The State of Secrets Sprawl 2024
The State of Secrets Sprawl 2024 report by GitGuardian uncovers a 28% increase in leaked secrets on GitHub, revealing an urgent need for significantly improved security practices.
The State of Secrets Sprawl 2024 report by GitGuardian uncovers a 28% increase in leaked secrets on GitHub, revealing an urgent need for significantly improved security practices.

The healthcare industry, holding a treasure trove of valuable data, finds itself at a pivotal point in its fight against cyber threats. This sector, harassed by cybercriminals, has endured the highest average costs due to breaches for over a decade.

Cloudflare experienced a security breach when its internal systems were compromised, leading to unauthorized access to sensitive data. Another incident highlights the importance of maintaining strict secrets security across the supply chain.
Discover Arnault's journey as lead ML engineer at GitGuardian, tackling complex data science challenges and secrets management in cybersecurity.
![Has My Secret Leaked? [Security Zines]](/content/images/size/w600/2024/01/Security-Z.png)
A new comic strip to better grasp the simple but effective way HasMySecretLeaked checks your secrets without asking you to reveal them!

Kubernetes Service Account tokens are exploited in many attack chain scenarios. Learn how to mitigate these risks and secure your Kubernetes clusters effectively.
Tired of the AI hype? We get it. Our latest blog takes a no-nonsense look at AI in 2024's cybersecurity – just the facts and some thoughtful insights. No earth-shattering revelations, just a decent read for your coffee break.

Discover the inner workings of the recently implemented Cyber Resilience Act (CRA) in the EU and explore why this framework has raised concerns about jeopardizing the open-source ecosystem. Join us in our latest blog post to delve into this important topic.
Learn how to enhance secrets manager security with GitGuardian Honeytoken. Strengthen your system's security and protect your critical assets effectively.
Discover how an overprovisioned SAS token exposed a massive 38TB trove of private data on GitHub for nearly three years. Learn about the misconfiguration, security risks, and mitigation strategies to protect your sensitive assets.
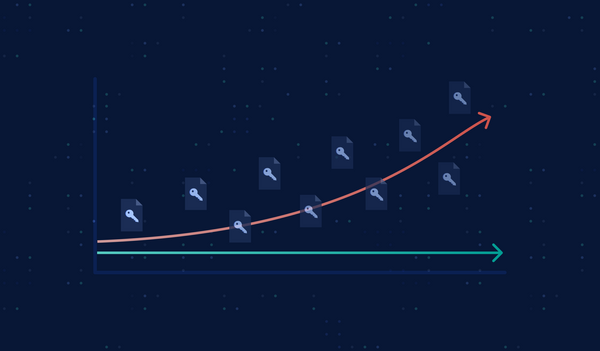
The figures are precise: stolen credentials remain the most common cause of a data breach. So how are there still thousands of hardcoded secrets hiding in source code, CI/CD pipelines, or Docker images, and, more importantly, how should we deal with them?
![From Code to Cloud: Security for Developers [cheat sheet included]](/content/images/size/w600/2023/08/Snyk-GitGuardian-Cheat-sheet.png)
In this cheat sheet, we will walk you through the different stages of the software development lifecycle and highlight key security considerations and tools that can help you mitigate risks and protect your code.