Honeytokens can be an effective way to detect and stop black hat hackers. When strategically placed in datasets, these fake records are impossible for an attacker to differentiate from real data. Once interacted with, honeytokens trigger alerts, revealing malicious activity before real damage can be done. Let's learn how honeytokens can strengthen your cybersecurity posture.
The Types of Cybercriminals
When it comes to cybercrime, most black hat computer hackers are not as sophisticated as you might think. There are generally three different types of cybercriminals:
Script kiddies - These hackers use pre-written scripts and tools created by others to carry out cyberattacks, often without fully understanding how they work. They are mostly motivated by the challenge or thrill of carrying out an attack.
Generic cybercriminals - These hackers have more technical skills and often carry out attacks for financial gain, such as stealing credit card information or bank account credentials. Their methods are more targeted than script kiddies.
State actors - These are highly skilled hackers, sometimes affiliated with or sponsored by nation-states, who carry out cyber warfare and espionage campaigns for political, economic, or military advantages.
Financial Record Checkers
In general, when data is stolen, the data type determines what happens next. If it’s financial data, it’s frequently run through something called a credit/debit card checker to ensure validation.
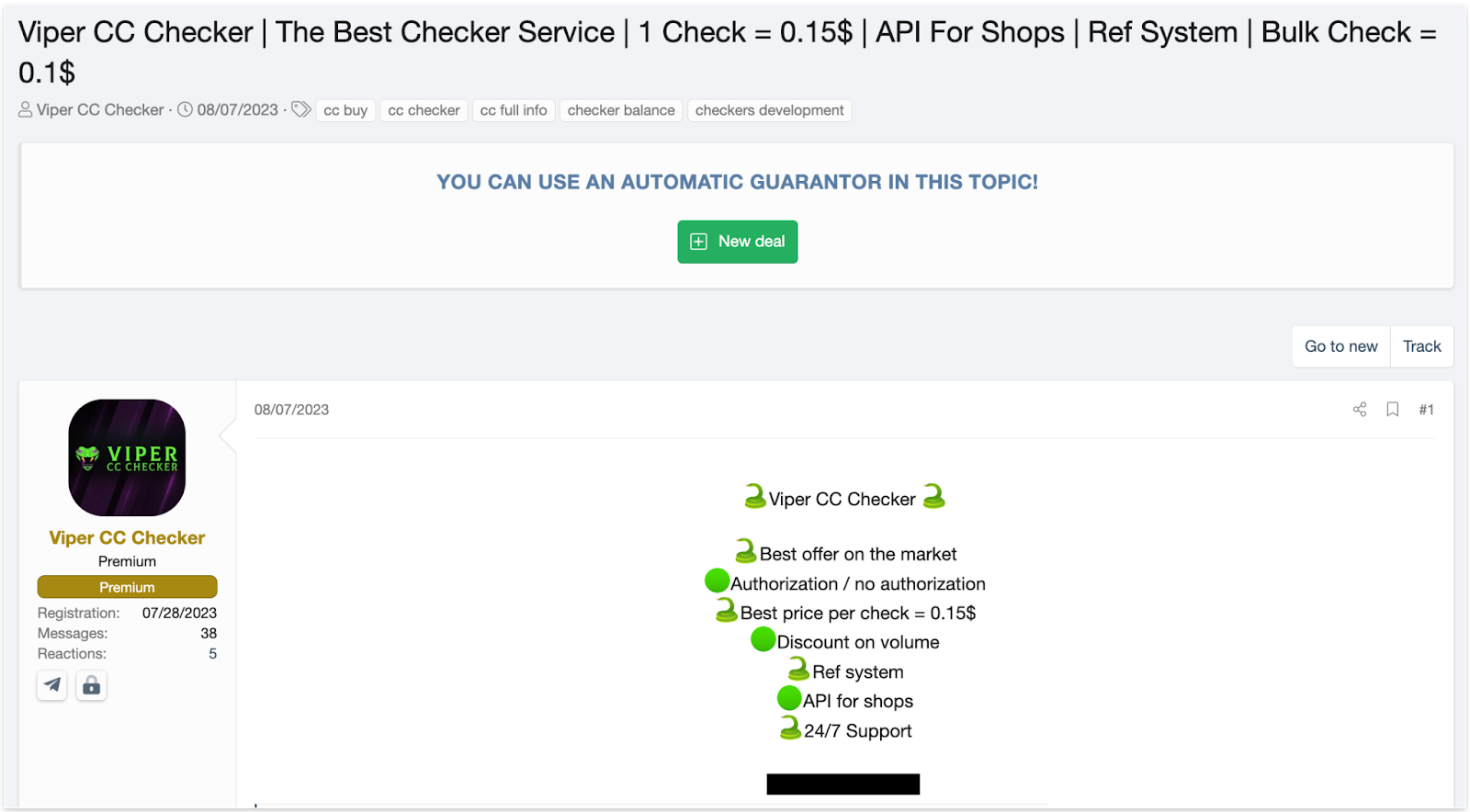
This has several advantages for attackers. To begin, not all stolen financial records are legitimate, so the checker can filter out invalid data. Secondly, when attackers compile the records and potential buyers test samples from the compilation, the original attacker's best interest is for the compilation to have a high validity rate so that potential buyers are more likely to purchase the data.
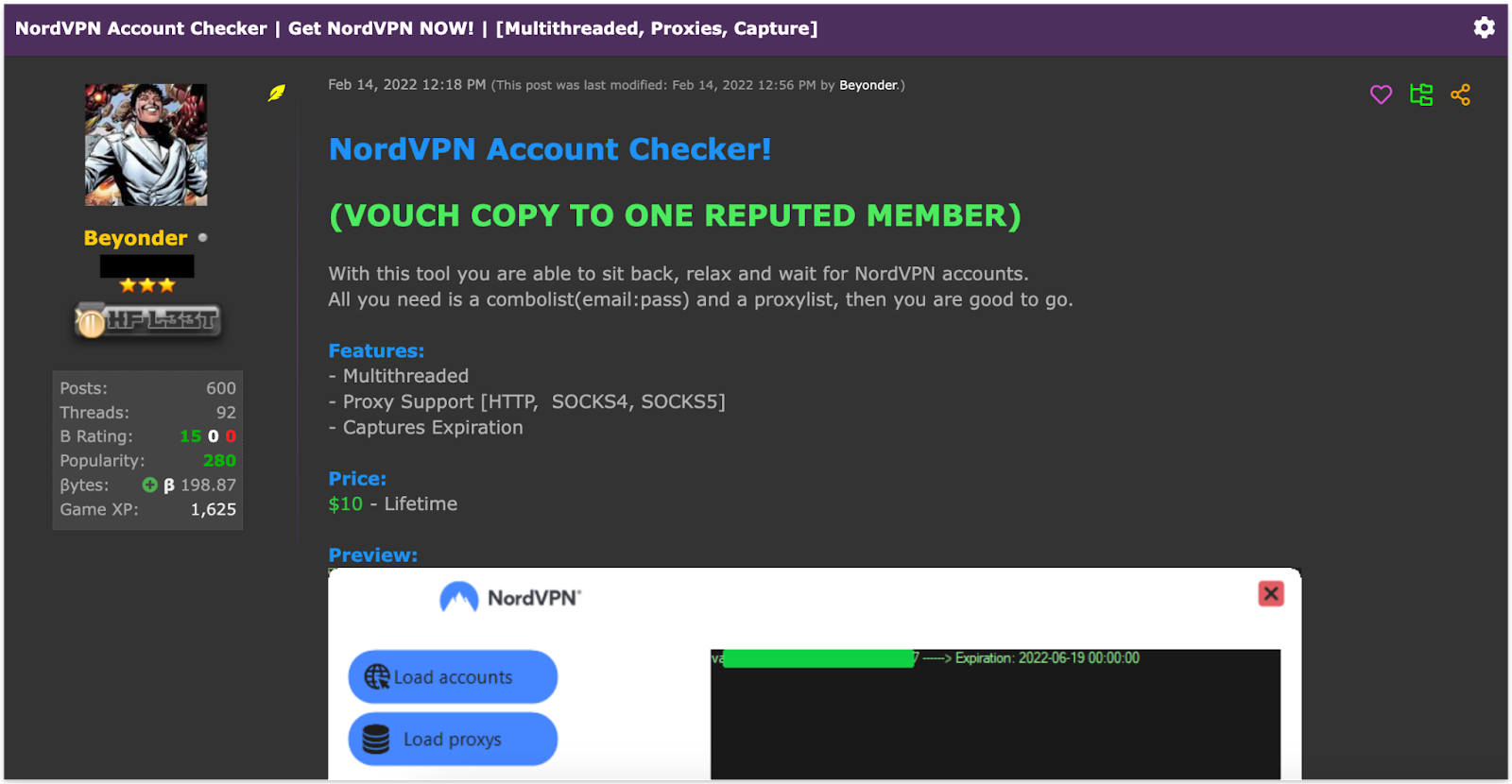
Stolen Account Checkers
Additionally, if a large number of accounts are stolen from a database, attackers will also frequently use an account checker to check the validity of the credentials.
It works by loading a list of stolen accounts into a file and then attempting to authenticate each one using a proxy list that rotates through different IP addresses to avoid blacklisting.
In all of these cases, honeytokens can greatly aid in the early detection of breaches. Because a honeytoken is indistinguishable from real data, any interaction with it will generate an alert.
Other sensitive data formats, such as API keys, can also be stolen by hackers. Attackers cannot determine whether stolen API keys are valid unless they interact with them in some way.
A decoy API key planted as a honeytoken, just like stolen credentials or financial data, would notify the system owner if used by an attacker, allowing for early detection of a breach.
Honeytokens for Attribution
Another key benefit of honeytokens is the enablement of attribution of attacks. When a honeytoken is accessed or used by an attacker, forensic analysis can reveal important details about the threat actor responsible.
For example, if credentials to a fake user account are leaked and then used by an attacker, the activity can be traced back to reveal the attacker's IP address, geographic location, hosting providers, and other identifiable digital fingerprints.
Honeytokens in places like dark web marketplaces and hacking forums can also trace attacks back to their source. Blue teamers can register accounts and monitor these communities to track their planted honeytokens. The actors advertising or selling the honeytokens expose details about themselves in the process.
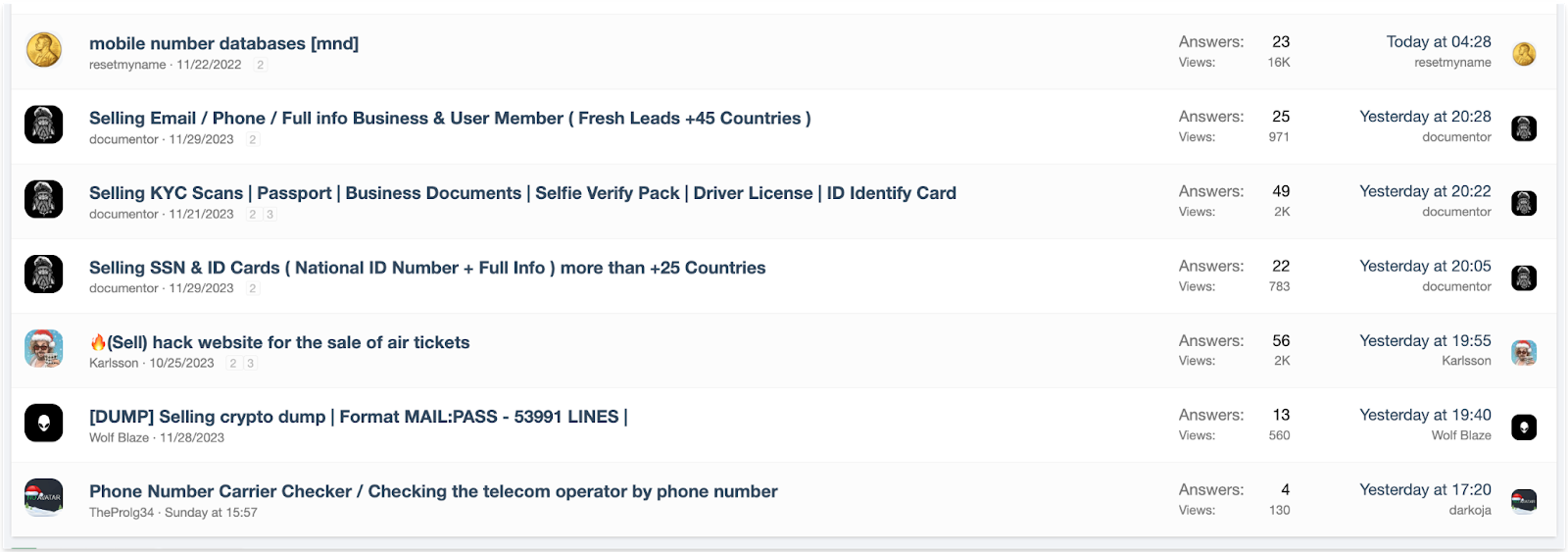
By piecing together attribution clues from various honeytoken interactions, security teams can build up intelligence on threat groups, hacking campaigns, and the tactics and techniques of bad actors.
Attribution enables more informed defense planning and the ability to share threat intelligence with other organizations. It also supports legal action against attackers when possible. The convincing forensic evidence honeytokens provide is useful for law enforcement investigations and prosecutions.
Next Steps With GitGuardian
GitGuardian is actively working towards an automated honeytoken deployment system. This upcoming feature will empower organizations to seamlessly integrate honeytokens into their security strategy, strengthening their defenses without added complexity or manual effort.
Learn more about this honeytoken technology.
This article is a guest post. Views and opinions expressed in this publication are solely those of the author and do not reflect the official policy, position, or views of GitGuardian, The content is provided for informational purposes, GitGuardian assumes no responsibility for any errors, omissions, or outcomes resulting from the use of this information. Should you have any enquiry with regard to the content, please contact the author directly.









