing their roadmap, GitHub is not describing minor hardening around the edges. It is describing a structural shift in how Actions will work. The platform is moving toward deterministic workflow dependencies, centralized execution policy, tighter secret scoping, better telemetry, and native outbound network controls for hosted runners. Those changes point in the same direction: less ambient trust, fewer implicit permissions, and more infrastructure-level control over what automation can do.
Most organizations are still operating in the messy reality where their workflows are already live, with their secrets already distributed across repositories, CI systems, collaboration platforms, registries, and cloud tooling. Their reusable workflows already reflect years of convenience decisions. Their response plans are already being tested by supply chain incidents that move faster than most governance programs.
GitHub is building toward a safer actions platform. In the meantime, teams still need visibility, detection, and remediation for the environment they have today.
Changing The Trust Model
For a long time, GitHub Actions security has relied heavily on teams getting the YAML right. Pin your actions and avoid risky triggers. Be careful with pull_request_target while you scope your secrets tightly. Review your reusable workflows and protect your runners. All of that guidance still matters, but it has always placed a lot of burden on local workflow authors. The roadmap shows GitHub moving that burden upward into the platform itself.
One of the clearest examples is dependency locking for workflows. GitHub plans to add a dependencies section so workflows can lock direct and transitive dependencies to specific commit SHAs, with verification before jobs execute. That turns Actions dependencies into something closer to a managed dependency graph than a loose set of runtime references. It means teams can review changes in pull requests, reduce exposure to tag mutation, and make execution more deterministic. That is a real shift in control.
Recent supply chain attacks have repeatedly shown how dangerous mutable trust can be. A workflow that references an action by tag is convenient, but it's also a place where trust can drift. A platform that resolves dependencies at runtime is flexible. It also makes it harder to prove exactly what ran and why. GitHub’s roadmap effectively admits that convenience-first CI/CD needs stronger guardrails to hold up against modern attacker behavior.
Execution policy is becoming a first-class control
Another major change is workflow execution protections built on GitHub rulesets. This is one of the most important items in the roadmap because many CI/CD incidents are not about one dramatic bug. They are about context collapse. The wrong actor triggers the wrong workflow on the wrong event, and suddenly, an untrusted path gains access to trusted capabilities.
GitHub’s planned controls let organizations define who can trigger workflows and which events are permitted, with organization-level policy instead of per-file guesswork. That means security teams can set boundaries around things like workflow_dispatch, push, and pull_request, and evaluate those policies before enforcement. It is a much more mature model than asking every repository maintainer to reason perfectly about workflow trust boundaries in isolation.
This is the platform catching up to reality. CI/CD risk is governance risk. It is not just syntax risk.
Secrets are being treated as contextual assets instead of shared utilities
The roadmap’s changes around secrets may be the most important operationally. GitHub plans to introduce scoped secrets so credentials can be bound more precisely to repositories, branches, environments, workflow identities, and trusted reusable workflows. Secret management will no longer automatically ride along with repository write access. That function is being separated into a distinct administrative responsibility.
This means GitHub is moving away from a model where secrets are broadly available within a repository context and toward one where access is conditional on the execution context and trust boundaries. That reduces blast radius. It also reflects a broader truth in modern software delivery: a secret is never just a string. It represents access, authority, and potential lateral movement. Once it leaves its intended lane, the problem is no longer limited to CI.
This is exactly why the current transition period matters so much. Better secret scoping inside Actions will help when it lands. It will not clean up the existing sprawl of tokens, API keys, service credentials, and cloud secrets already scattered across the rest of the development environment.
The near-term gap is not theoretical
GitHub’s roadmap addresses a real pattern. The company’s own recent writing on supply chain security points directly to attacks that focused on secret exfiltration and unauthorized publishing, including incidents involving tj-actions/changed-files, Nx, and trivy-action. The pattern is familiar: attackers compromise the automation layer, harvest credentials, and then use those credentials to expand access and impact.
The real question for defenders right now is, "While these new Actions controls are being built and rolled out, how do you reduce risk in the environment you already have?"
This is where GitGuardian can help teams of any size.
GitGuardian helps with the environment teams actually have today
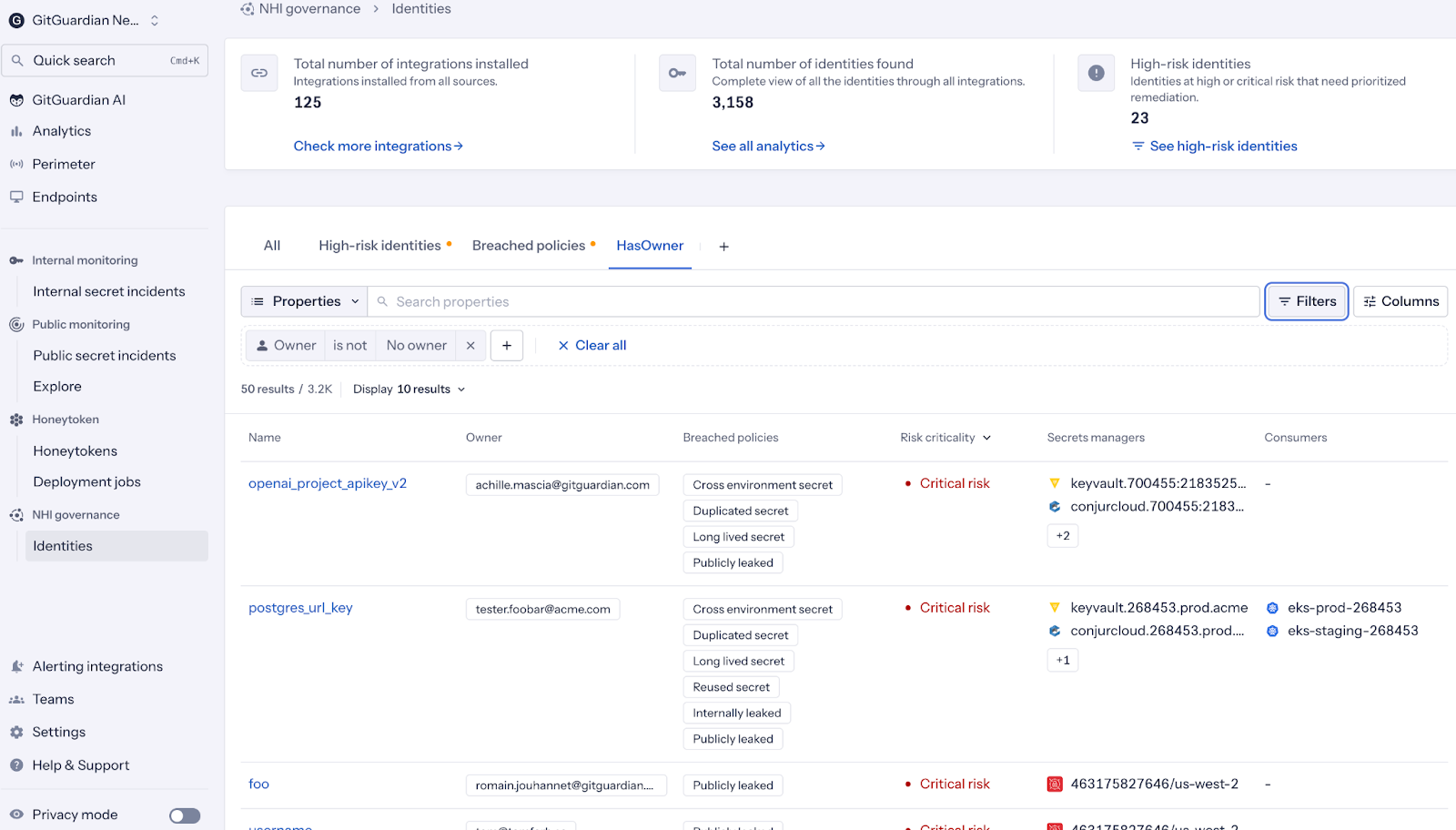
GitGuardian’s Secrets Security and NHI Governance platform is built on the fact that secret exposure is rarely confined to a single repository or control plane. The platform scans across a broad set of internal sources where credentials may appear, including version control systems, container registries, documentation platforms, messaging systems, package registries, and other connected systems. It is critical to think past the Git repo and to consider anywhere an attacker is looking, including the developers' local machines.
GitHub’s roadmap improves one critical layer, but most real-world secret exposure is already spread across multiple layers. A leaked token may start in code, then show up in CI logs, then be pasted into a ticket, then remain duplicated in a collaboration thread, then persist in a registry artifact or a stale secret manager path. Security teams do not need a narrow answer to a broad problem. They need a way to find the credential wherever it traveled.
GitGuardian gives teams a wider view, while GitHub is still building the next generation of platform controls.
Detection and remediation still matter even when prevention improves
One of the quiet assumptions behind many security roadmap discussions is that a better platform eventually removes the need for as much downstream cleanup. That is never really how these transitions work.
Better prevention changes the rate of new incidents. It does not automatically resolve the backlog of existing exposure, nor does it remove the need for fast incident response during active compromise.
GitGuardian is valuable for teams because it supports both detection and automated remediation. The platform's broader workflow is built around investigating incidents, validating risk, assigning ownership, and driving remediation. The platform's posture model is centered on protecting, detecting, remediation, and prevention. This is a useful reflection of the real work teams have to do after a secret is exposed.
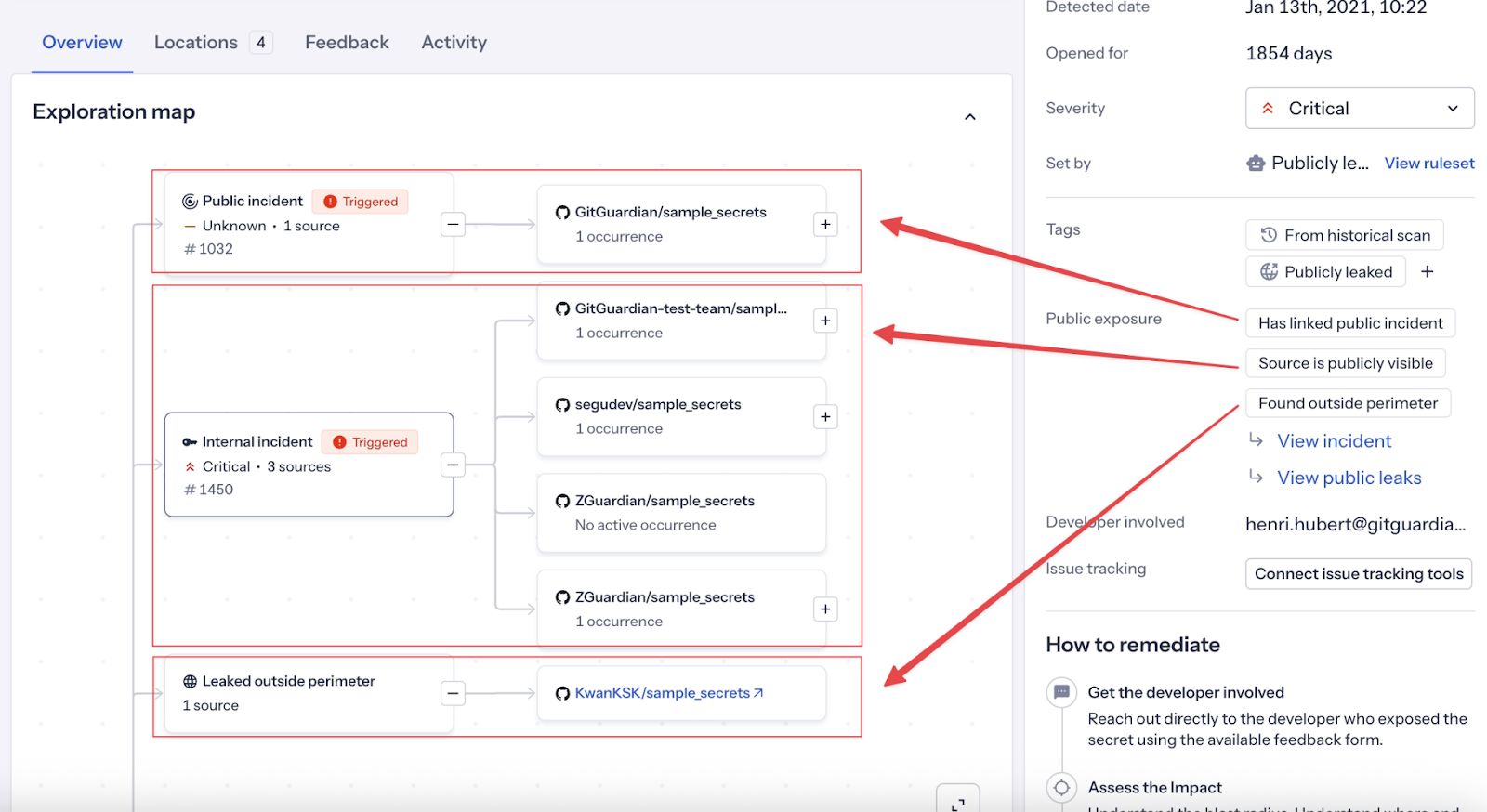
That workflow becomes even more useful during supply chain incidents, where the central problem is often not just that code was tampered with, but that credentials may already have been harvested, reused, or staged for later abuse.
Honeytokens fit the current moment especially well
GitHub also plans to improve observability with an Actions Data Stream and, later, a native egress firewall for GitHub-hosted runners. Both are strong signals that CI/CD visibility is becoming part of mainstream platform security. But again, those are roadmap items.
If you need an earlier warning system in the meantime, GitGuardian Honeytoken is here to help. Honeytokens are a way to generate decoy credentials and track unauthorized usage, with a specific emphasis on DevOps pipeline security and supply chain attack detection. The core concept is straightforward: place monitored fake credentials where an attacker searching for real ones is likely to find them, then alert when those credentials are touched.
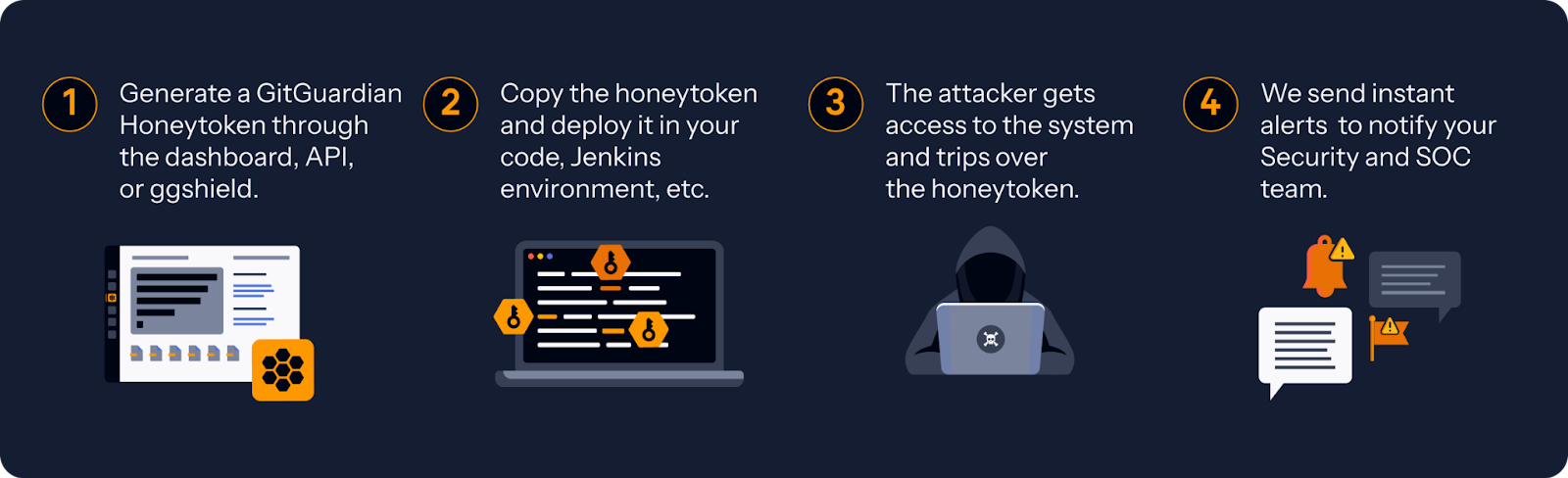
That makes sense in the exact environment GitHub is trying to harden. Attackers who compromise build and automation systems often go hunting for secrets very early. A honeytoken gives defenders a chance to detect that behavior before the attacker has turned a workflow compromise into something larger. It is not a substitute for runner telemetry, execution policy, or scoped secrets. It is an immediate control that fits the current exposure pattern.
A Governance Story About Non-human Identities
Software delivery systems are now full of non-human identities making privileged decisions. Workflows authenticate to APIs. Actions call cloud services. Build systems publish artifacts. Bots trigger pipelines. Reusable workflows inherit trust from one repository to another. All of that adds up to a dense machine-to-machine access environment, and much of it is still mediated by secrets.
GitHub is improving that environment from the platform side. GitGuardian helps organizations govern the credentials that make it work from the exposure side.
That is an important distinction. GitHub is tightening the lanes in which Actions can operate. GitGuardian NHI Governance helps organizations discover where the keys to those lanes already lie, who owns them, where they have spread, and what needs to be fixed first.
What Changes Now For Defenders
The main takeaway from GitHub’s 2026 Actions security roadmap is that CI/CD security is becoming more explicit, more policy-driven, and more infrastructure-aware. That is the right direction. Deterministic dependencies, scoped secrets, execution protections, telemetry streams, and outbound network controls all reflect a more mature model for securing automation.
But the immediate defender takeaway is even simpler.
You do not need to wait for the roadmap to become generally available to start reducing risk.
- You can reduce the ambient spread of secrets now.
- You can monitor the broader internal ecosystem now.
- You can tighten remediation around exposed credentials now.
- You can place early warning tripwires for attacker behavior now.
That is where GitGuardian fits in this transition. GitHub is building a safer future state for Actions. GitGuardian helps security teams operate safely in the current state, where secrets are already distributed, workflows are already trusted, and attackers are already treating CI/CD as a high-value target.