A helpful glossary of common terms and definitions used in DevSecOps explained with amusing comics.
We are constantly adding comics and terms so if you have an idea, please be sure to email me at mackenzie.jackson@gitguardian.com. Thanks to @sebiwicb for allowing us to use some great comics!
CI/CD Definition
CI/CD stands for continuous integration and continuous deployment.
Continuous integration is a software development practice where developers regularly merge their code changes into a central repository, after which automated builds and tests are run. Continuous delivery is a software development practice where code changes are automatically built, tested, and prepared for a release to production.

Data Breach Definition
A data breach is referring to an incident where information is stolen or released from a system without authorization. An example of a data breach could be if an unauthorized user gains access to a database or if data is published, accidentally or intentionally, to an unsecure location that can be viewed by unauthorized persons.

DevOps Definition
DevOps is the combination of both software development (dev) and IT operations (ops). Merging the two disciplines together brings IT operations into consideration earlier and throughout the entire software development life cycle. The goal of DevOps is to shorten the development process and provide continuous delivery with high software quality and is usually implemented within agile software development.
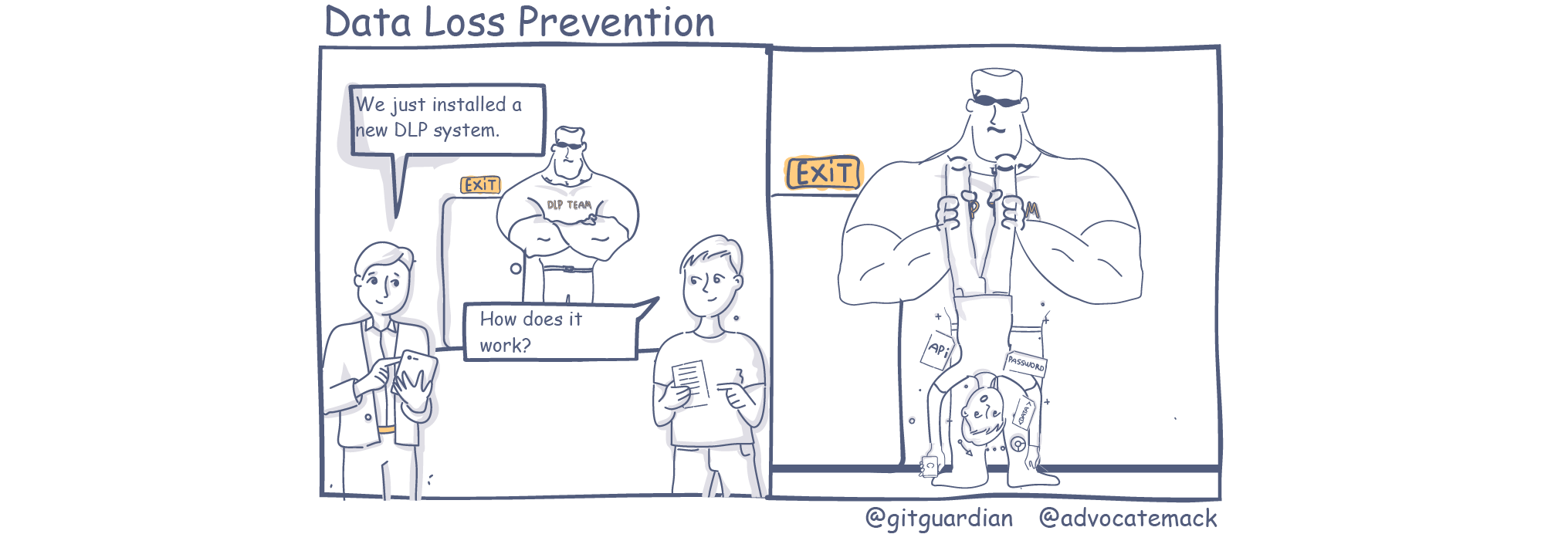
DLP Definition
DLP or data loss prevention refers to tools and methodologies that can detect any potential data breaches and prevents them by monitoring, detecting and blocking sensitive data while in use, in motion, and at rest. Data loss, data leak and data breach are commonly used synonymously.
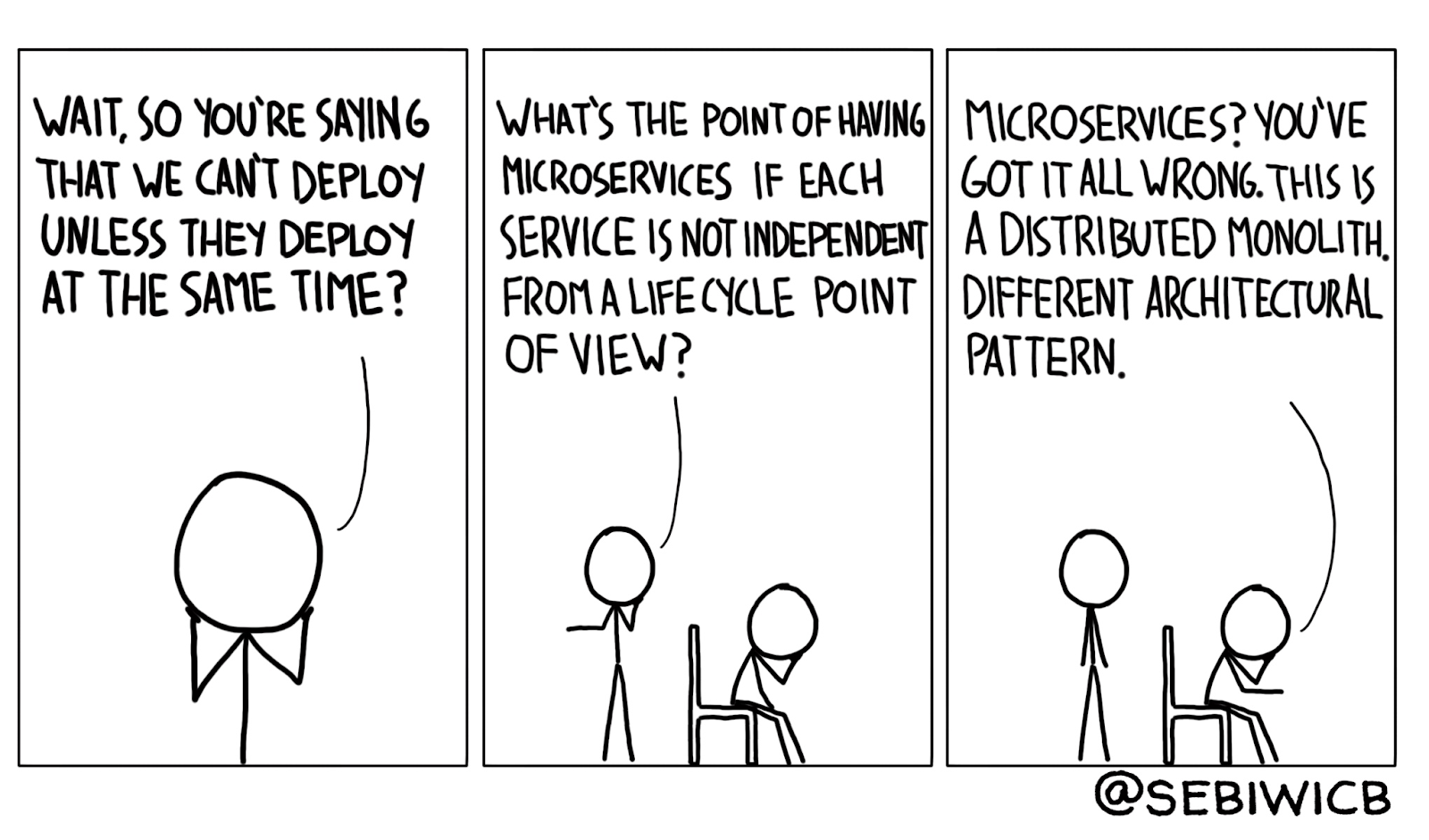
Microservices Definition
A microservice refers to a form of software architecture that uses a number of small (micro) individual services that link together to make a single application. Each service runs independently and communicates with other services typically through an application programming interface (API). There are many advantages in using this architecture including the ability to: independently deploy each service, use multiple frameworks and languages and easily use existing external services.
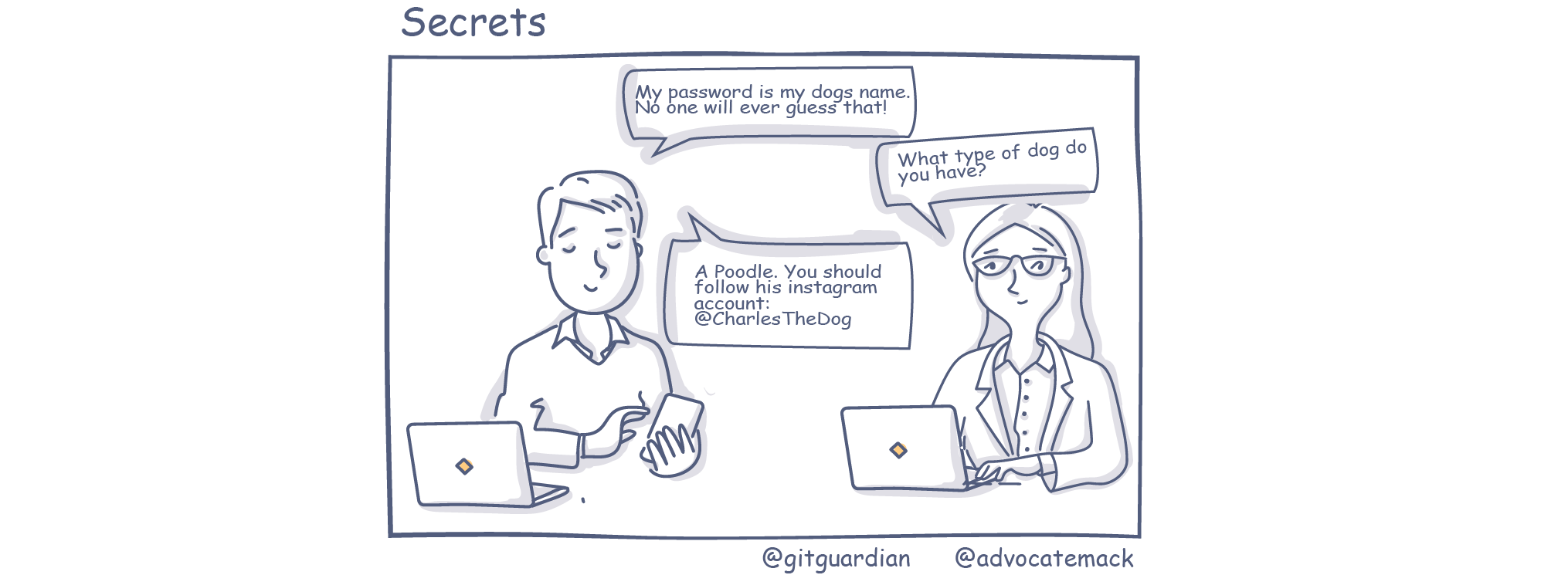
Secrets Definition
In software development, the term secrets is used to refer to digital authentication credentials. Credentials that authenticate a user or system to access any external or internal service, data or application. Commonly used secrets are usernames and passwords, API tokens, security certificates and database URIs.

Secrets Management Definition
Secrets management refers to tools and methods that are used to store, distribute and rotate secrets such as API tokens, security certificates and credentials. Secrets management is designed to provide assurance that secrets can only be accessed by authenticated users and remain in a tightly controlled central location.
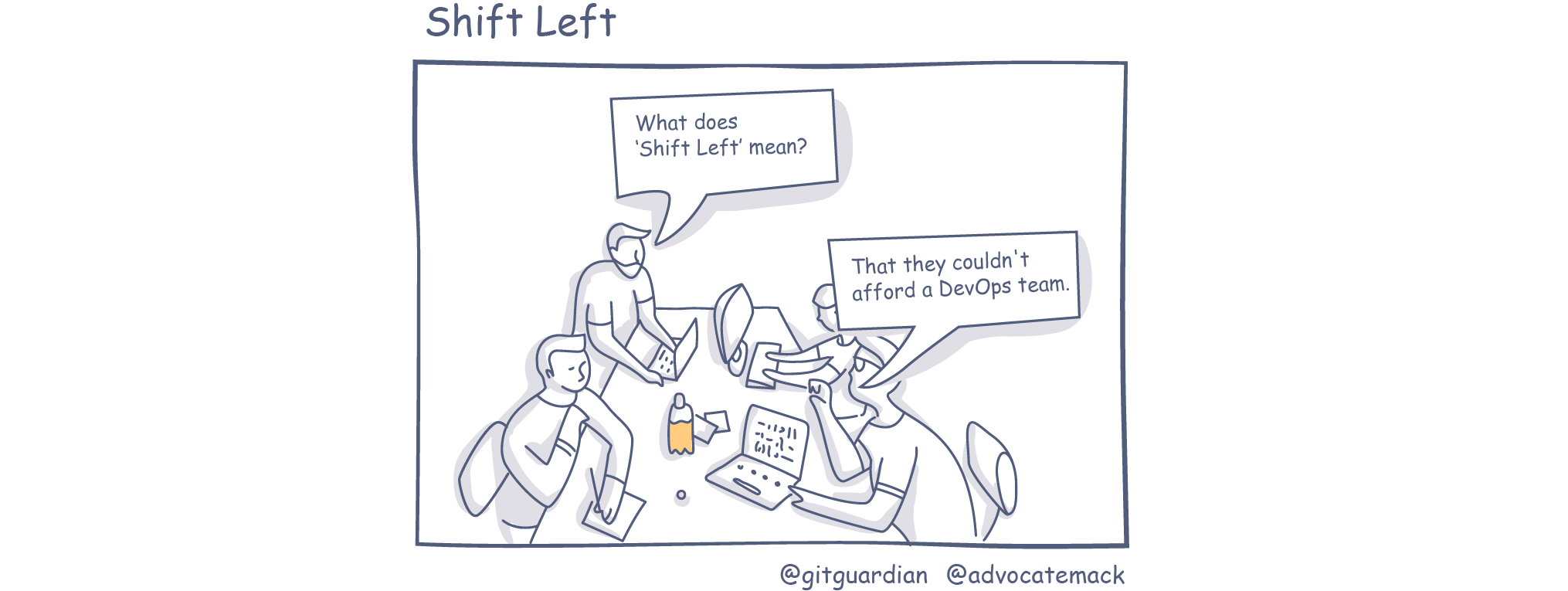
Shift Left Definition
Shift-left testing is an approach to software testing and system testing in which testing is performed earlier in the life cycle. It is the first half of the maxim "Test early and often." It was coined by Larry Smith in 2001. The methodology supports the early collaboration of security teams while encouraging developers to take ownership of security becoming part of the security process.
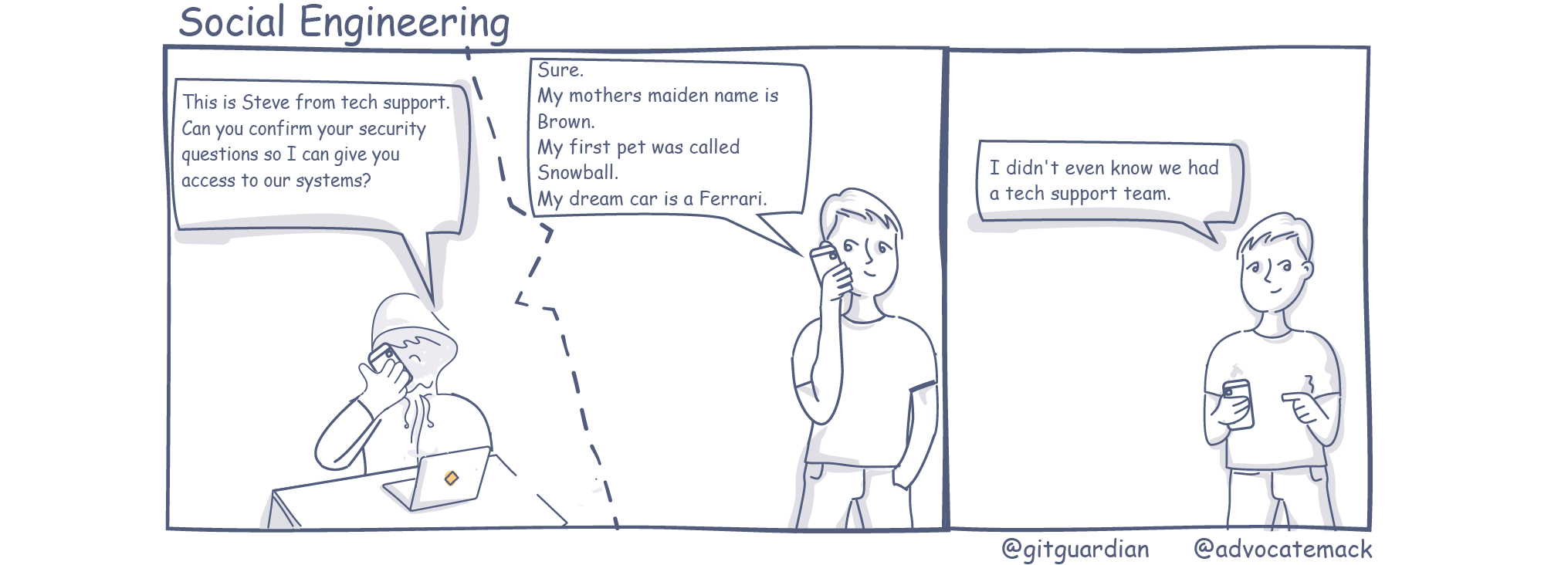
Social Engineering Definition
Social engineering in cyber security refers to the psychological manipulation of people into performing actions or to reveal sensitive information that can be used by a bad actor or hacker to gain access to sensitive information or services. An example of social engineering is impersonating a team member to trick an employee into divulging company credentials.
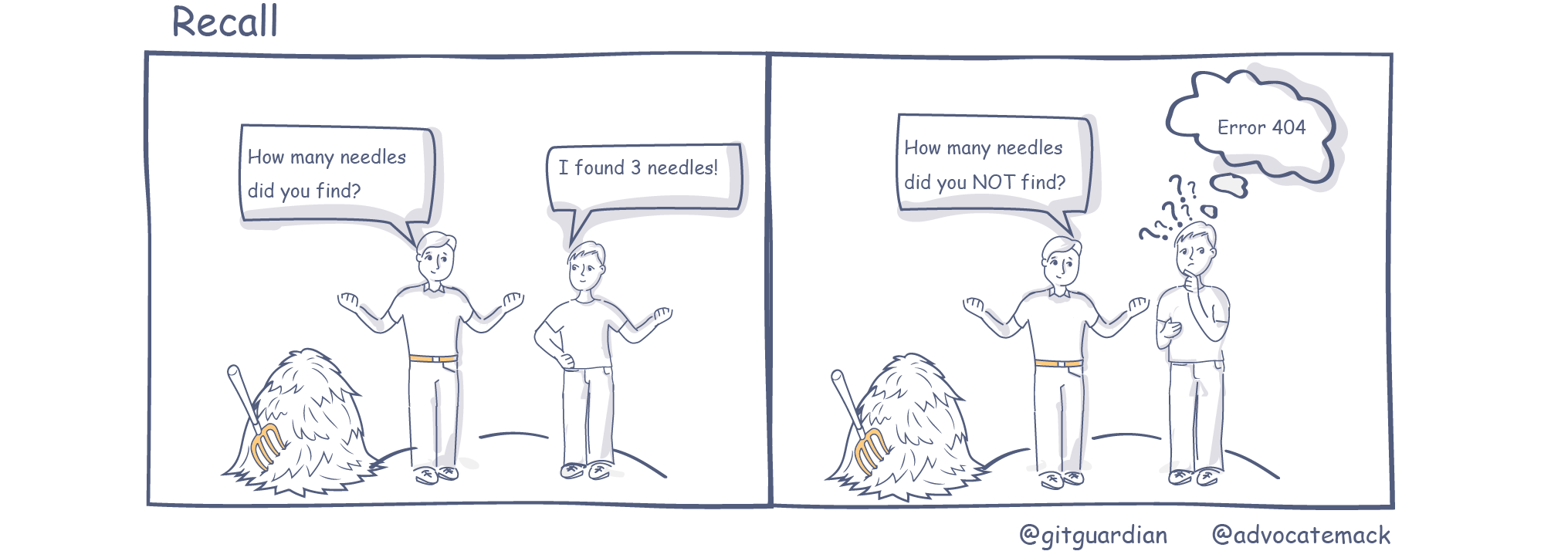
Recall Definition
Recall is a common indicator used to evaluate the performance of classification algorithms, often alongside precision. Precision and recall metrics answer two very different questions:
Precision: looking at all the needles that you were able to find in the haystack, what percentage are actually needles?
Recall: among all the needles that were to be found, what percentage of needles did you find?
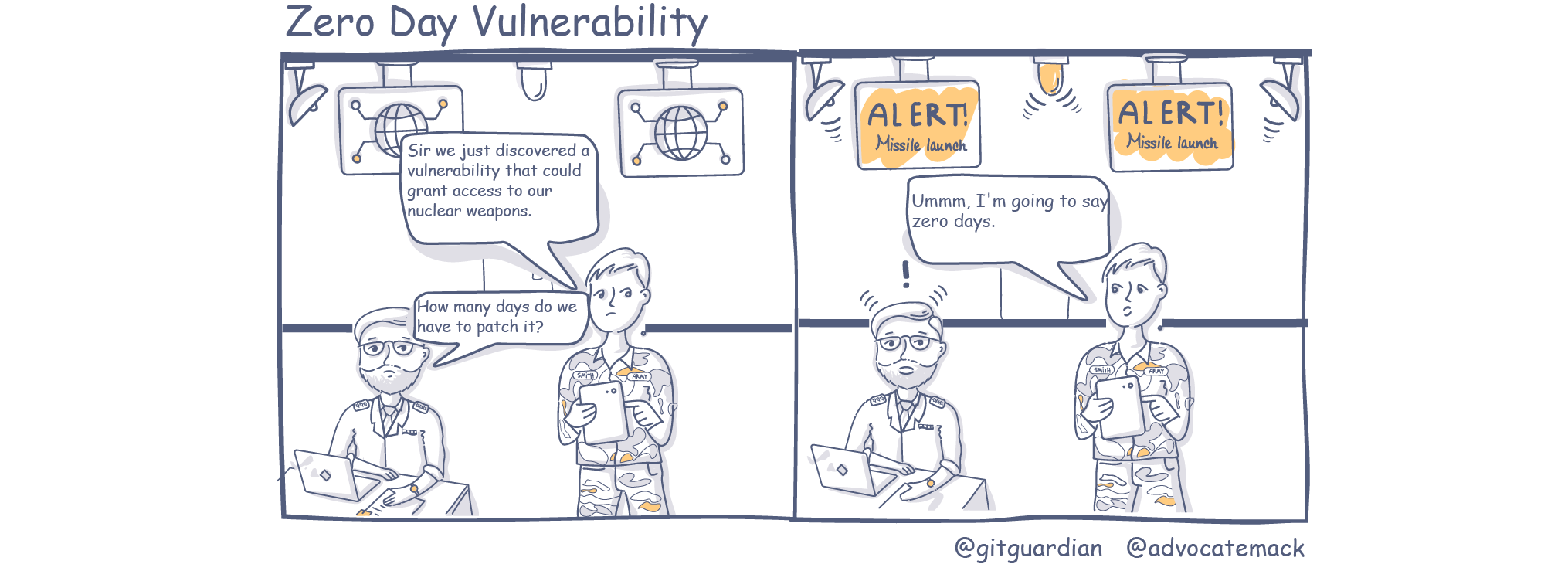
Zero Day Vulnerability Definition
A zero day risk or zero day vulnerability is a flaw inside software, firmware or hardware that is currently unknown to responsible parties. ‘Zero day’ refers to the number of days or time between being made aware of the vulnerability and someone launching an attack.
If you want to learn more on DevOps, DevSecOps, Secrets, Shift left and other cybersecurity concepts, visit our Learning Center
Have a comic or idea for a comic? Drop me an email and we will include it and credit you. mackenzie@gitguardian.com