
Honeytokens - Protect Your Holy Grail
When protecting your SDLC, you must choose. But choose wisely. For as the True Grail will bring you life. The False Grail will take it from you.

When protecting your SDLC, you must choose. But choose wisely. For as the True Grail will bring you life. The False Grail will take it from you.

Learn the benefits of policy as code and start testing your policies for cloud-native environments.
You might already be using a Cloud IDE for certain projects. This exciting evolution of the local dev environment has a lot of advantages but also brings some new risks. This article will help you stay safe as you embrace the cloud for your coding needs.

We're happy to present you our Secrets Management Maturity Model, a model to help your organization make sense of its actual posture and how to improve it.

New research by CyberNews has revealed that there are millions of private git repositories that are, in fact, not all that private.

We’re introducing a new Role-based Access Management (RBAC) system with “Teams” in your GitGuardian Internal Monitoring workspace. Bring Dev, Sec, and Ops together and fix hardcoded credentials faster than you ever thought possible!

Learn more about what is a Software Bills Of Materials, why use it, what are the standards and how to automate it with Continuous Integration.

In this article, we’ll be going over the 1.1 revision of The Secure Software Development Framework that was published earlier this year.

In recent years, resorting to MSPs has become very popular for companies wanting to accelerate the digitization of their businesses. With this surge in popularity, MSPs now face the question: how to ensure we can meet our cybersecurity responsibilities?
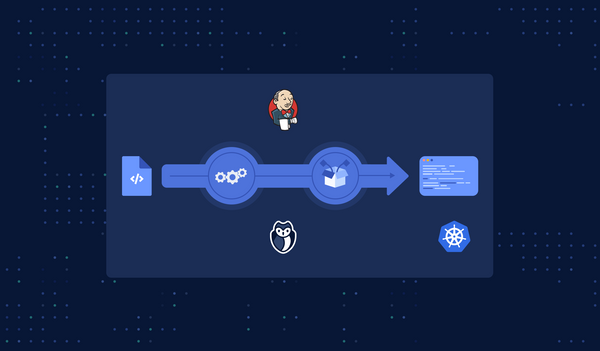
In this tutorial, we will show how to integrate GitGuardian Shield to run on one of the most famous CI tools: Jenkins (with a cool bonus!).

In their latest white paper, GitGuardian examines why implementing DevSecOps at scale to protect the modern software factory means evolving traditional AppSec. Read more to learn how the shared responsibility model adoption will unlock security in an agile world.
Infrastructure as Code is slowly but surely becoming norm for organizations that seek automation and faster delivery. Learn the big concepts powering it in this article.