
The Future Of GitHub Actions Security And What You Can Do Right Now
GitHub is hardening Actions with deterministic dependencies, scoped secrets, and policy controls. Teams still need immediate detection and remediation for today’s risk.

GitHub is hardening Actions with deterministic dependencies, scoped secrets, and policy controls. Teams still need immediate detection and remediation for today’s risk.
Plaintext secrets on developer machines create real supply chain risk. Honeytokens provide early detection while stronger identity-based controls are rolled out.

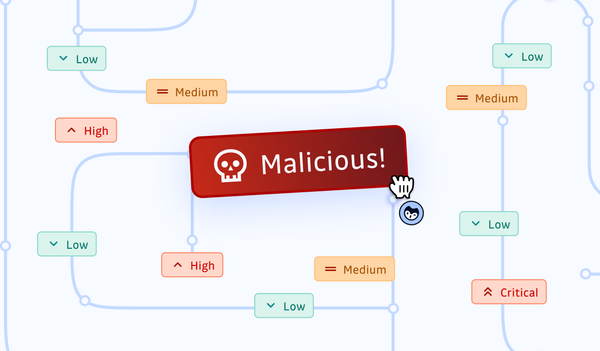
On September 5, 2025, GitGuardian discovered GhostAction, a massive supply chain attack affecting 327 GitHub users across 817 repositories. Attackers injected malicious workflows that exfiltrated 3,325 secrets, including PyPI, npm, and DockerHub tokens via HTTP POST requests to a remote endpoint.
Dependency confusion attacks exploit gaps in your software supply chain. Dive into modern dependency management and learn how to defend your systems with best practices.
This month we dive into CVE-2024-27198 for JetBrains TeamCity and the controversy surrounding the patching process that contributed to it being exploited in the wild.
SBOMs are security analysis artifacts becoming required by more companies due to internal policies and government regulation. If you sell or buy software, you should know the what, why, and how of the SBOM.
The open-source world narrowly escaped a sophisticated supply-chain attack that could have compromised countless systems. A stark reminder of the necessity of vigilant monitoring and rigorous vetting within the open-source ecosystem to maintain trust and security.

...despite all intentions to follow best practices, they don't. When you automate enforcement of best practices, you can ensure those practices are followed...

Discover how honeytokens enhance security by detecting breaches in real-time across the software development lifecycle. Learn how to deploy these decoy credentials and traps effectively, bolstering defenses against cyber threats.

Let's walk through nine of the top secrets management solutions for 2024.
Security Researcher Tom Forbes worked with the GitGuardian team to analyze all the code committed to PyPi packages and surfaced thousands of hardcoded credentials.

A condensed recap of our hands-on runtime security webinar from September. Get the juiciest knowledge nuggets and pointers to more.