
Four Credential-Harvesting Campaigns Hit Open Source Ecosystems in Two Weeks
The pace is not slowing down. Between May 18 and June 1, 2026, four distinct supply chain campaigns swept through npm, PyPI, Crates.io, GitHub Actions, and Composer.

The pace is not slowing down. Between May 18 and June 1, 2026, four distinct supply chain campaigns swept through npm, PyPI, Crates.io, GitHub Actions, and Composer.

GitGuardian and GuidePoint Security have partnered to deliver enhanced secrets detection and non-human identity security solutions to North American customers, offering tools to combat secrets sprawl and mismanaged identities.

Machine identities make up the majority of the over 24 million secrets GitGuardian discovered in public in 2025. Let's look at how we got here and how we fix this.
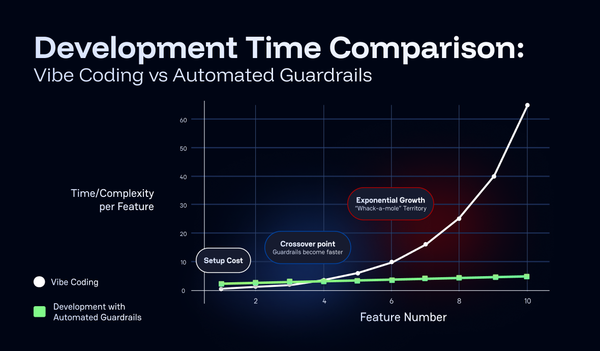
Vibe coding might sound like a trendy term, but it's really just developing software without automated checks and quality gates. Traditional engineering disciplines have always relied on safety measures and quality controls, so vibe coding should be no different in my honest opinion.

Identiverse 2025 exposed the urgent need for NHI governance. From AI agents to orphaned credentials, NHIs and their sprawling secrets are today’s most overlooked risks.

See how GitGuardian's deep discovery, combined with Akeyless's automation, delivers full secrets lifecycle control.

Our latest State of Secrets Sprawl 2025 research reveals a troubling reality: the majority of leaked corporate secrets found in public code repositories continue to provide access to systems for years after their discovery.

At BSides312 in Chicago, experts showed that defending systems requires defending people, with trust, inclusion, and communication as key controls. Defense is deeply human.

From entering passwords with getpass to using secret managers like AWS Secrets Manager, this guide covers best practices for protecting sensitive information in your notebooks.
PHP TEK 2025 revealed how empowering developers through clear, embedded security practices strengthens defenses without adding operational friction.
How I wrapped large-language-model power in a safety blanket of secrets-detection, chunking, and serverless scale.

Discover why machine identities are the new security frontier from KuppingerCole EIC 2025. Learn about secrets sprawl, AI agents, and why traditional IAM fails to protect NHIs in this GitGuardian recap.

Discover how SPICE, WIMSE, and SCITT are redefining workload identity, digital trust, and software supply chain integrity in modern machine-first environments.