
Designing Identity for the Agentic Enterprise: The Okta AI Identity Summit
Speakers made it clear that agentic AI is already operating across enterprise workflows. Learn why identity must govern ownership, permissions, actions, and accountability.

Speakers made it clear that agentic AI is already operating across enterprise workflows. Learn why identity must govern ownership, permissions, actions, and accountability.

Explore highlights from DevOpsDays Birmingham 2024, featuring workshops, sessions, and community-driven discussions on empowering teams and doing it securely.
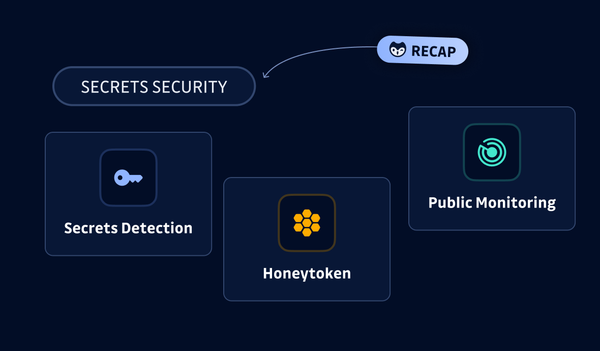
Discover how GitGuardian's latest product innovations enhance your secrets security, streamline remediation, and improve incident management for better protection of your software supply chain.

Read our key takeaways from Drupal GovCon 2024, where Drupal experts explored secure open-source solutions for U.S. government websites and collaborative tools.

SPIFFE stands for Secure Production Identity Framework for Everyone, and aims to replace single-factor access credentials with a highly scalable identity solution. This blog post provides some practical applications of SPIFFE in real-world environments.

At DEF CON 32's AppSec Village, we explored secrets security challenges, answered common questions, and shared how to detect and handle hidden credentials effectively.
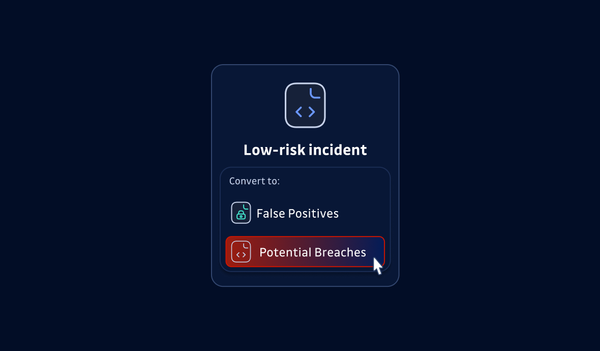
Ignoring low-risk secrets in GitGuardian? This could be a costly mistake. Learn how to avoid the hidden dangers of prematurely closing incidents.
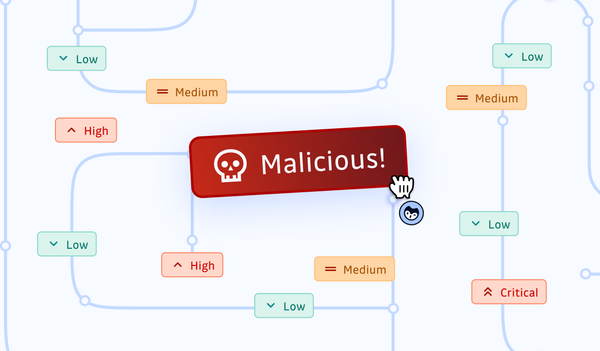
Dependency confusion attacks exploit gaps in your software supply chain. Dive into modern dependency management and learn how to defend your systems with best practices.

Experience the heat of innovation at BSides Las Vegas 2024, where cybersecurity experts tackle AI security, passwordless solutions, and zero-downtime credential rotation.

The New York Times had their entire codebase leaked. In this article we explore what was inside that code, how the leak happened and what the risk for the New York Times going forward is. (Spoiler we found thousands of secrets).
DevSecOps Engineer Gene Gotimer explains why constant software dependency updates are crucial for security in DevSecOps practices.

What does Agile have to do with improving security? A lot! Explore highlights from Agile2024, including technical health, productive meetings, and addressing shadow IT.